 Blog's Page
Blog's Page
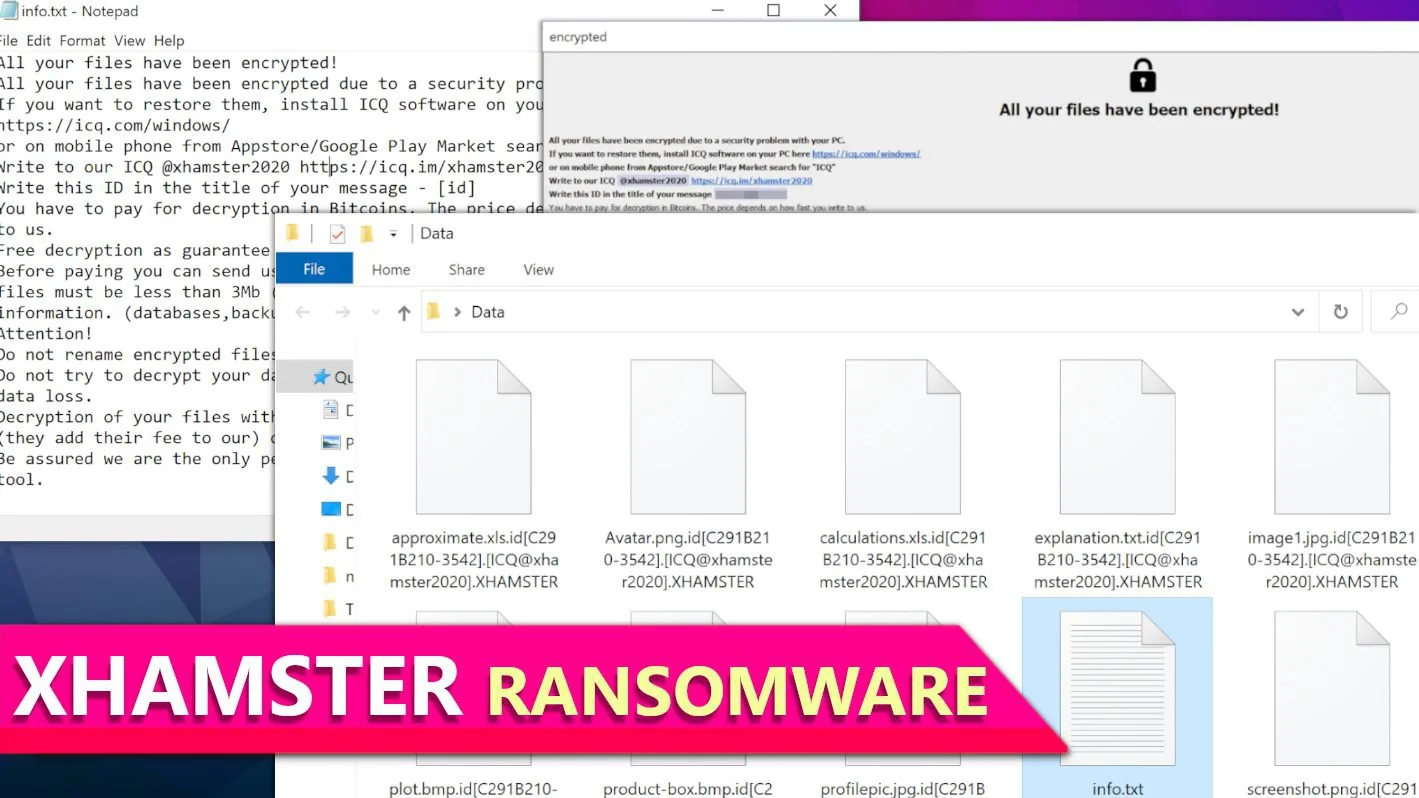
Cybercriminals Have Recently Unleashed A New Threat Known As XHAMSTER Ransomware, A Variant Of The Notorious Phobos Ransomware. This Malicious Software Is Designed To Lock Victims' Data, Rendering It Inaccessible And Unusable.
XHAMSTER Ransomware Employs A Powerful Encryption Algorithm, Making It Extremely Difficult, If Not Impossible, To Restore The Affected Files Without The Decryption Keys Held By The Hackers Themselves.
