 Blog's Page
Blog's Page
Rogue Programs Represent A Significant Threat In The Digital Landscape, Capable Of Causing Substantial Harm To Individuals, Businesses, And Even Entire Systems. These malicious Software Applications Disguise Themselves As Legitimate Programs But Function With Malicious Intent. One Such Example, Albeit Hypothetical, Is Diftefum.co.in, An Emblematic Rogue Program Notorious For Its Deceptive Tactics And Detrimental Effects On Unsuspecting Users.
Diftefum.co.in Masquerades As A Benign Application, Often Enticing Users With Promises Of Useful Features Or Services. However, Beneath Its Facade Lies A Web Of Malicious Code Designed To Exploit Vulnerabilities, Compromise Security, And Infiltrate Systems Undetected.
Once Installed, Diftefum.co.in Can Wreak Havoc Through Various Means, Including But Not Limited To:
Unauthorized Access: Diftefum.co.in May Grant Cybercriminals Unauthorized Access To Sensitive Information Stored On The Infected Device Or Network. Diftefum.co.in Could Include Personal Data, Financial Records, Or Proprietary Business Information.
System Instability: Rogue Programs Like Diftefum.co.in Are Notorious For Destabilizing Systems By Consuming Resources, Causing Crashes, Or Disrupting Essential Processes. Diftefum.co.in Can Lead To Significant Downtime, Productivity Losses, And Frustration For Users.
Malware Propagation: Diftefum.co.in May Serve As A Vector For Additional Malware, Facilitating Its Spread Across Interconnected Devices Or Networks. Diftefum.co.in Could Result In A Domino Effect Of Infections, Compounding The Damage Inflicted.
Financial Exploitation: Some Rogue Programs, Including Diftefum.co.in, Exploit Users For Financial Gain Through Tactics Such As Ad Fraud, Phishing, Or Ransom Demands. These Activities Not Only Harm Victims Financially But Also Erode Trust In Online Transactions And Services.
Privacy Breaches: Diftefum.co.in May Compromise User Privacy By Harvesting Sensitive Data Without Consent, Tracking Online Activities, Or Intercepting Communication. Such Violations Can Have Far-reaching Consequences, Including Identity Theft, Blackmail, Or Reputational Damage.
Detecting And Mitigating The Risks Associated With Rogue Programs Like Diftefum.co.in Requires A Multifaceted Approach Encompassing Both Proactive Measures And Reactive Responses.
Some Strategies Include:
Vigilant Monitoring: Employ Robust Cybersecurity Solutions Capable Of Detecting And Blocking Rogue Programs In Real-time. Diftefum.co.in Includes Antivirus Software, Intrusion Detection Systems, And Network Monitoring Tools.
User Education: Educate Users About The Dangers Of Rogue Programs And The Importance Of Exercising Caution When Downloading Software Or Clicking On Unfamiliar Links. Encourage Practices Such As Verifying The Legitimacy Of Sources And Regularly Updating Security Software.
Patch Management: Keep Software And Operating Systems Up To Date With The Latest Security Patches To Mitigate Known Vulnerabilities Exploited By Rogue Programs Like Diftefum.co.in. Implement A Proactive Patch Management Strategy To Minimize Exposure To Potential Threats.
Network Segmentation: Segment Networks To Limit The Impact Of Rogue Programs By Containing Infections Within Isolated Segments. Diftefum.co.in Prevents Lateral Movement And Mitigates The Spread Of Malware Across The Entire Network.
Incident Response Planning: Develop And Regularly Update An Incident Response Plan To Guide Actions In The Event Of A Rogue Program Infiltration. Diftefum.co.in Includes Procedures For Isolating Infected Systems, Restoring Backups, And Communicating With Stakeholders.
Rogue Programs Like Diftefum.co.in Pose A Significant Threat To Individuals And Organizations Alike, Exploiting Vulnerabilities For Financial Gain, Data Theft, And System Compromise.
By Understanding The Risks Associated With These Malicious Applications And Implementing Proactive Security Measures, Users Can Better Protect Themselves Against The Detrimental Effects Of Rogue Programs. Vigilance, Education, And Collaboration Are Key In Combating This Ever-evolving Threat Landscape.
