 Blog's Page
Blog's Page
Recently, Numerous Individuals Have Reported Encountering Intrusive Pop-up Notifications On Their Computers And Mobile Devices, Urging Them To Grant Permission For Notifications Or Activate Push Notifications From A Site Known As News-wuweyo.com Browser Hijacker.
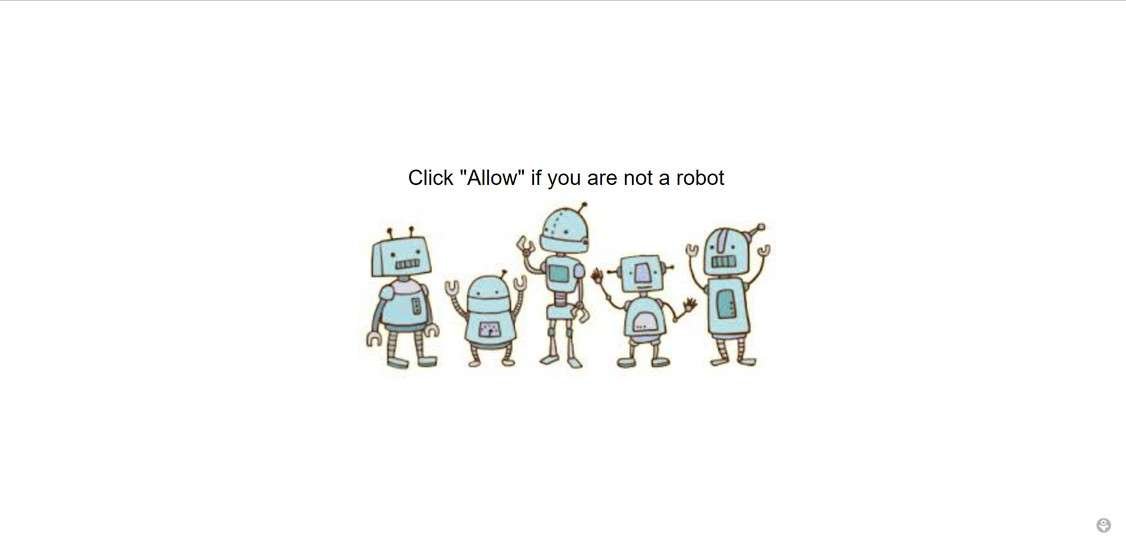
At First Glance, News-wuweyo.com Website May Seem Innocuous, Typically Presenting A Video Player Alongside A Message Requesting Users To Enable Notifications To View The Video. However, Consenting To Notifications From News-wuweyo.com Site Leads To A Barrage Of Explicit Content, Counterfeit Antivirus Alerts, Gambling Advertisements, And Other Harmful Pop-ups, Even When The Browser Is Not In Use.
News-wuweyo.com Is Suspected To Be Associated With Various adware As Well As The Browser Hijacker Campaigns And Scam Networks That Seek To Expose Users To Undesired Content And Pilfer Their Personal Information.
News-wuweyo.com Website Article Aims To Delve Into The Workings Of The News-wuweyo.com Scam, Provide Insights Into Removing News-wuweyo.com From Infected Devices, And Offer Guidance On Avoiding Falling Prey To It In The First Place.
The News-wuweyo.com Browser Hijacker Manifests Several Symptoms That Can Disrupt A User's Online Experience And Compromise The Security Of Their Device.
Here Are The Symptoms Associated With News-wuweyo.com:
Intrusive Pop-up Notifications: Users May Encounter Persistent Pop-up Notifications Prompting Them To "allow" Notifications Or Enable Push Notifications From News-wuweyo.com. These Notifications Can Appear Even When The Browser Is Closed.
Unauthorized Browser Homepage And Search Engine Changes: The Browser Settings May Be Altered Without User Consent, Leading To Changes In The Homepage And Default Search Engine. News-wuweyo.com May Set Itself As The Default, Making It Challenging To Revert To The User's Preferred Settings.
Unwanted Browser Extensions: The News-wuweyo.com Browser Hijacker May Install Unwanted Extensions Or Add-ons, Affecting The Browser's Functionality. These News-wuweyo.com Extensions Could Lead To Further Intrusive Pop-ups And Ads.
