 Blog's Page
Blog's Page

If You Find That You're Unable To Open Files And Notice The Addition Of The ".LPER" Extension To Them, It's Probable That Your System Has Been Infected With This Malicious Ransomware.
LPER Represents A Malicious ransomware Infection Designed To Encrypt Files, Thereby Restricting Access To Vital Data Such As Documents, Images, And Videos. LPER Ransomware Employs A Nefarious Tactic By Appending The ".LPER" Extension To The Encrypted Files, Rendering Them Inaccessible To The User.
Subsequently, Victims Are Coerced Into Paying A Ransom, Typically In The Form Of Bitcoin Cryptocurrency, In Exchange For The Decryption Key Required To Regain Access To Their Data.
Upon Initial Infection With The LPER Ransomware, The malware Conducts A Thorough Scan Of The Victim's Computer System, Targeting Specific File Types Crucial For Productivity And Personal Use.
LPER Ransomware Include Documents With Extensions Like .doc, .docx, .xls, And .pdf, As Well As Multimedia Files Such As Images And Videos. Once Identified, The Ransomware Proceeds To Encrypt These Files, Altering Their Extensions To ".LPER".
The Encryption Process Utilized By LPER Is Robust, Employing Sophisticated Algorithms That Render The Files Unreadable Without The Decryption Key. Consequently, Victims Find Themselves Unable To Open Or Access Their Encrypted Files, Leading To Significant Disruption In Their Daily Activities, Work, Or Personal Projects.
Following Encryption, The LPER Ransomware Delivers Its Ransom Demands To The Victim, Typically Through A Ransom Note Displayed On The Infected System Or Via Other Communication Channels. The Note Outlines The Terms For Payment Of The Ransom Amount And Provides Instructions On How To Proceed With The Transaction, Often Emphasizing The Urgency Of Compliance To Expedite File Decryption.
Mitigating The Impact Of The LPER Ransomware Requires Swift Action, Including Isolating The Infected System From Network Connections To Prevent Further Spread, And Seeking Assistance From Cybersecurity Professionals Or Utilizing Reputable Antivirus Software To Remove The Malware.
Additionally, Maintaining Regular Backups Of Important Data On Separate Storage Devices Or Cloud Services Can Serve As An Effective Preventive Measure Against Ransomware Attacks, Ensuring The Ability To Restore Files Without Succumbing To Extortion Demands.
This Is The Ransom Note That The LPER Ransomware Will Show To Its Victims:
ATTENTION!
Don’t Worry, You Can Return All Your Files!
All Your Files Like Pictures, Databases, Documents And Other Important Are Encrypted With Strongest Encryption And Unique Key.
The Only Method Of Recovering Files Is To Purchase Decrypt Tool And Unique Key For You.
This Software Will Decrypt All Your Encrypted Files.
What Guarantees You Have?
You Can Send One Of Your Encrypted File From Your PC And We Decrypt It For Free.
But We Can Decrypt Only 1 File For Free. File Must Not Contain Valuable Information.
You Can Get And Look Video Overview Decrypt Tool:
https://we.tl/t-oTIha7SI4s
Price Of Private Key And Decrypt Software Is $980.
Discount 50% Available If You Contact Us First 72 Hours, That’s Price For You Is $490.
Please Note That You’ll Never Restore Your Data Without Payment.
Check Your E-mail “Spam” Or “Junk” Folder If You Don’t Get Answer More Than 6 Hours.
To Get This Software You Need Write On Our E-mail:
support@fishmail.top
Reserve E-mail Address To Contact Us:
datarestorehelp@airmail.cc
Here Is A Summary Of The LPER Ransomware:
After Encrypting Your Computer's Files, The LPER Ransomware Will Exhibit The "_readme.txt" File, Which Includes The Ransom Note And Guidance On How To Reach The Ransomware Authors. Victims Are Prompted To Communicate With These Malicious Developers Via The support@fishmail.top And datarestorehelp@airmail.cc Email Addresses.
Removing Malware From A Windows Computer Involves A Combination Of Using Antivirus Or Anti-malware Tools, Performing System Scans, And Taking Manual Actions To Eliminate The Malicious Software. Here's A Step-by-step Guide:
Ctrl + Shift + Esc To Open Task Manager.Win + R To Open The Run Dialog, Type cleanmgr, And Press Enter.Remember To Maintain Good Security Practices, Such As Keeping Your Operating System And Software Up-to-date, Using A Reputable Antivirus Program, And Being Cautious When Clicking On Links Or Downloading Files From The Internet. Regularly Backing Up Your Important Data Is Also Crucial To Mitigate The Impact Of Potential Infections.