Removing Malware From A Windows Computer Involves A Combination Of Using Antivirus Or Anti-malware Tools, Performing System Scans, And Taking Manual Actions To Eliminate The Malicious Software. Here's A Step-by-step Guide:
Ctrl + Shift + Esc To Open Task Manager.Win + R To Open The Run Dialog, Type cleanmgr, And Press Enter.Remember To Maintain Good Security Practices, Such As Keeping Your Operating System And Software Up-to-date, Using A Reputable Antivirus Program, And Being Cautious When Clicking On Links Or Downloading Files From The Internet. Regularly Backing Up Your Important Data Is Also Crucial To Mitigate The Impact Of Potential Infections.
If You Have Malwarebytes Installed On Your Computer And It Has Detected Malware, Follow These Steps To Remove The Malware:
Open Malwarebytes:
Update Malwarebytes:
Run A Threat Scan:
Review Scan Results:
Quarantine Or Remove Threats:
Reboot Your Computer:
Check For Persistence:
Monitor For Issues:
Clear Browser Data:
Reset Browser Settings:
Review Installed Programs:
Change Passwords:
Update Operating System:



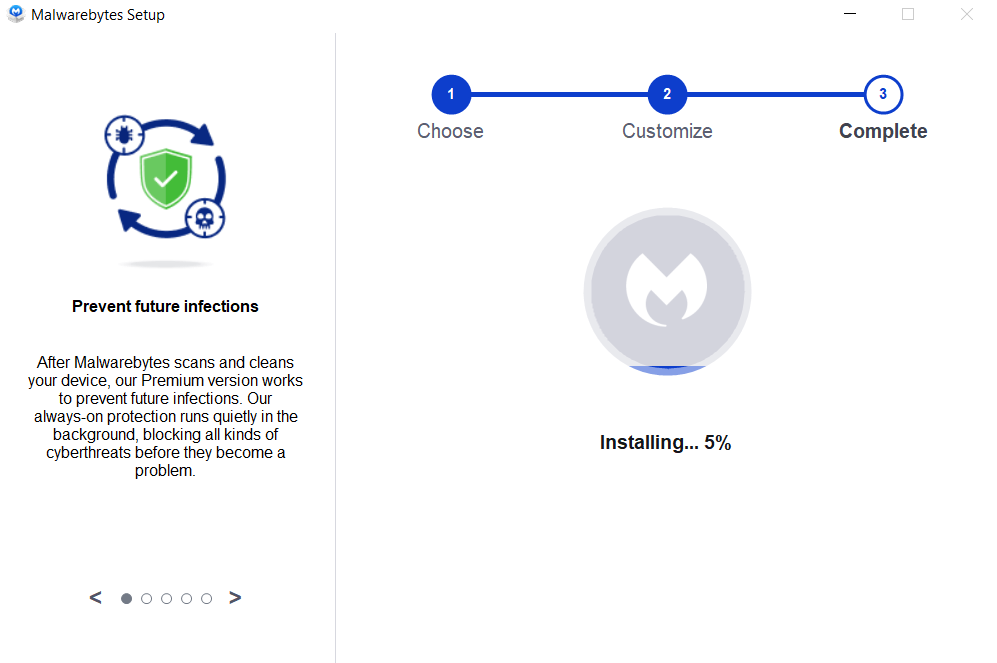
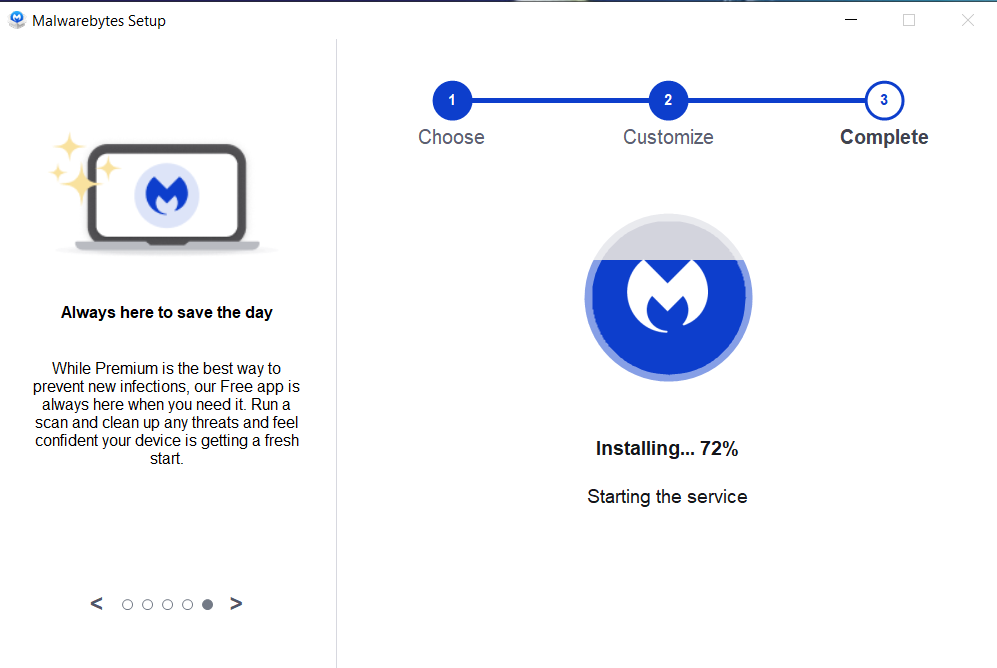
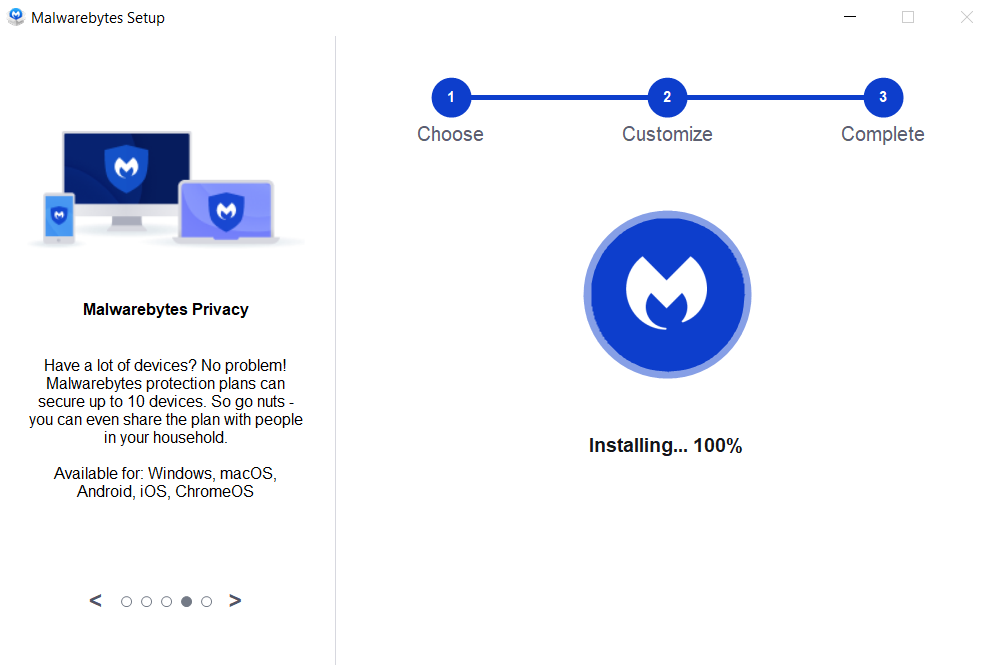

If The Malware Persists Or If You Encounter Difficulties During The Removal Process, You May Want To Seek Assistance From The Malwarebytes Support Community Or Consider Running Additional Scans Using Other Reputable Antivirus Or Anti-malware Tools. Remember To Keep Your Security Software Updated And Practice Safe Computing Habits To Minimize The Risk Of Future Infections.
