 Blog's Page
Blog's Page

Trojan.EyeStye Is A Malicious trojan Infection That Poses A Significant Threat To Computer Systems By Employing Sophisticated Techniques To Evade Detection By Various Antivirus Programs, Thereby Remaining Concealed Within The PC.
Trojan.EyeStye Trojan Often Adopts A Deceptive Guise, Masquerading As A Seemingly Helpful Application, Only To Unleash Its Destructive Capabilities Once Inside The Computer. Unlike Some Self-propagating Threats, Trojan.EyeStye Relies On User-initiated Downloads To Infiltrate A System, Adding An Element Of Social Engineering To Its Attack Vector.
Once Inside A System, Trojan.EyeStye Can Inflict A Range Of Detrimental Actions, The Extent Of Which Is Contingent On The Choices Made By The Hacker Controlling It.
Trojan.EyeStye Modus Operandi Encompasses Enabling Remote Access To The Compromised Computer, Providing The Hacker With The Ability To Infiltrate The System From A Remote Location Via The Internet. This Remote Access Feature Opens The Door For A Variety Of Malicious Activities Orchestrated By The Attacker.
One Of The Primary Functionalities Of Trojan.EyeStye Is To Engage In Surreptitious Surveillance Of The Users. Trojan.EyeStye Insidious Trojan Employs Keylogging Techniques, Allowing It To Record And Track The Keystrokes Made By Users On The Infected Computer.
As A Result, The Hacker Gains Access To Sensitive Information, Including Login Credentials And Banking Passwords. The Insidious Nature Of Trojan.EyeStye Lies In Its Ability To Carry Out These Spying Activities Discreetly, Often Leaving Users Oblivious To The Compromise Of Their Confidential Data.
The Stealthy Nature Of Trojan.EyeStye, Coupled With Its Capacity To Avoid Detection By Conventional Antivirus Programs, Makes It A Formidable Tool For Cybercriminals. Trojan.EyeStye Trojan Operates Covertly, Silently Infiltrating The Computer System And Executing Its Malicious Agenda Without Raising Alarm Bells.
Users, Unfortunately, May Remain Unaware Of The Compromise Until The Damage Is Done, As Trojan.EyeStye Strategically Conceals Its Presence Within The System.
To Mitigate The Risks Associated With Trojan.EyeStye And Similar Trojan Threats, Users Are Advised To Adopt A Multifaceted Approach To Cybersecurity. Trojan.EyeStye Includes Exercising Caution When Downloading Applications Or Files From The Internet, Particularly From Untrusted Sources.
Regularly Updating And Patching The Operating System And Installed Software Can Close Potential Vulnerabilities That Trojans Often Exploit. Additionally, Deploying Reputable Antivirus Software With Updated Definitions Is Essential To Enhance The System's Defenses Against Evolving Threats.
In Conclusion, Trojan.EyeStye Stands Out As A Formidable Trojan Infection That Employs Stealth And Sophistication To Compromise Computer Systems. Its Ability To Avoid Detection By Antivirus Programs, Coupled With Its Capacity For Remote Access And Covert Surveillance, Underscores The Importance Of Robust Cybersecurity Practices.
Users Must Remain Vigilant, Employ Security Measures, And Stay Informed About The Evolving Tactics Employed By Trojans To Safeguard Their Digital Assets And Personal Information.
This Black Friday VPN Deals 2023, Fortify Your Online Security With Exclusive VPN Deals! Unlock Discounts On Top-tier Services, Ensuring Private And Unrestricted Internet Access. Black Friday VPN Deals 2023, Browse Anonymously, Safeguard Sensitive Data, And Enjoy Seamless Streaming With Lightning-fast Speeds. Don't Miss Out On These Limited-time Offers—invest In Your Digital Privacy This Black Friday VPN Deals 2023 And Enjoy A Safer Online Experience. Read More...
