 Blog's Page
Blog's Page
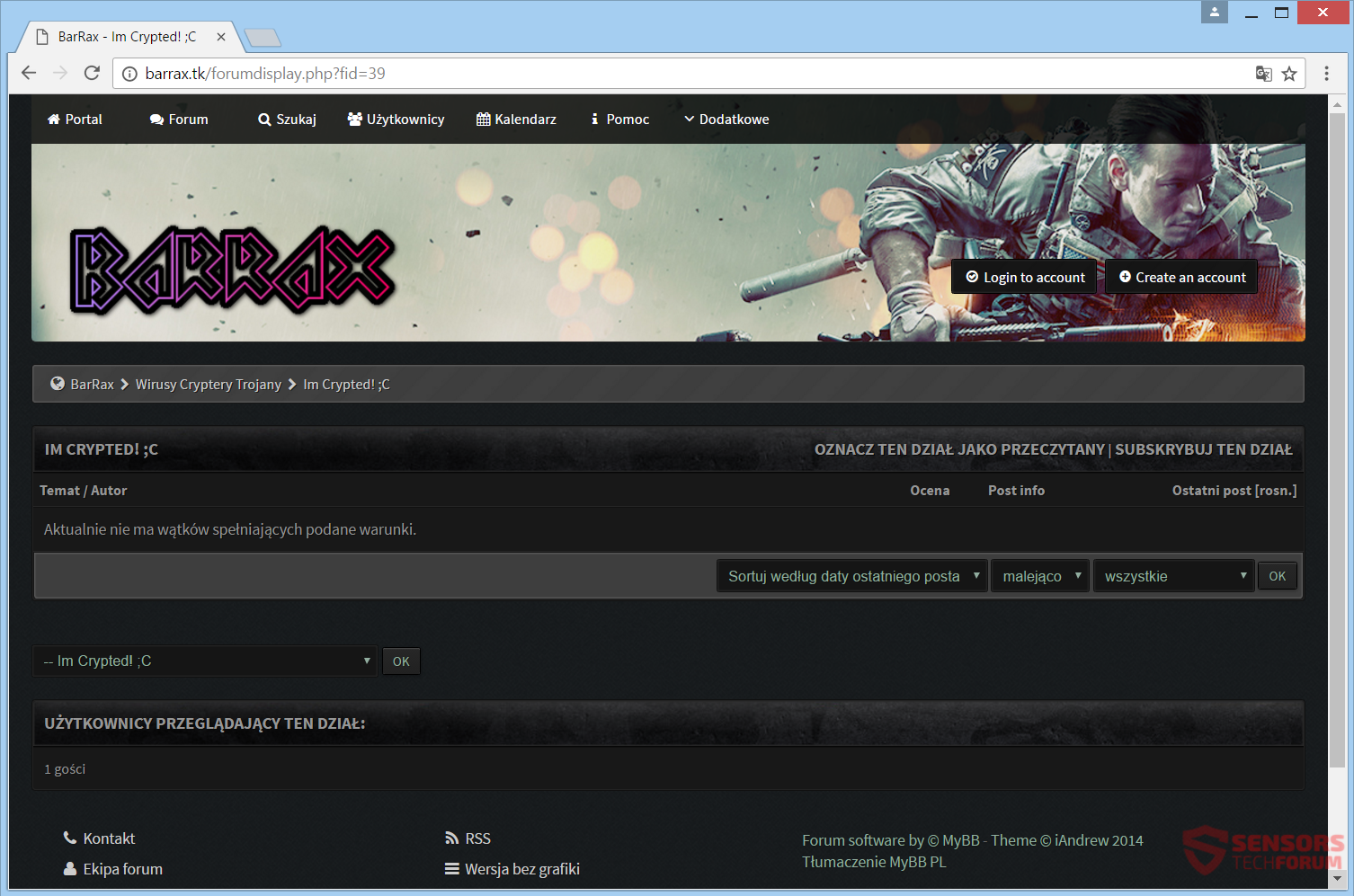
The Barrax Ransomware Is Part Of The Extensive Lineage Of HiddenTear, An Open-source Ransomware Engine Initially Released In 2015 For Purported 'educational Purposes.' Regrettably, Since Its Public Release, HiddenTear Has Served As The Foundation For Numerous Threats, And The Barrax Ransomware Is Just One Among The Many Barrax Ransomware Trojans That Emerged After HiddenTear's Introduction In August 2015.