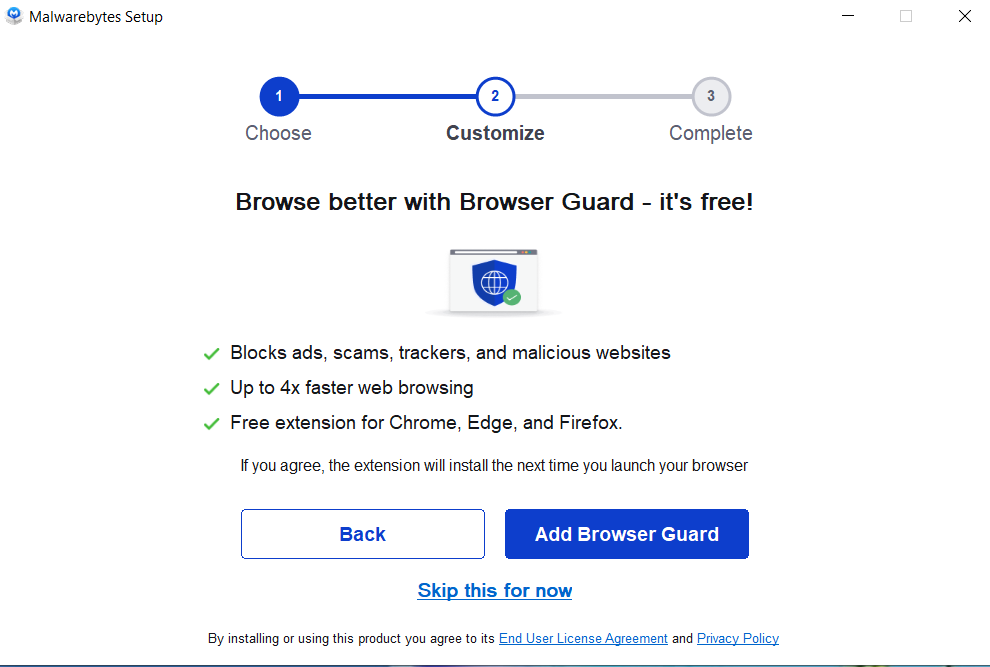
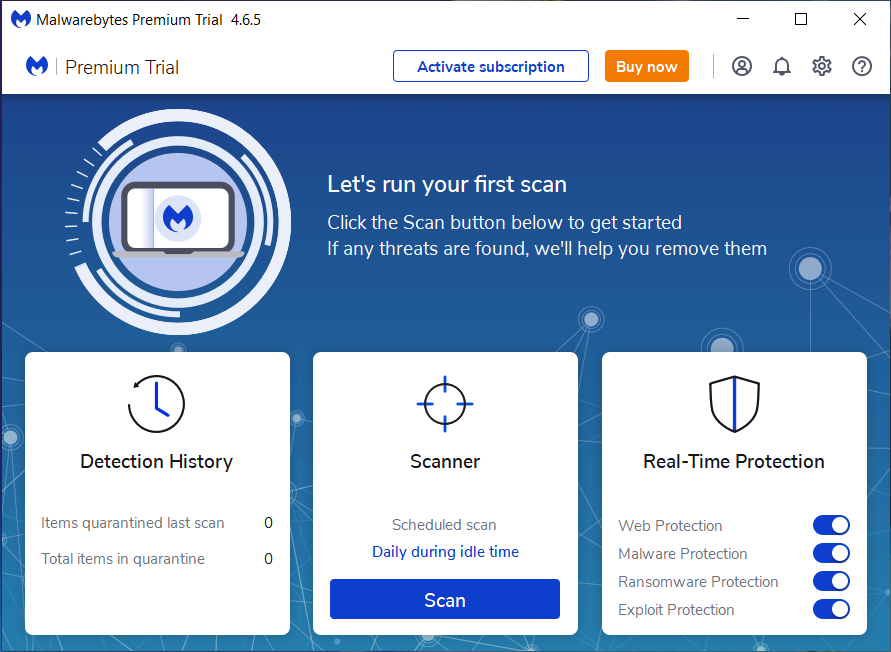
Malwarebytes Is A Leading Cybersecurity Solution Dedicated To Protecting Users From The Ever-evolving Landscape Of Digital Threats. With A Proven Track Record In Malware Detection And Removal, Malwarebytes Offers Cutting-edge Technology To Safeguard Computers And Devices Against Viruses, Ransomware, And Other Malicious Software.
Boasting A User-friendly Interface, Malwarebytes Provides A Seamless Experience For Both Novice And Advanced Users. Its Real-time Protection Capabilities, Coupled With Powerful Scanning Algorithms, Ensure That Users Are Shielded From The Latest Cybersecurity Threats. Malwarebytes Continually Updates Its Extensive Malware Database, Enabling Users To Stay Ahead Of Emerging Risks And Vulnerabilities.
Beyond malware Detection, Malwarebytes Offers Additional Features Such As Web Protection And Anti-exploit Technology, Fortifying Defenses Against Malicious Websites And Zero-day Exploits. The Software's Lightweight Footprint Ensures Minimal Impact On System Performance, Delivering Robust Security Without Compromising Speed.
Whether Used As A Standalone Solution Or In Conjunction With Other Cybersecurity Tools, Malwarebytes Remains A Trusted Ally In The Battle Against Cyber Threats. As A Proactive And Responsive Cybersecurity Partner, Malwarebytes Empowers Users To Navigate The Digital World With Confidence, Knowing That Their Data And Devices Are Safeguarded Against The Latest And Most Sophisticated Threats.
Diftefum.co.in, Diftefum.co.in Removal, Remove Diftefum.co.in, Understanding Rogue Programs, Risks, Effects, And Prevention Measures