Once A System Is Infected, XHAMSTER Ransomware Encrypts Files On The Victim's Computer, Making Them Unreadable And Effectively Holding Them Hostage.
The Attackers Demand A Ransom Payment In Exchange For The Decryption Keys Necessary To Unlock The Files. Victims Are Often Left With No Choice But To Pay The Ransom In Hopes Of Regaining Access To Their Valuable Data.
XHAMSTER Ransomware Is Crucial For Individuals And Organizations To Take Proactive Measures To Protect Themselves Against Ransomware Attacks.
This Includes Regularly Updating Software And Operating Systems, Employing Reliable Antivirus Programs, And Practicing Safe Browsing Habits. Additionally, Maintaining Secure And Up-to-date Backups Of Important Files Can Help Mitigate The Impact Of XHAMSTER Ransomware Attacks, Allowing Victims To Restore Their Data Without Giving In To The Hackers' Demands.
In The Face Of Evolving Cyber Threats Like XHAMSTER Ransomware, Staying Informed About The Latest Cybersecurity Best Practices And Being Cautious While Online Are Essential Steps To Safeguarding Personal And Sensitive Information From Malicious Attacks.
As Part Of Its Actions, The XHAMSTER Ransomware Will Also Significantly Modify The Original Names Of The Locked Files:
Victims Of The Threat Will Be Presented With Two Ransom Notes.
In Recent Instances Of The XHAMSTER Ransomware Attacks, Victims Have Been Faced With A Chilling Message Demanding A Ransom For The Release Of Their Encrypted Files. Unlike Many Other Ransomware Messages, The Exact Sum To Be Paid Is Left Ambiguous.
Instead, The Attackers Have Adopted A Unique Approach: The Ransom Amount Is Determined By How Swiftly Affected Users Establish Contact With Them. XHAMSTER Ransomware Tactic Adds A Sense Of Urgency To The Situation, Pressuring Victims Into Immediate Action To Reclaim Their Valuable Data.
The Ransom Demand Specifies That The Only Accepted Payment Method Is Bitcoin, A Decentralized Digital Currency Often Favored By Cybercriminals Due To Its Anonymity And Difficulty To Trace.
This Preference For Bitcoin Transactions Ensures That The Criminals Can Operate Discreetly, Making It Challenging For Law Enforcement Agencies To Track Their Movements Or Freeze Their Assets.
Interestingly, The Attackers Offer A Glimmer Of Hope To Their Victims. In A Seemingly Generous Gesture, They Allow Users To Send Up To 5 Files For Decryption Free Of Charge. This Offer Serves As A Demonstration Of The Hackers' Ability To Unlock The Affected Data, Showcasing Their Capability To Fulfill Their End Of The Bargain.
However, There Are Limitations To This Offer. The Total Size Of The Selected Files Must Not Exceed 3MB In Their Original, Non-archived Form. Additionally, These Files Should Not Contain Any Critical Or Valuable Information, Making It Clear That This Offer Is More Symbolic Than Practical.
To Initiate The Process Of Negotiation, Victims Are Instructed To Contact The Hackers Via The Same ICQ Account Mentioned In The Names Of The Encrypted Files. ICQ, A Messaging Platform Popular Among Cybercriminals For Its Privacy Features, Provides A Secure Channel For Communication Between The Attackers And Their Victims.
This Direct Communication Ensures That The Ransom Negotiations Can Proceed Smoothly, Allowing The Hackers To Provide Further Instructions, Clarify Payment Details, And, If Necessary, Offer Additional Proof Of Their Decryption Capabilities.
For Victims Of The XHAMSTER Ransomware, This Situation Underscores The Importance Of Cybersecurity Awareness And Preparedness. Regularly Updating Security Software, Maintaining Secure Backups Of Essential Files, And Exercising Caution While Online Can Significantly Reduce The Risk Of Falling Victim To Such Attacks.
Additionally, Law Enforcement Agencies And Cybersecurity Experts Continue To Collaborate To Track Down These Criminals And Bring Them To Justice, Highlighting The Ongoing Efforts To Combat Ransomware Threats And Protect Individuals And Organizations From These Malicious Activities.