Introduced In February 2017, The Barrax Ransomware Is Likely Disseminated Through Corrupted Email Attachments And Bundled With Free Software Or Media Distributed Online, Often Via File-sharing Websites And Networks.
Upon Infecting A Computer, The Barrax Ransomware Employs Tactics Rendering The Victim's Files Entirely Inaccessible, Compelling A Ransom Payment. This Characteristic Makes Barrax Ransomware And Similar Ransomware Trojans Exceptionally Perilous.
Even If Barrax Ransomware Infection Is Successfully Eradicated With The Assistance Of A Reliable Security Application, The Compromised Files Remain Inaccessible, Underscoring The Persistent Threat Posed By Such Ransomware Attacks.
Primarily Tailored For Computers Operating On A 32-bit Version Of The Windows Operating System, The Barrax Ransomware, Nonetheless, Has The Capability To Run On 64-bit Windows Versions As Well. Compact In Size, The Barrax Ransomware Utilizes A Combination Of AES-256 And RSA-2048 Encryptions To Render Victims' Files Entirely Inaccessible.
The Executable File Associated With The Barrax Ransomware Is Identified As 'BarraxCrpt.exe,' Although Certain Versions May Forego Re-branding The Original HiddenTear Source And Utilize A File Named 'hidden-tear.exe' To Execute The Encryption Attack.
Remarkably, The Barrax Ransomware Can Be Configured To Conduct Diverse Attacks, Targeting Various File Types Or Presenting Distinct Ransom Messages Following Each Attack.
In The Case Of The Most Common Version Of The Barrax Ransomware Being Distributed, The Following File Types Will Be Targeted During The Attack:
.3GP, .7Z, .APK, .AVI, .BMP, .CDR, .CER, .CHM, .CONF, .CSS, .CSV, .DAT, .DB, .DBF, .DJVU, .DBX, .DOCM, ,DOC, .EPUB, .DOCX .FB2, .FLV, .GIF, .GZ, .ISO .IBOOKS,.JPEG, .JPG, .KEY, .MDB .MD2, .MDF, .MHT, .MOBI .MHTM, .MKV, .MOV, .MP3, .MP4, .MPG .MPEG, .PICT, .PDF, .PPS, .PKG, .PNG, .PPT .PPTX, .PPSX, .PSD, .RAR, .RTF, .SCR, .SWF, .SAV, .TIFF, .TIF, .TBL, .TORRENT, .TXT, .VSD,.WMV, .XLS, .XLSX, .XPS, .XML, .CKP, .ZIP, .JAVA, .PY, .ASM, .C, .CPP, .CS, .JS, .PHP, .DACPAC, .RBW, .RB, .MRG, .DCX, .DB3, .SQL, .SQLITE3, .SQLITE, .SQLITEDB, .PSD, .PSP, .PDB, .DXF, .DWG, .DRW, .CASB, .CCP, .CAL, .CMX, .CR2.
The Barrax Ransomware Executes Its Attack By Primarily Targeting Computers Running A 32-bit Version Of The Windows Operating System, Although It Is Also Compatible With 64-bit Windows Versions.Enclosed Within A Compact File, It Employs A Combination Of AES-256 And RSA-2048 Encryptions To Render Victims' Files Completely Inaccessible.
The Executable File, Commonly Known As 'BarraxCrpt.exe,' Is The Identified Component Of The Barrax Ransomware, Although Certain Versions May Opt To Use 'hidden-tear.exe' Without Re-branding The Original HiddenTear Source During The Encryption Attack.
Notably, The Barrax Ransomware Can Be Customized To Carry Out Diverse Attacks, Targeting Different File Types Or Presenting Distinct Ransom Messages With Each Assault.
Regrettably, Once Files Have Been Compromised By A Threat Such As The Barrax Ransomware, Recovery Without The Decryption Key May Prove Impossible. Nevertheless, It Is Crucial For Computer Users To Avoid Paying The Ransom Imposed By Barrax Ransomware, As Succumbing To Such Demands Perpetuates The Creators' Ability To Generate Threats And Victimize Others.
