 Blog's Page
Blog's Page

Your Personal Files Could Be In Jeopardy As The Infamous STOP/DJVU Ransomware Resurfaces With A Fresh Variant That Encrypts Images, Documents, And Crucial Files On Compromised Systems. This New Iteration Adds The ".CDPO" Extension To Encrypted File Names, Rendering Them Unreachable.
Upon Infection, The CDPO Ransomware Deposits A Ransom Note Labeled "readme.txt" On The Desktop. CDPO Ransomware Directs Victims To A Payment Website, Urging Them To Remit Payment In Bitcoin Cryptocurrency. Supposedly, This Payment Secures A Decryption Key Capable Of Restoring Access To The Encrypted Files.
CDPO Represents A File-encrypting Ransomware Infection That Locks Access To Vital Data Like Documents, Images, And Videos By Encrypting Files With The ".CDPO" Extension. CDPO Ransomware Subsequently Demands Ransom In Bitcoin Cryptocurrency In Exchange For Data Access Restoration.
Upon Initial Infection, CDPO Ransomware Scans The Victim's Computer For Critical Files Such As .doc, .docx, .xls, .pdf, Images, And Videos. Upon Detection, It Encrypts These Files, Appending The ".CDPO" Extension To Them, Rendering Them Inaccessible.
After Encrypting Your Computer's Files, The CDPO Ransomware Will Present The "_readme.txt" File Containing The Ransom Note And Instructions To Contact The Ransomware Authors. Victims Are Instructed To Reach Out To These Malicious Developers Via The support@fishmail.top And datarestorehelp@airmail.cc Email Addresses.
This Is The Ransom Note That The CDPO Ransomware Will Show To Its Victims:
ATTENTION!
Don’t Worry, You Can Return All Your Files!
All Your Files Like Pictures, Databases, Documents And Other Important Are Encrypted With Strongest Encryption And Unique Key.
The Only Method Of Recovering Files Is To Purchase Decrypt Tool And Unique Key For You.
This Software Will Decrypt All Your Encrypted Files.
What Guarantees You Have?
You Can Send One Of Your Encrypted File From Your PC And We Decrypt It For Free.
But We Can Decrypt Only 1 File For Free. File Must Not Contain Valuable Information.
You Can Get And Look Video Overview Decrypt Tool:
https://we.tl/t-oTIha7SI4s
Price Of Private Key And Decrypt Software Is $980.
Discount 50% Available If You Contact Us First 72 Hours, That’s Price For You Is $490.
Please Note That You’ll Never Restore Your Data Without Payment.
Check Your E-mail “Spam” Or “Junk” Folder If You Don’t Get Answer More Than 6 Hours.
To Get This Software You Need Write On Our E-mail:
support@fishmail.top
Reserve E-mail Address To Contact Us:
datarestorehelp@airmail.cc
Here Is A Summary Of The CDPO Ransomware:
Regrettably, Decrypting Files Encrypted By The CDPO Ransomware Is Presently Impossible. However, There's A Chance In The Future If Decryption Keys Are Retrieved From The Cybercriminals' Servers. Therefore, If You Opt Not To Pay The Ransom, It's Recommended To Create An Image Of The Encrypted Drives For Potential Future Decryption.