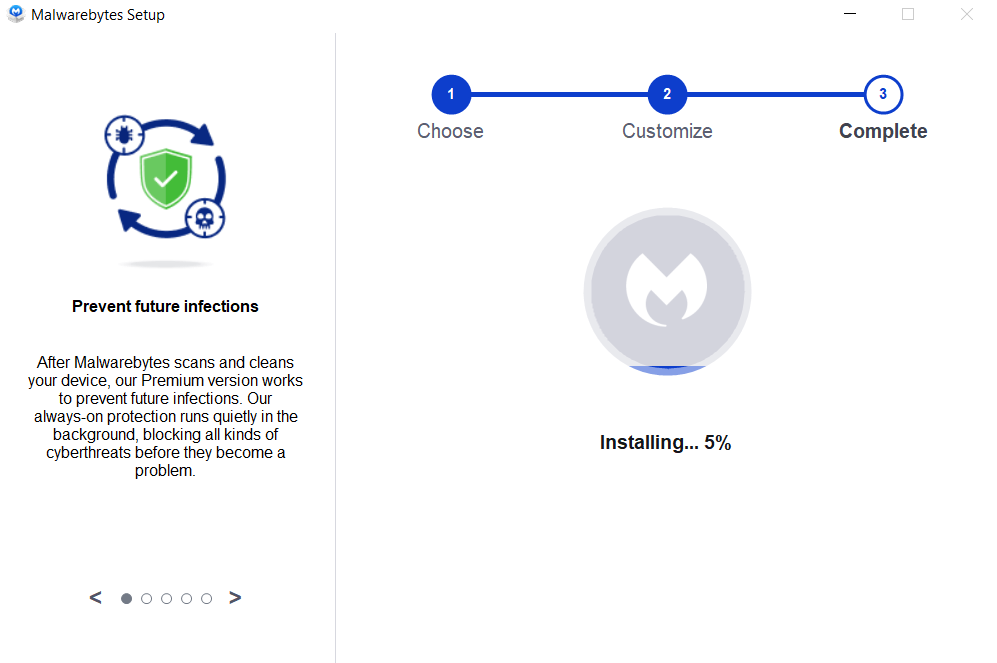
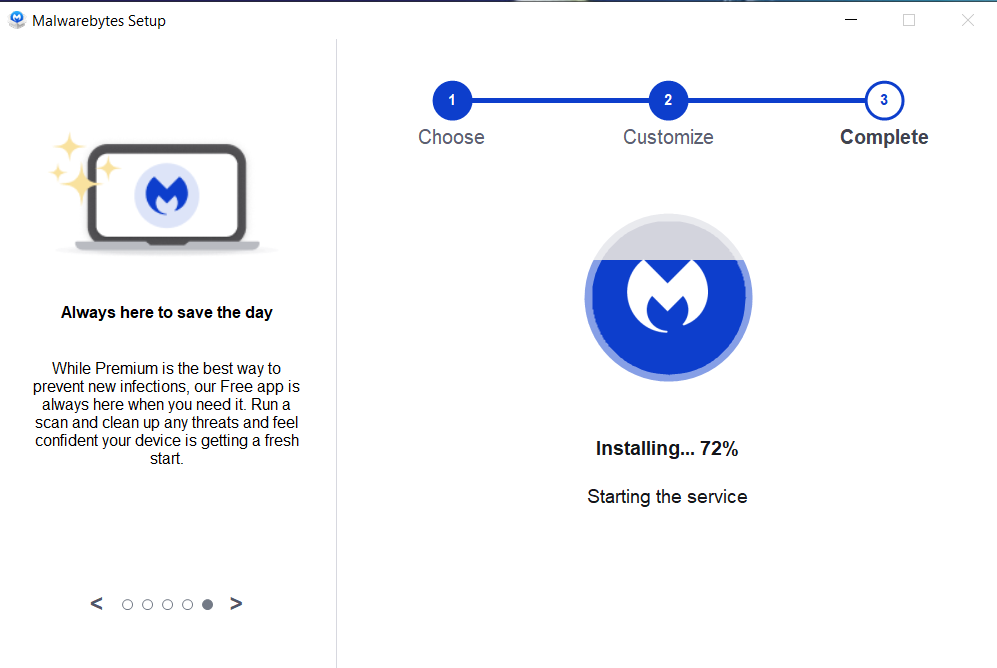
Removing Malware From A Windows Computer Involves A Combination Of Using Antivirus Or Anti-malware Tools, Performing System Scans, And Taking Manual Actions To Eliminate The Malicious Software. Here's A Step-by-step Guide:
Ctrl + Shift + Esc To Open Task Manager.Win + R To Open The Run Dialog, Type cleanmgr, And Press Enter.Remember To Maintain Good Security Practices, Such As Keeping Your Operating System And Software Up-to-date, Using A Reputable Antivirus Program, And Being Cautious When Clicking On Links Or Downloading Files From The Internet. Regularly Backing Up Your Important Data Is Also Crucial To Mitigate The Impact Of Potential Infections.
