 Blog's Page
Blog's Page

The AES-Matrix Ransomware Was Initially Detected By PC Security Researchers On July 7, 2017. It Appears To Have Connections To An Earlier Ransomware Trojan Called The GruxEr Ransomware, Which Was First Identified In May 2017.
Throughout 2017, There Has Been A Notable Surge In Encryption Ransomware Trojans, With The AES-Matrix Ransomware Being One Of Several Instances. AES-Matrix Ransomware Increase In Infections Correlates With A Rise In Bitcoin Prices, Often Utilized For The Associated Payments.
The Primary Targets Of The AES-Matrix Ransomware Are Small And Medium Businesses. AES-Matrix Ransomware Propagation Is Predominantly Linked To Exploiting Inadequately Secured Remote Desktop Protocol Connections.
Exploiting Weak Password Protection Or Poorly Implemented Security Measures, Malicious Actors Exploit These Vulnerabilities To Implant The AES-Matrix Ransomware On The Servers Of Targeted Companies. Notably, AES-Matrix Ransomware Is Not Confined To Corporate Entities And Is Also A Threat To Individual Computer Users.
After Being Installed On A Computer, The AES-Matrix Ransomware Employs AES 256 Encryption To Render The Victim's Files Inaccessible. AES-Matrix Ransomware Scans Local Drives And Network Shared Directories To Encrypt Files, Encompassing Databases, Configuration Files, Images, Videos, Audio, And Files Linked To Widely Used Software.
Once The Victim's Files Are Encrypted, The AES-Matrix Ransomware Demands A Ransom. Notably, AES-Matrix Ransomware Targets User-generated Files And Exhibits Similarities To HiddenTear, An Open-source Ransomware Platform That Has Given Rise To Numerous Ransomware Trojans.
However, Unlike Typical HiddenTear Variants, The AES-Matrix Ransomware Does Not Employ Custom Extensions Or Perform Comparable Tasks On The Affected Files.
The AES-Matrix Ransomware Will Deliver A Ransom Note To The Victim, Informing The Victim Of The Attack And Demanding The Payment Of A Ransom From The Victim. The Following Is The Ransom Note That Has Been Linked To The AES-Matrix Ransomware Attack:
'Hello,
Your All Datas Have Been Encrypted By AES-256 Key,
If You Want To Decrypt By Yourselft, It Would Take Hundred Years,
If You Can Pay Some Money, I Will Send You The Decrypt Key, You Can Get Your Data Back Immediately.
According To The CyberEdge Group's 2017 Cyberthreat Defense Report, 1/3 Company Paid A Ransom.
So It Is Not Shame To Pay Ransom,many Company Paid It Before.
Your Are So Large Security Safes Company.
Now Would You Like To See Your Business Become Like A Startup Or Just Pay To Continue Your Business?
Contact My Email: Darkpart@tutanota.com Or Darkware@tutanota.com
If You Do Not Contact Me Soon, You Key Will Be Deleted Automaticly By System And You Will Lose Your Data 4ever.
Just Take It As Security Consultant Fee. They Charge Much More Than Me.'
The Ransom Note Of The AES-Matrix Ransomware Incorporates Images Linked To 'The Matrix' Movie Series, From Which The Ransomware Derives Its Name. Demanding A Payment Of 250 USD In Bitcoins, The AES-Matrix Ransomware Employs Fabricated Statistics To Deceive Computer Users Into Complying With The Ransom Demand. Nevertheless, It Is Advisable For Computer Users To Refrain From Paying The Ransom Imposed By The AES-Matrix Ransomware.
There Are Multiple Compelling Reasons For Computer Users To Refrain From Paying The Ransom Demanded By AES-Matrix Ransomware. In Most Cases, The Perpetrators Rarely Provide The Data Even After Receiving Payment.
Moreover, Yielding To The Ransom Demand Enables These Individuals To Persist In Creating Such Infections And Victimizing Others. Instead, malware Analysts Strongly Recommend That Computer Users Establish A Dependable Backup System.
Maintaining File Backups Proves To Be The Most Effective Defense Against Threats Like AES-Matrix Ransomware, As Users Can Restore Their Files From The Backup, Eliminating The Need To Pay The Ransom. This Proactive Approach Removes Any Leverage That Extortionists Might Exploit, Providing A Robust Defense Against Such Attacks.
This Black Friday VPN Deals 2023, Fortify Your Online Security With Exclusive VPN Deals! Unlock Discounts On Top-tier Services, Ensuring Private And Unrestricted Internet Access. Black Friday VPN Deals 2023, Browse Anonymously, Safeguard Sensitive Data, And Enjoy Seamless Streaming With Lightning-fast Speeds. Don't Miss Out On These Limited-time Offers—invest In Your Digital Privacy This Black Friday VPN Deals 2023 And Enjoy A Safer Online Experience. Read More...