XHAMSTER Ransomware Or Any Other Malicious Software. Providing Such Information Could Potentially Aid Malicious Individuals In Their Activities. It's Important To Be Cautious And Vigilant About Cybersecurity Threats And To Follow Best Practices To Protect Your Devices And Data.
Regularly Updating Your Software, Using Reputable Antivirus Programs, And Avoiding Suspicious Email Attachments Or Links Are Essential Steps In Safeguarding Your Digital Security.
If You Suspect Your Computer May Be Infected With Ransomware Or Any Other Malware, It's Crucial To Seek Assistance From Cybersecurity Professionals Or Reliable Antivirus Software To Mitigate The Potential Damage.
1. Award-winning Security
The Same Malware That Attacks Fortune 500 Companies Attacks Private Users, Too. Sophos Home Uses The Same Award-winning Security Features That Keep Those Companies Safe.
New Features Of The Sophos Home
You Have Been Infected. Well, Not You, But Your Computer Has. It’s Slow. You Need A No-nonsense Malware Cleaner To Get Your Computer Back Up To Speed. HitmanPro Is The Malware Remover Of Choice For Tens Of Millions Of People.
It’s Really Small
You Can Download HitmanPro In Two Seconds (unless You Still Have Dial-up Internet). It’s Only 10MB. Plus, You Do Not Have To Install It – Just Run It After It’s Downloaded.
It Scans For Bad Behavior
A Standard Antivirus Program Misses Stuff. It’s Focused On Finding Malware Signatures That Virus Firms Have Identified As Malicious. But What About New, Zero-day Threats That Have Not Been Researched? That’s Why HitmanPro Looks At Behaviors When Scanning For Trojans And Other Malware. Bad Behavior Is Caught, With Or Without A Malware Signature.
It Uses Multiple Experts
Two Heads Are Better Than One. So We Have Four. HitmanPro Leverages Malware Databases From Four Security Labs, Including SophosLabs, To Be Incredibly Thorough When Scanning For And Cleaning Up Spyware And Malware. More Research Means More Powerful Cleaning.
It Cleans Up After Itself
Malware Piggybacks On Various Programs To Gain Access To Your Computer. HitmanPro Removes That Malware – And It Does Not Stop There. Damaged Windows Resources Are Brought Back To Their Safe, Original Versions.
It Goes Deep To Clean
Resilient Malware Can Also Affect Critical System Files And Boot Records To Manipulate The Windows Operating System And Installed Antivirus Software. This Is Even Before The Operating System Boots. HitmanPro Can Remove These Persistent Threats From Within The Running Operating System And Its Boot Records.
Cylance Smart Antivirus Is The First Next-generation Antivirus Available To Consumers And Provides Families With The Only Enterprise Class Security Software Designed For Personal Use. Using Artificial Intelligence, Cylance Smart Antivirus Eliminates The Need For Updates And Pop-ups While It Protects You And Your Loved Ones Against The Latest Cybersecurity Threats.
| Smart Antivirus For US | Smart Antivirus For UK |
| Smart Antivirus For Ireland | Smart Antivirus For Canada |
| Smart Antivirus For New Zealand | Smart Antivirus For Australia |
An Antivirus That Works Smarter, Not Harder, From BlackBerry. Lightweight, Non-intrusive Protection Powered By Artificial Intelligence.
Traditional Antivirus Can’t Keep Up
Traditional Antivirus Typically Uses A Signature Based Model, Which Is Reliant On Capturing New Viruses In The Wild And Creating A Master List Of Malware For Users To Download. This Makes It Especially Vulnerable To Zero-day Attacks And Modern Threats Which Can Alter Themselves Too Quickly For Signature Updates To Catch.
A Different Approach
Cylance Uses Cutting-edge Algorithms And Artificial Intelligence To Proactively Protect You, Preventing Threats Like Malware, Hackers, Viruses, Ransomware, And Malicious Websites. It Does This Whilst Being Lightweight And Easy To Use. Cylance’s AI Has Been Demonstrated As Effective Against Threats -- Even Without Updates -- Over 2 Years Into The Future.