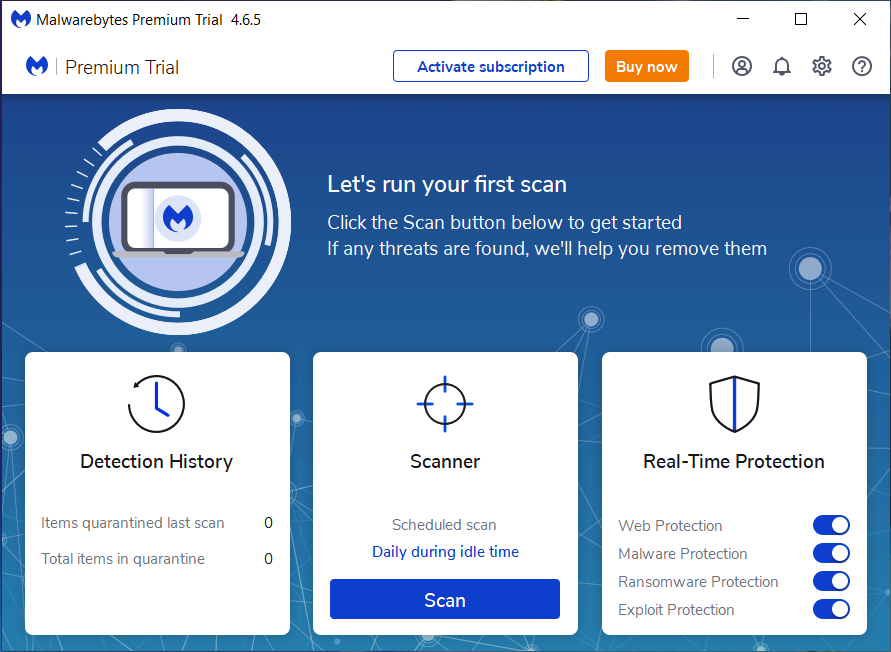
If You Have Malwarebytes Installed On Your Computer And It Has Detected Malware, Follow These Steps To Remove The Malware:
Open Malwarebytes:
Update Malwarebytes:
Run A Threat Scan:
Review Scan Results:
Quarantine Or Remove Threats:
Reboot Your Computer:
Check For Persistence:
Monitor For Issues:
Clear Browser Data:
Reset Browser Settings:
Review Installed Programs:
Change Passwords:
Update Operating System:



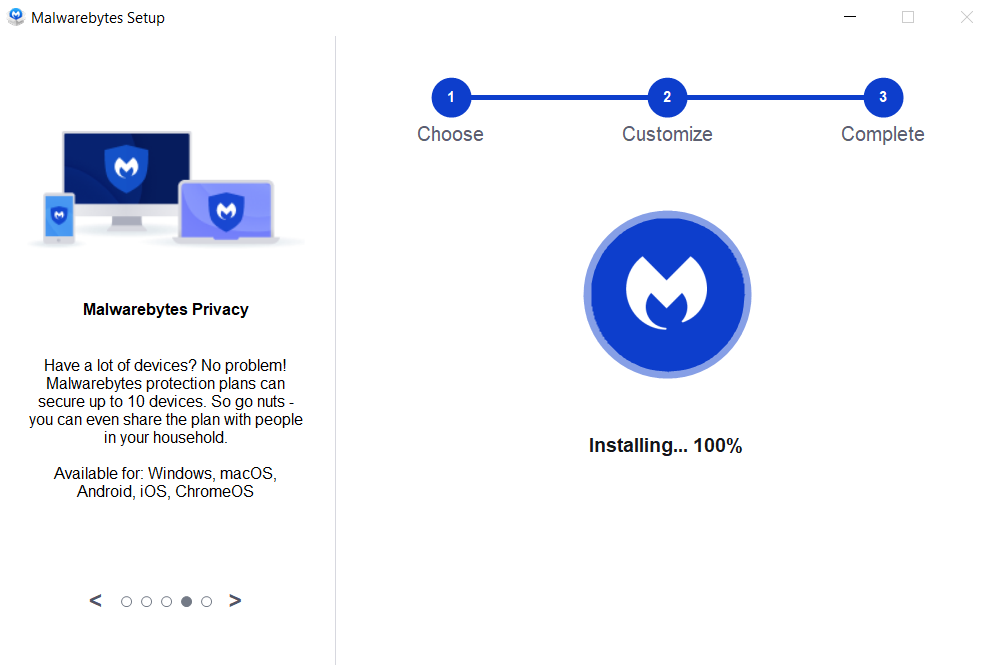

If The Malware Persists Or If You Encounter Difficulties During The Removal Process, You May Want To Seek Assistance From The Malwarebytes Support Community Or Consider Running Additional Scans Using Other Reputable Antivirus Or Anti-malware Tools. Remember To Keep Your Security Software Updated And Practice Safe Computing Habits To Minimize The Risk Of Future Infections.