If You Have Malwarebytes Installed On Your Computer And It Has Detected Malware, Follow These Steps To Remove The Malware:
Open Malwarebytes:
Update Malwarebytes:
Run A Threat Scan:
Review Scan Results:
Quarantine Or Remove Threats:
Reboot Your Computer:
Check For Persistence:
Monitor For Issues:
Clear Browser Data:
Reset Browser Settings:
Review Installed Programs:
Change Passwords:
Update Operating System:




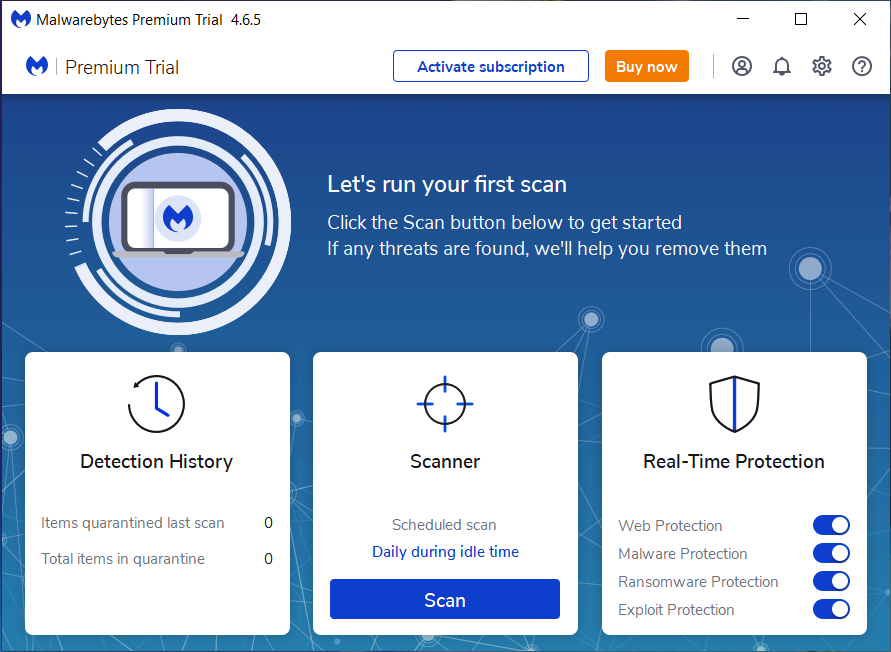
If The Malware Persists Or If You Encounter Difficulties During The Removal Process, You May Want To Seek Assistance From The Malwarebytes Support Community Or Consider Running Additional Scans Using Other Reputable Antivirus Or Anti-malware Tools. Remember To Keep Your Security Software Updated And Practice Safe Computing Habits To Minimize The Risk Of Future Infections.
Malwarebytes Is A Leading Cybersecurity Solution Dedicated To Protecting Users From The Ever-evolving Landscape Of Digital Threats. With A Proven Track Record In Malware Detection And Removal, Malwarebytes Offers Cutting-edge Technology To Safeguard Computers And Devices Against Viruses, Ransomware, And Other Malicious Software.
Boasting A User-friendly Interface, Malwarebytes Provides A Seamless Experience For Both Novice And Advanced Users. Its Real-time Protection Capabilities, Coupled With Powerful Scanning Algorithms, Ensure That Users Are Shielded From The Latest Cybersecurity Threats. Malwarebytes Continually Updates Its Extensive Malware Database, Enabling Users To Stay Ahead Of Emerging Risks And Vulnerabilities.
Beyond malware Detection, Malwarebytes Offers Additional Features Such As Web Protection And Anti-exploit Technology, Fortifying Defenses Against Malicious Websites And Zero-day Exploits. The Software's Lightweight Footprint Ensures Minimal Impact On System Performance, Delivering Robust Security Without Compromising Speed.
Whether Used As A Standalone Solution Or In Conjunction With Other Cybersecurity Tools, Malwarebytes Remains A Trusted Ally In The Battle Against Cyber Threats. As A Proactive And Responsive Cybersecurity Partner, Malwarebytes Empowers Users To Navigate The Digital World With Confidence, Knowing That Their Data And Devices Are Safeguarded Against The Latest And Most Sophisticated Threats.
LPER Ransomware, Remove LPER Ransomware, Uninstall LPER Ransomware, LPER Ransomware Removal, Get Rid Of LPER Ransomware