Redirects To News-wuweyo.com: Users Might Experience Automatic Redirections To The News-wuweyo.com Website, Even When Attempting To Visit Other Legitimate Sites. News-wuweyo.com Behavior Interferes With Normal Browsing Activities.
Increased Display Of Advertisements: The News-wuweyo.com Hijacker Is Likely To Flood The User's Browser With A Heightened Volume Of Advertisements, Including Pop-ups, Banners, And In-text Ads. These Ads Are Often Irrelevant To The User's Interests And May Lead To Potentially Malicious Websites.
Sluggish Browser Performance: The Presence Of The News-wuweyo.com Browser Hijacker Can Result In Slower Browser Performance And Increased Loading Times Due To The Additional Content And Scripts It Introduces.
Tracking And Data Collection: News-wuweyo.com May Employ Tracking Mechanisms To Monitor The User's Online Activities, Collecting Browsing Habits, Search Queries, And Other Sensitive Information. News-wuweyo.com Data May Be Used For Targeted Advertising Or Potentially Sold To Third Parties.
Security Risks: The News-wuweyo.com Browser Hijacker Poses Security Risks By Exposing Users To Potentially Harmful Content, Fake Alerts, And Scams. Clicking On Malicious Links Or Interacting With Deceptive Pop-ups Can Lead To Further Malware Infections Or Compromise Personal Information.
To Address News-wuweyo.com's Symptoms, Users Should Take Immediate Action To Remove The News-wuweyo.com Browser Hijacker From Their System And Restore Their Browser Settings To A Secure State.
Utilizing Reputable Antivirus Or Anti-malware Software Can Assist In The Detection And Removal Of Such Threats. Additionally, Exercising Caution While Browsing And Avoiding Interactions With Suspicious Pop-ups Can Help Prevent Future Infections.
To Remove The News-wuweyo.com Browser Hijacker From An Infected PC, Follow These Steps.
First, Uninstall Any Suspicious Programs From The Control Panel. Next, Reset The Browser Settings To Default. Check For And Remove Any Unwanted Browser Extensions Related To News-wuweyo.com. Run A Reputable Antivirus Or Anti-malware Scan To Detect And Eliminate Any Remaining Threats.
Clear Browser Cache And Cookies. Consider Using A Dedicated Ad-blocker Extension To Prevent Future Intrusions. Finally, Educate Yourself On Safe Browsing Practices To Avoid Similar Infections. Regularly Update Your Antivirus Software And Keep The Operating System Up-to-date For Enhanced Security.
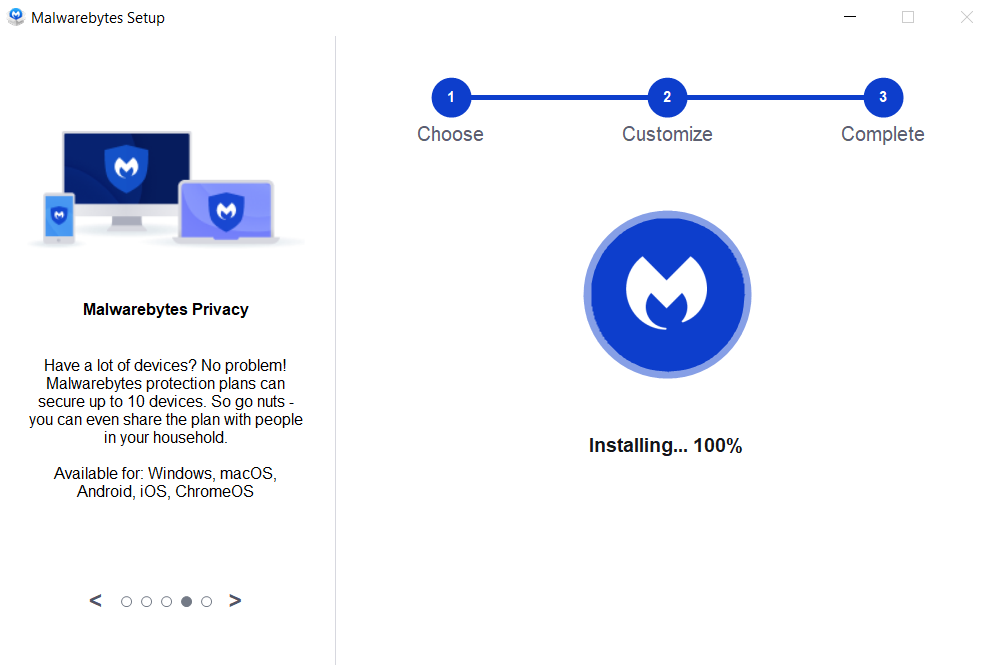
Removing Malware From A Windows Computer Involves A Combination Of Using Antivirus Or Anti-malware Tools, Performing System Scans, And Taking Manual Actions To Eliminate The Malicious Software. Here's A Step-by-step Guide:
Ctrl + Shift + Esc To Open Task Manager.Win + R To Open The Run Dialog, Type cleanmgr, And Press Enter.Remember To Maintain Good Security Practices, Such As Keeping Your Operating System And Software Up-to-date, Using A Reputable Antivirus Program, And Being Cautious When Clicking On Links Or Downloading Files From The Internet. Regularly Backing Up Your Important Data Is Also Crucial To Mitigate The Impact Of Potential Infections.