Advanced AI Training
We Use Cloud-based Supercomputers And Millions Of Examples Of Malicious Programs To Train A Neural Net, A Kind Of Digital Brain, To Recognise Threats.
Download And Protect
When You Purchase Cylance, This Is What You Download Onto Your Computer - A Superlightweight ’brain’, Trained To Catch And Quarantine Viruses.
Detection In Milliseconds
Cylance Sits In The Background, Instantly Recognising Threats The Moment They Occur And Reacting In Milliseconds – Unlike Other Antivirus Software Which Must Constantly Scan For Threats.
Complete Protection
Our AI Quarantines Files It Identifies As Threats, Allowing You To Review Individual Threats On You And Your Family’s Computers.
Cutting Edge Protection Without The Bloat Of Traditional Antivirus
Cylance Sits In The Background, Instantly Recognising Threats The Moment They Occur And Reacting In Milliseconds - Unlike Other Antivirus Software Which Must Constantly Scan For Threats.
1. Stops Infections Before They Can Attack
Traditional Antivirus Waits For You To Be Infected Before It Can Act. Cylance Observes The Behaviour Of Programs In Real-time, Detecting Threats In Milliseconds - Before They Can Execute.
2. Protects Against Never-before Seen Malware
Proactive AI Provides Protection From All Types Of Malware - Existing Threats And Those Yet To Be Developed. Cylance Prevents Attacks Before They Happen Rather Than Relying On Other Users Becoming Infected To ’discover’ Threats.
3. Unobtrusive Protection
We Know You Just Want Your Antivirus To Keep Your Safe - Not Waste Your Time. That’s Why We Guarantee To Never Bother You With Unwanted Alerts Or Pop-up Ads. Promise.
4. Light On RAM And CPU
We’ve Done All The Computational Heavy Lifting In The Cloud. As A Result, Cylance Uses Much Less RAM And CPU Than Other AV Solutions - Making It Perfect For Gamers Or Alongside Other Intensive Processes. You Won’t Even Notice We’re There.
Cylance Protects Devices On All Major Platforms And With Remote Protection, Cloud-based Support, Simple Set-up, It’s Never Been Easier To Be The Expert.
Easy To Install And Use
It’s Easy To Get Started With Cylance. Simply Download And Install, And You Have The Power Of An AI Supercomputer On Your Device. The Intuitive Interface Allows You To Manage Devices Centrally, Modify Settings, And Check Which Files Cylance Has Quarantined.
Remote Management
Cloud Based Support And Remote Management And Protection Means No More Worried Calls From Mom. Remotely View The Quarantine List Of All Devices To Keep Your Family Secure And Take The Work Out Of Being The Expert.
Operating Systems:
Memory
Internet Browser Support:
Cylance Uses Artificial Intelligence To Deliver Prevention-first, Predictive Security Products And Specialized Security Services That Change How Organizations Approach Endpoint Security. Cylance’s Security Solutions Provide Full Spectrum Predictive Threat Prevention And Visibility Across The Enterprise, Combatting Threats Such As Malware, Ransomware, File Less Malware, Malicious Scripts, Weaponized Docs, And Other Attack Vectors.
| Smart Antivirus For US | Smart Antivirus For UK |
| Smart Antivirus For Ireland | Smart Antivirus For Canada |
| Smart Antivirus For New Zealand | Smart Antivirus For Australia |
With AI Based Malware Prevention, Application And Script Control, Memory Protection, Device Policy Enforcement, Root Cause Analysis, Threat Hunting, Automated Threat Detection And Response, Coupled With Expert Security Services, Cylance Can Protect Endpoints Without Increasing Staff Workload Or Costs.
The Essential PC & Internet Security Solution
1. Antivirus & Anti-Spyware Engine
Detects And Removes Viruses, Spyware, Trojan Horses, Worms, Bots And More. Independently Tested To Provide Superior Protection.
2. Advanced Real-Time Antivirus
Provides Access To The Up-to-date Database Of Antivirus Signatures To Protect Against Newly Emerging Threats. Real-Time Cloud Database Contains Up-to-date Reputation Of Files, Web Resources And Software Enhancing Traditional Antivirus + Firewall Protection
Checks Files Against Real-time Cloud Database To Ensure That Even The Latest Threats Are Not Missed.