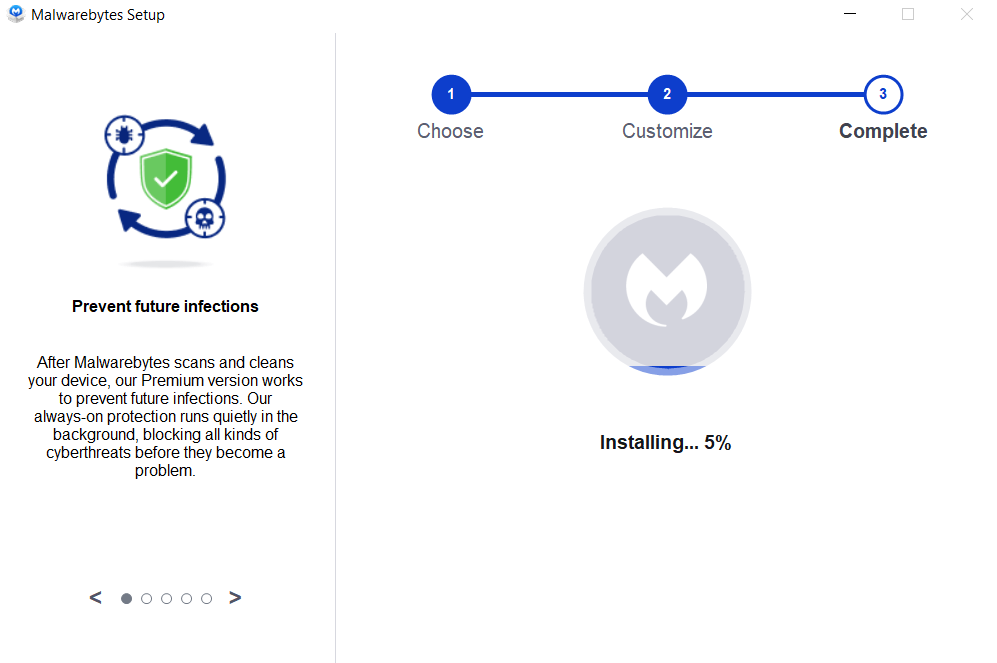
Removing Malware From A Windows Computer Involves A Combination Of Using Antivirus Or Anti-malware Tools, Performing System Scans, And Taking Manual Actions To Eliminate The Malicious Software. Here's A Step-by-step Guide:
Ctrl + Shift + Esc To Open Task Manager.Win + R To Open The Run Dialog, Type cleanmgr, And Press Enter.Remember To Maintain Good Security Practices, Such As Keeping Your Operating System And Software Up-to-date, Using A Reputable Antivirus Program, And Being Cautious When Clicking On Links Or Downloading Files From The Internet. Regularly Backing Up Your Important Data Is Also Crucial To Mitigate The Impact Of Potential Infections.
If You Have Malwarebytes Installed On Your Computer And It Has Detected Malware, Follow These Steps To Remove The Malware:
Open Malwarebytes:
Update Malwarebytes:
Run A Threat Scan:
Review Scan Results:
Quarantine Or Remove Threats:
Reboot Your Computer:
Check For Persistence:
Monitor For Issues:
Clear Browser Data:
Reset Browser Settings:
Review Installed Programs:
Change Passwords:
Update Operating System:



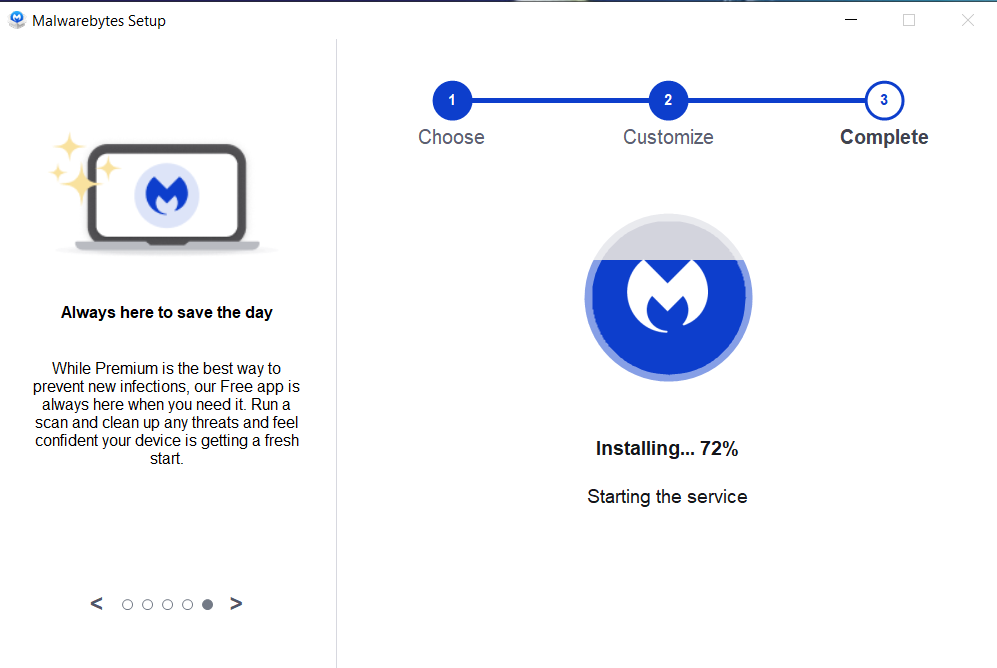

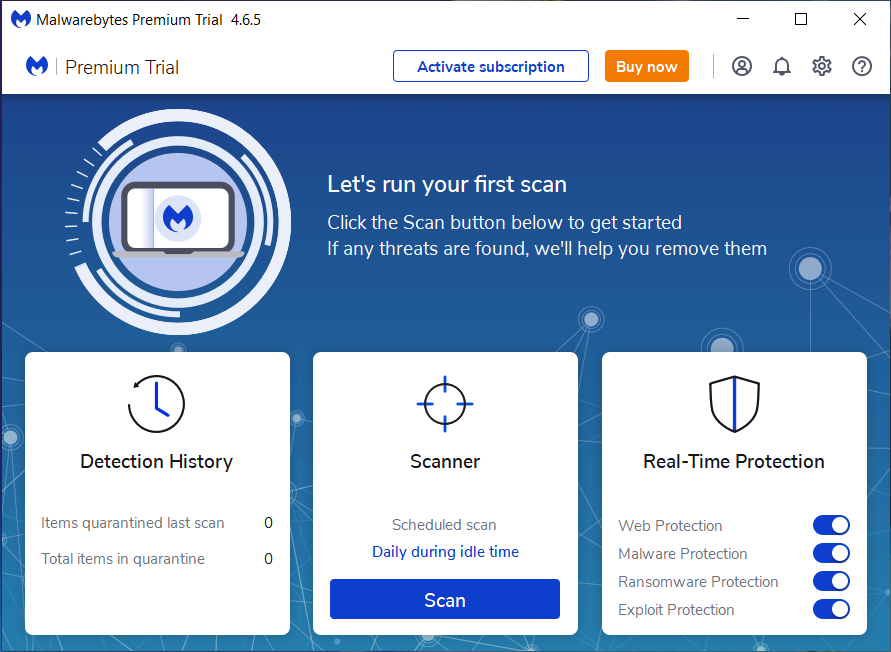
If The Malware Persists Or If You Encounter Difficulties During The Removal Process, You May Want To Seek Assistance From The Malwarebytes Support Community Or Consider Running Additional Scans Using Other Reputable Antivirus Or Anti-malware Tools. Remember To Keep Your Security Software Updated And Practice Safe Computing Habits To Minimize The Risk Of Future Infections.