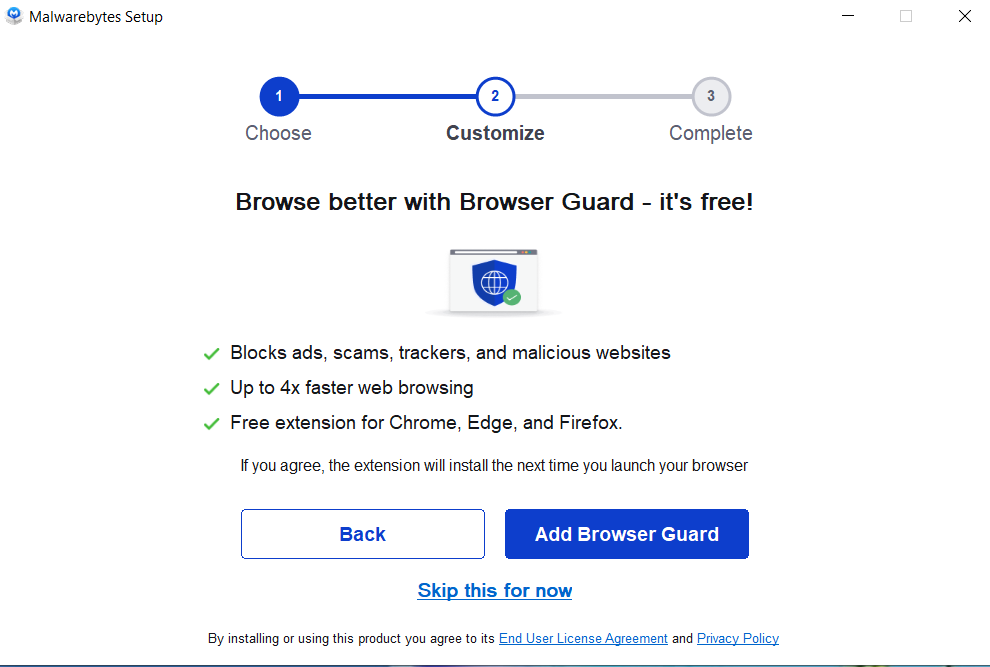
Malwarebytes Is A Leading Cybersecurity Solution Dedicated To Protecting Users From The Ever-evolving Landscape Of Digital Threats. With A Proven Track Record In Malware Detection And Removal, Malwarebytes Offers Cutting-edge Technology To Safeguard Computers And Devices Against Viruses, Ransomware, And Other Malicious Software.
Boasting A User-friendly Interface, Malwarebytes Provides A Seamless Experience For Both Novice And Advanced Users. Its Real-time Protection Capabilities, Coupled With Powerful Scanning Algorithms, Ensure That Users Are Shielded From The Latest Cybersecurity Threats. Malwarebytes Continually Updates Its Extensive Malware Database, Enabling Users To Stay Ahead Of Emerging Risks And Vulnerabilities.
Beyond malware Detection, Malwarebytes Offers Additional Features Such As Web Protection And Anti-exploit Technology, Fortifying Defenses Against Malicious Websites And Zero-day Exploits. The Software's Lightweight Footprint Ensures Minimal Impact On System Performance, Delivering Robust Security Without Compromising Speed.
Whether Used As A Standalone Solution Or In Conjunction With Other Cybersecurity Tools, Malwarebytes Remains A Trusted Ally In The Battle Against Cyber Threats. As A Proactive And Responsive Cybersecurity Partner, Malwarebytes Empowers Users To Navigate The Digital World With Confidence, Knowing That Their Data And Devices Are Safeguarded Against The Latest And Most Sophisticated Threats.
Trojan.EyeStye, Remove Trojan.EyeStye, Uninstall Trojan.EyeStye, Delete Trojan.EyeStye, Trojan.EyeStye Removal