Mandatory Protective Measures For Computer Users Include Maintaining Backups Of All Files On An Offline Storage Device And Installing A Dependable Security Program To Mitigate The Impact Of A Barrax Ransomware Attack.
This Black Friday VPN Deals 2023, Fortify Your Online Security With Exclusive VPN Deals! Unlock Discounts On Top-tier Services, Ensuring Private And Unrestricted Internet Access. Black Friday VPN Deals 2023, Browse Anonymously, Safeguard Sensitive Data, And Enjoy Seamless Streaming With Lightning-fast Speeds. Don't Miss Out On These Limited-time Offers—invest In Your Digital Privacy This Black Friday VPN Deals 2023 And Enjoy A Safer Online Experience. Read More...
Removing Malware From A Windows Computer Involves A Combination Of Using Antivirus Or Anti-malware Tools, Performing System Scans, And Taking Manual Actions To Eliminate The Malicious Software. Here's A Step-by-step Guide:
Ctrl + Shift + Esc To Open Task Manager.Win + R To Open The Run Dialog, Type cleanmgr, And Press Enter.Remember To Maintain Good Security Practices, Such As Keeping Your Operating System And Software Up-to-date, Using A Reputable Antivirus Program, And Being Cautious When Clicking On Links Or Downloading Files From The Internet. Regularly Backing Up Your Important Data Is Also Crucial To Mitigate The Impact Of Potential Infections.
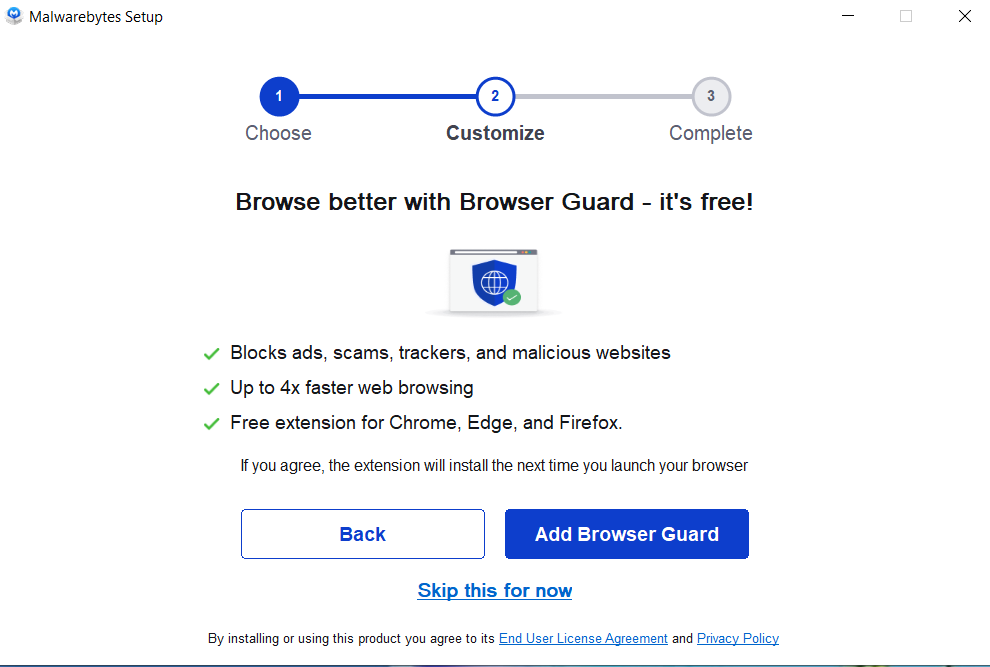
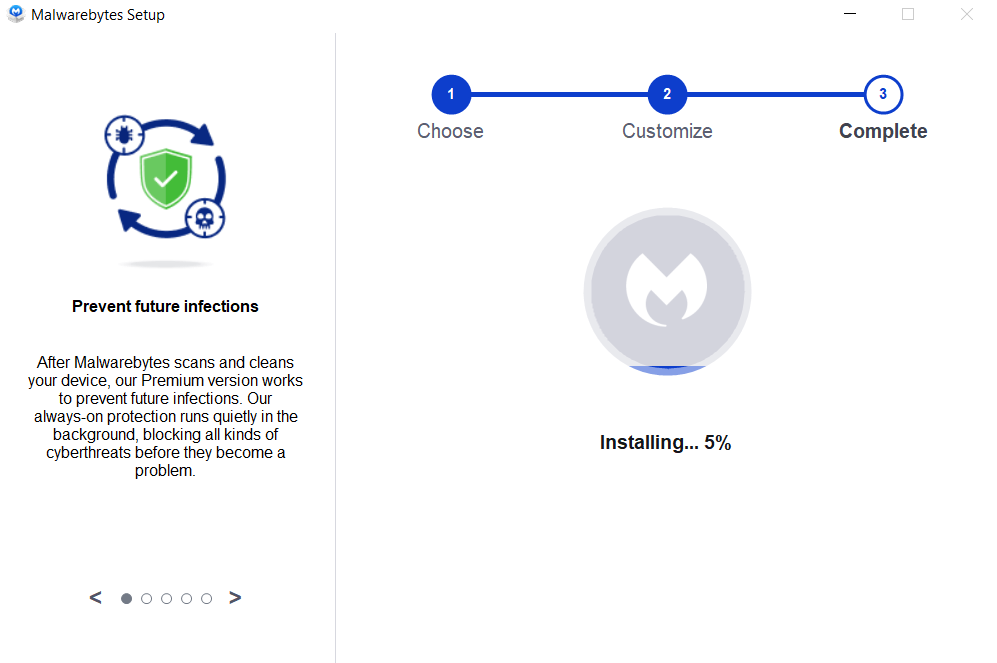
If You Have Malwarebytes Installed On Your Computer And It Has Detected Malware, Follow These Steps To Remove The Malware:
Open Malwarebytes:
Update Malwarebytes:
Run A Threat Scan:
Review Scan Results:
Quarantine Or Remove Threats:
Reboot Your Computer:
Check For Persistence:
Monitor For Issues:
Clear Browser Data:
Reset Browser Settings:
Review Installed Programs:
Change Passwords:
Update Operating System:



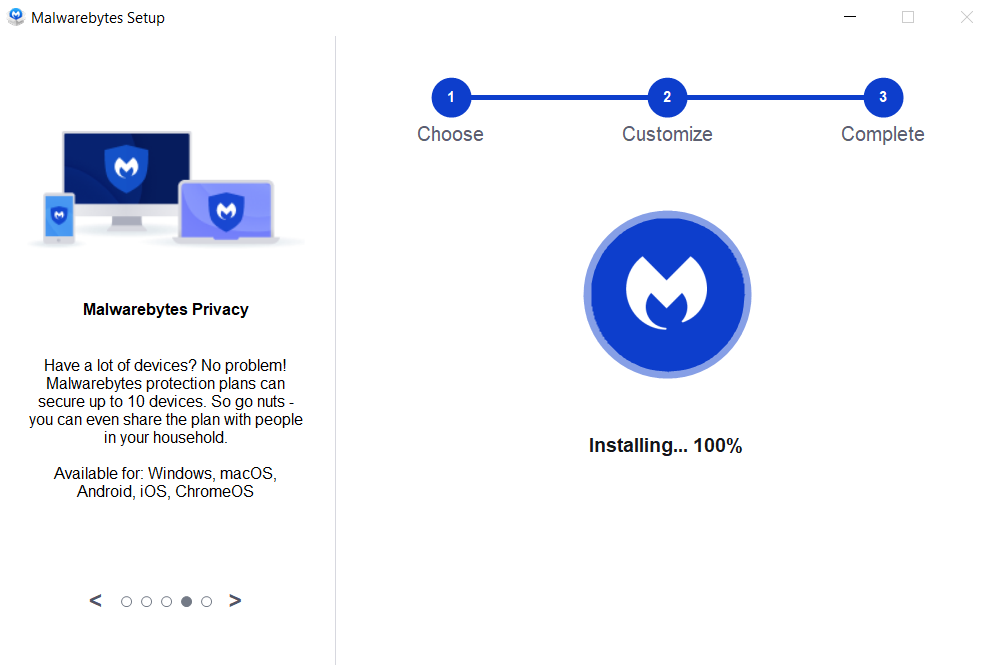

If The Malware Persists Or If You Encounter Difficulties During The Removal Process, You May Want To Seek Assistance From The Malwarebytes Support Community Or Consider Running Additional Scans Using Other Reputable Antivirus Or Anti-malware Tools. Remember To Keep Your Security Software Updated And Practice Safe Computing Habits To Minimize The Risk Of Future Infections.