Malwarebytes Is A Leading Cybersecurity Solution Dedicated To Protecting Users From The Ever-evolving Landscape Of Digital Threats. With A Proven Track Record In Malware Detection And Removal, Malwarebytes Offers Cutting-edge Technology To Safeguard Computers And Devices Against Viruses, Ransomware, And Other Malicious Software.
Boasting A User-friendly Interface, Malwarebytes Provides A Seamless Experience For Both Novice And Advanced Users. Its Real-time Protection Capabilities, Coupled With Powerful Scanning Algorithms, Ensure That Users Are Shielded From The Latest Cybersecurity Threats. Malwarebytes Continually Updates Its Extensive Malware Database, Enabling Users To Stay Ahead Of Emerging Risks And Vulnerabilities.
Beyond malware Detection, Malwarebytes Offers Additional Features Such As Web Protection And Anti-exploit Technology, Fortifying Defenses Against Malicious Websites And Zero-day Exploits. The Software's Lightweight Footprint Ensures Minimal Impact On System Performance, Delivering Robust Security Without Compromising Speed.
Whether Used As A Standalone Solution Or In Conjunction With Other Cybersecurity Tools, Malwarebytes Remains A Trusted Ally In The Battle Against Cyber Threats. As A Proactive And Responsive Cybersecurity Partner, Malwarebytes Empowers Users To Navigate The Digital World With Confidence, Knowing That Their Data And Devices Are Safeguarded Against The Latest And Most Sophisticated Threats.
CDPO Ransomware, Remove CDPO Ransomware, Uninstall CDPO Ransomware, Delete CDPO Ransomware, Get Rid Of CDPO Ransomware, CDPO Ransomware Removal