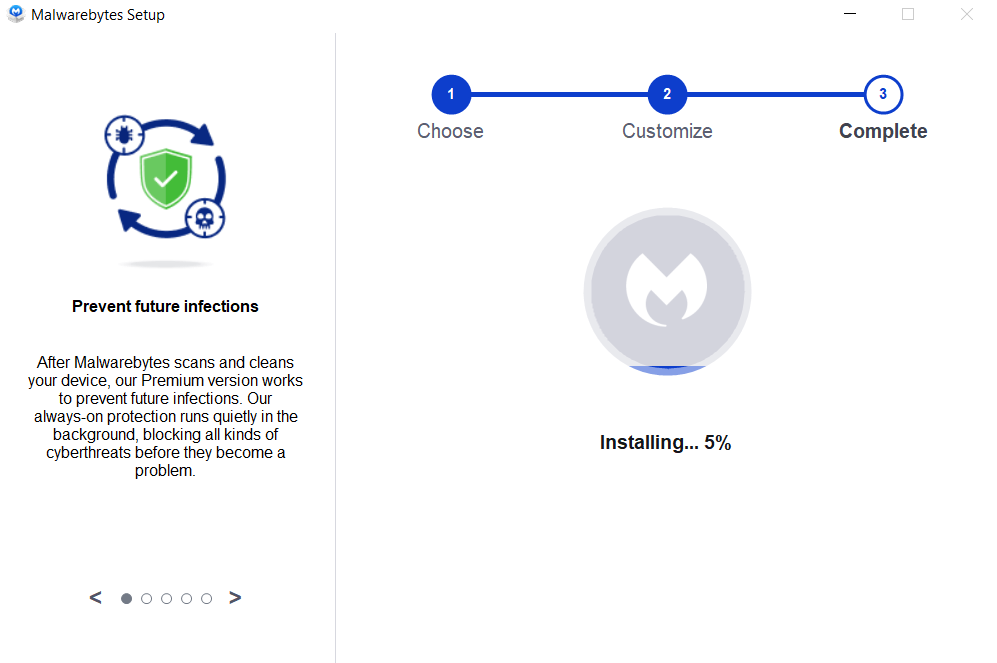
If You Have Malwarebytes Installed On Your Computer And It Has Detected Malware, Follow These Steps To Remove The Malware:
Open Malwarebytes:
Update Malwarebytes:
Run A Threat Scan:
Review Scan Results:
Quarantine Or Remove Threats:
Reboot Your Computer:
Check For Persistence:
Monitor For Issues:
Clear Browser Data:
Reset Browser Settings:
Review Installed Programs:
Change Passwords:
Update Operating System:



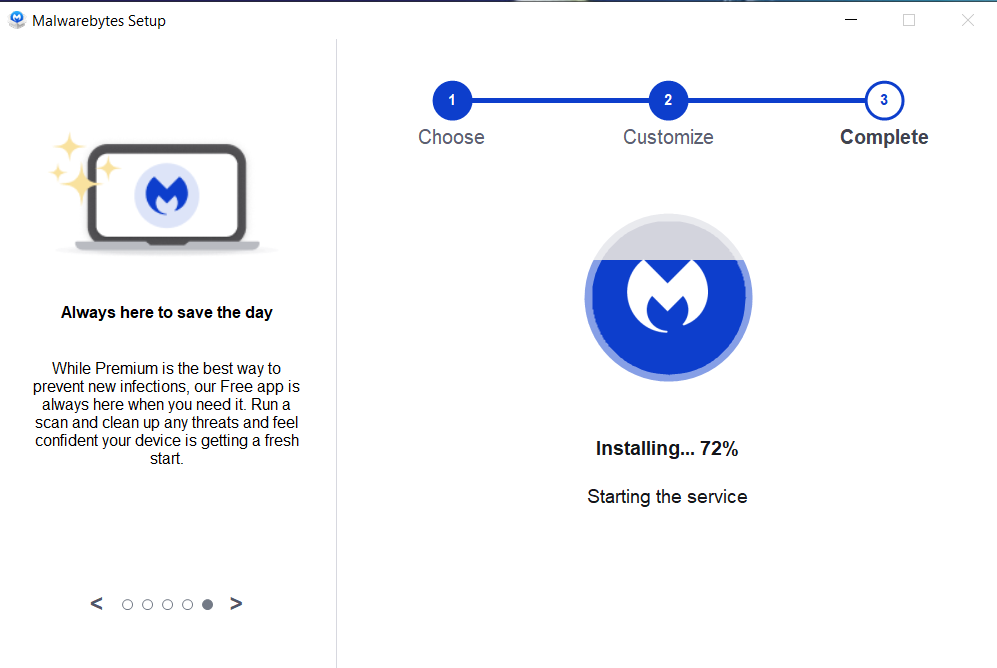

If The Malware Persists Or If You Encounter Difficulties During The Removal Process, You May Want To Seek Assistance From The Malwarebytes Support Community Or Consider Running Additional Scans Using Other Reputable Antivirus Or Anti-malware Tools. Remember To Keep Your Security Software Updated And Practice Safe Computing Habits To Minimize The Risk Of Future Infections.
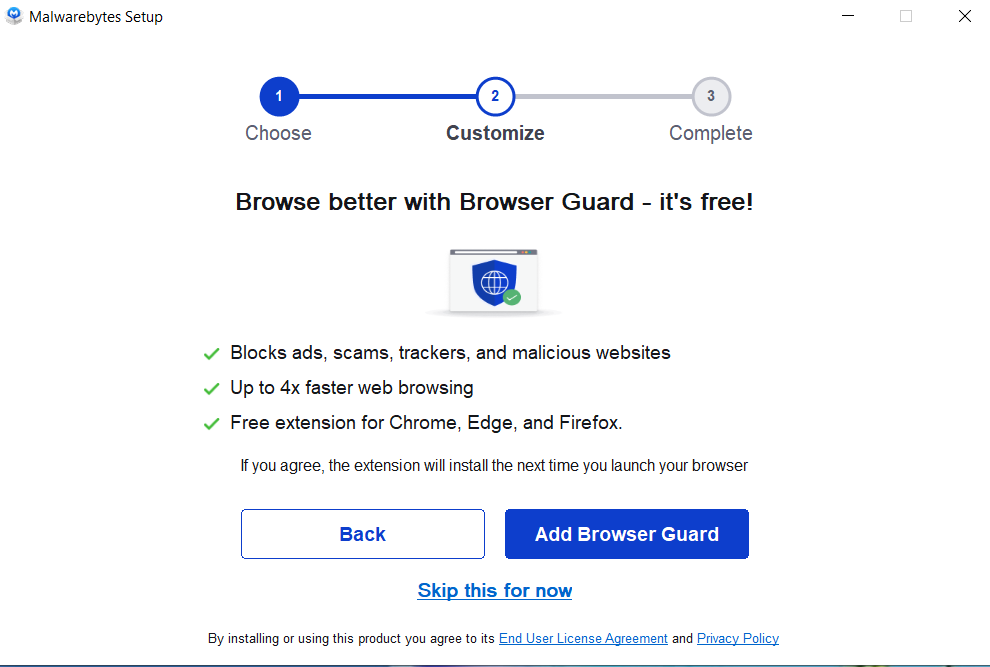