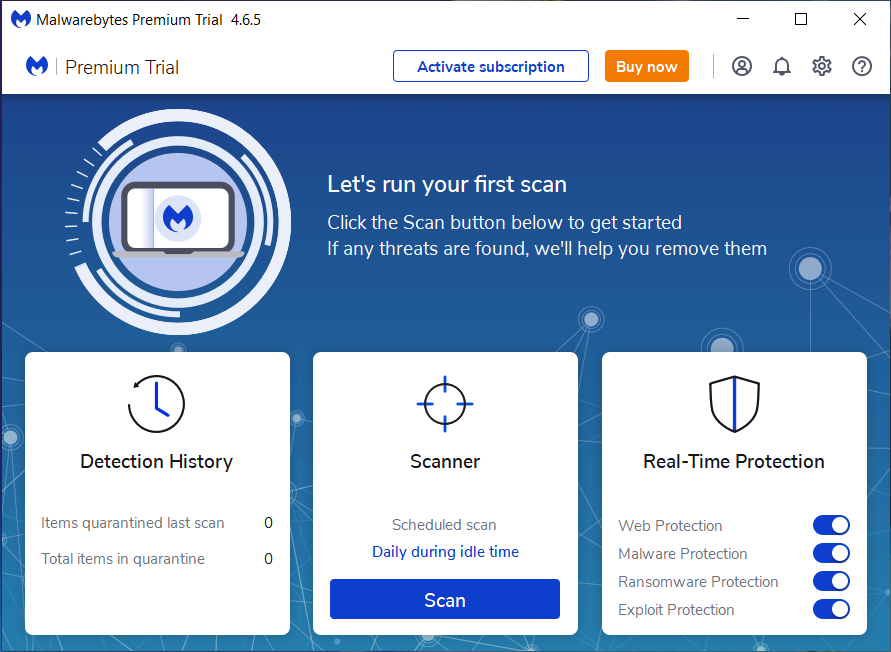
Malwarebytes Is A Leading Cybersecurity Solution Dedicated To Protecting Users From The Ever-evolving Landscape Of Digital Threats. With A Proven Track Record In Malware Detection And Removal, Malwarebytes Offers Cutting-edge Technology To Safeguard Computers And Devices Against Viruses, Ransomware, And Other Malicious Software.
Boasting A User-friendly Interface, Malwarebytes Provides A Seamless Experience For Both Novice And Advanced Users. Its Real-time Protection Capabilities, Coupled With Powerful Scanning Algorithms, Ensure That Users Are Shielded From The Latest Cybersecurity Threats. Malwarebytes Continually Updates Its Extensive Malware Database, Enabling Users To Stay Ahead Of Emerging Risks And Vulnerabilities.
Beyond malware Detection, Malwarebytes Offers Additional Features Such As Web Protection And Anti-exploit Technology, Fortifying Defenses Against Malicious Websites And Zero-day Exploits. The Software's Lightweight Footprint Ensures Minimal Impact On System Performance, Delivering Robust Security Without Compromising Speed.
Whether Used As A Standalone Solution Or In Conjunction With Other Cybersecurity Tools, Malwarebytes Remains A Trusted Ally In The Battle Against Cyber Threats. As A Proactive And Responsive Cybersecurity Partner, Malwarebytes Empowers Users To Navigate The Digital World With Confidence, Knowing That Their Data And Devices Are Safeguarded Against The Latest And Most Sophisticated Threats.
Barrax Ransomware, Remove Barrax Ransomware, Uninstall Barrax Ransomware, Delete Barrax Ransomware, Barrax Ransomware Removal