Contains The Latest Antivirus Signatures, Web Resources And Software To Ensure Up-to-date Protection.
3. Two-way Firewall
Stops Internet Attacks At The Front Door And Even Catches Thieves On Their Way Out. Our Two-way Firewall Proactively Protects Against Inbound And Outbound Attacks While Making You Invisible To Hackers.
4. Advanced Firewall
No Product Is 100% Effective Against Viruses Or Spyware. ZoneAlarm’s Advanced Firewall Monitors Behaviors Within Your Computer To Spot And Stop Even The Most Sophisticated New Attacks That Bypass Traditional Antivirus And Security Suites.
5. Additional Layers
Multiple Layers Of Advanced Protection Provide Unsurpassed Security.
Anti-Phishing
Protects You Against Phishing Attacks.
Antivirus/Anti-Spyware Engine
Detects And Remove Viruses, Spyware, Trojan Horses, Worms, Bots And Rootkits.
Advanced Real-Time Antivirus
Enhances Protection By Checking Against An Always Up-to-date Cloud Database Of Antivirus Signatures.
Advanced Firewall
Monitors Programs For Suspicious Behavior Spotting And Stopping New Attacks That Bypass Traditional Anti-virus Protection.
Two-way Firewall
Makes Your PC Invisible To Hackers And Stops Spyware From Sending Your Data Out To The Internet.
Identity Protection
Helps To Prevent Identity Theft By Guarding Your Personal Data.
Browser Protection
Protects Your Computer From Web Threats Before They Reach Your Browser.
1. Anti-Phishing Add-on
Google® Chrome All Versions
2. Microsoft® Windows® 10
3. Microsoft® Windows 7 SP1 All Versions
4. Microsoft .NET Framework
Version 3.5 Or Later
Note: If A Supported Microsoft .NET Framework Is Not Installed, It Will Be Installed With ZoneAlarm

Secure Your Digital Life Completely. True Cybersecurity Needs To Be Proactive, Not Reactive.
Support
Special Features Of Heimdal Premium Security Home
ANTIVIRUS IS NOT ENOUGH IN TODAY'S EVER EVOLVING ONLINE THREATSCAPE
Heimdal Premium Security Home Is The Ultimate Cybersecurity Suite, Combining A True Proactive Threat Prevention Solution With A Next-gen Antivirus With Market Leading Detection Rates So You Can Enjoy The Internet Freely!
Secure Your Digital Life Completely
Next-gen Threat Prevention Based On Machine Learning Meets A Powerful Antivirus With Market-leading Detection, So Your Online Security Is Flawless
Discover Actual Security In An Ever-changing Threat Landscape.
Heimdal™ Premium Security Home Brings The Unique Threat Prevention Layer Of Heimdal™ Threat Prevention Home On Top Of A Flawless, Market-leading Detection Heimdal™ Next-Gen Antivirus Home Antivirus To Stop Ransomware, Data Leakage, Viruses, APTs, Exploits & Other Advanced Online Threats.
Enjoy A Next Gen Multi-layered Security Suite.
Heimdal™ Premium Security Home Prevents Unknown Threats And Stops The Known Attacks. Browse Online Without The Fear Of Ransomware, Cryptojacking And Other Malware Strains, Connect Devices Without Worrying They’re Compromised.
Prevention Is The Best Cure.
Heimdal™ Premium Security Home Eliminates Vulnerabilities In Your System And Protects The Valuable Data That Makes Up Your Digital Life. Seamlessly Installs And Patches Your Other Software, So Your System Is Always Updated And Always Secure.
XHAMSTER Ransomware, Remove XHAMSTER Ransomware, XHAMSTER Ransomware Removal, Uninstall XHAMSTER Ransomware, Delete XHAMSTER Ransomware| Links1 | Links2 | Links3 | Products | Social Links |
|---|---|---|---|---|
| Home | Blog | Sitemap | Email Checker Tool | |
| About | CSI Links | ISRO Project Code: AA0802 | Offers | |
| Disclaimer | Gallery | Contact Us | Antivirus | |
| Privacy Policy | Software Downloads |