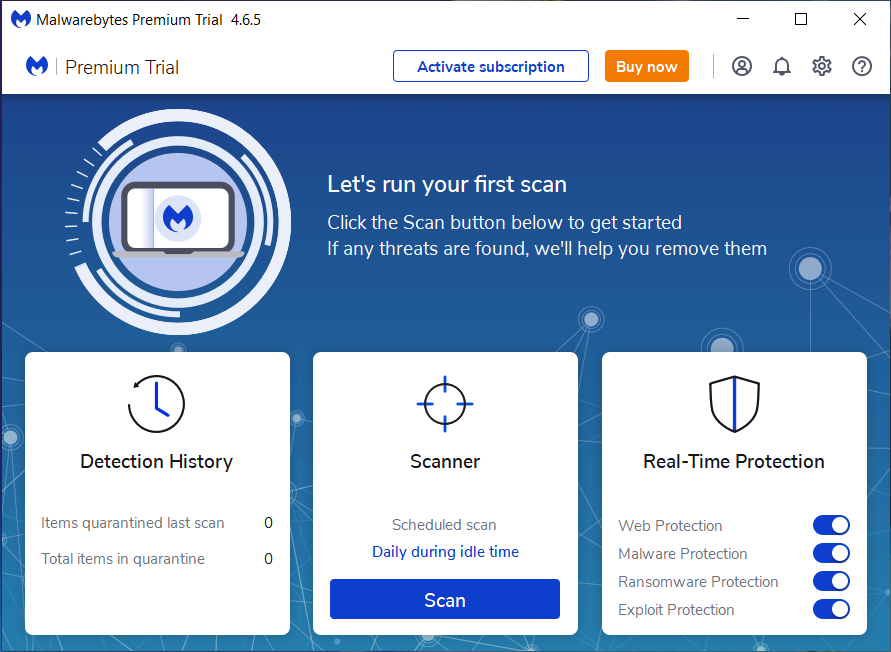
Malwarebytes Is A Leading Cybersecurity Solution Dedicated To Protecting Users From The Ever-evolving Landscape Of Digital Threats. With A Proven Track Record In Malware Detection And Removal, Malwarebytes Offers Cutting-edge Technology To Safeguard Computers And Devices Against Viruses, Ransomware, And Other Malicious Software.
Boasting A User-friendly Interface, Malwarebytes Provides A Seamless Experience For Both Novice And Advanced Users. Its Real-time Protection Capabilities, Coupled With Powerful Scanning Algorithms, Ensure That Users Are Shielded From The Latest Cybersecurity Threats. Malwarebytes Continually Updates Its Extensive Malware Database, Enabling Users To Stay Ahead Of Emerging Risks And Vulnerabilities.
Beyond malware Detection, Malwarebytes Offers Additional Features Such As Web Protection And Anti-exploit Technology, Fortifying Defenses Against Malicious Websites And Zero-day Exploits. The Software's Lightweight Footprint Ensures Minimal Impact On System Performance, Delivering Robust Security Without Compromising Speed.
Whether Used As A Standalone Solution Or In Conjunction With Other Cybersecurity Tools, Malwarebytes Remains A Trusted Ally In The Battle Against Cyber Threats. As A Proactive And Responsive Cybersecurity Partner, Malwarebytes Empowers Users To Navigate The Digital World With Confidence, Knowing That Their Data And Devices Are Safeguarded Against The Latest And Most Sophisticated Threats.
News-wuweyo.com, Uninstall News-wuweyo.com, News-wuweyo.com Removal, Remove News-wuweyo.com, Delete News-wuweyo.com| Links1 | Links2 | Links3 | Products | Social Links |
|---|---|---|---|---|
| Home | Blog | Sitemap | Email Checker Tool | |
| About | CSI Links | ISRO Project Code: AA0802 | Offers | |
| Disclaimer | Gallery | Contact Us | Antivirus | |
| Privacy Policy | Software Downloads |