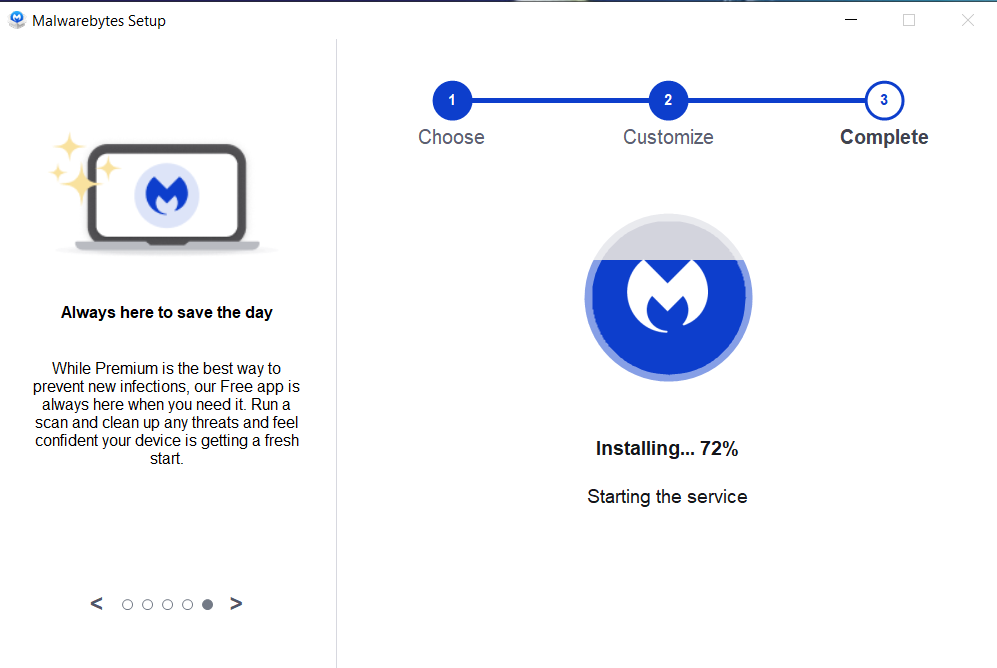
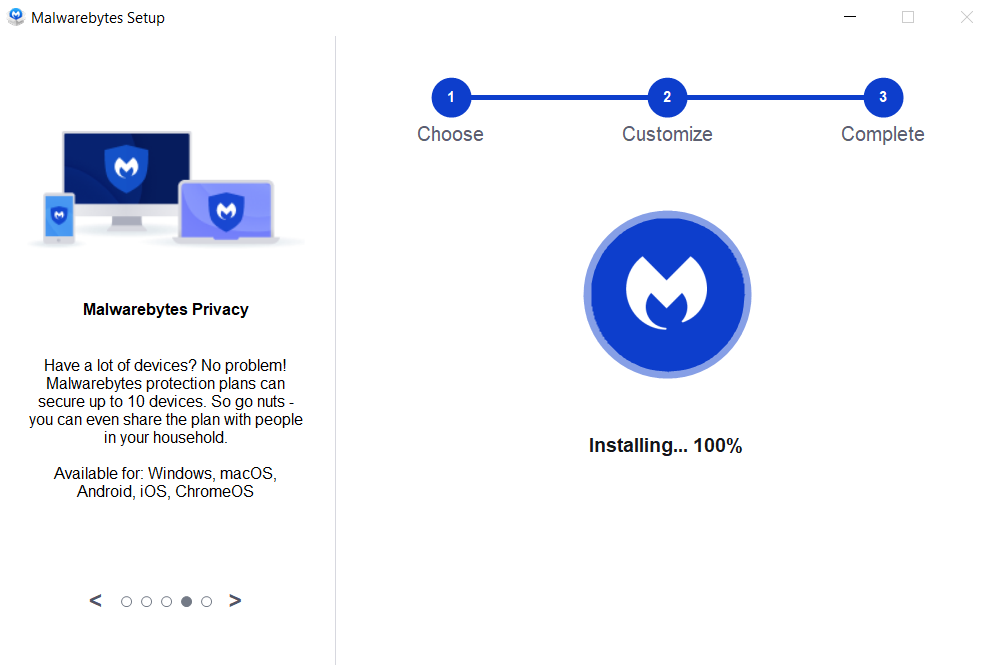
Removing Malware From A Windows Computer Involves A Combination Of Using Antivirus Or Anti-malware Tools, Performing System Scans, And Taking Manual Actions To Eliminate The Malicious Software. Here's A Step-by-step Guide:
Ctrl + Shift + Esc To Open Task Manager.Win + R To Open The Run Dialog, Type cleanmgr, And Press Enter.Remember To Maintain Good Security Practices, Such As Keeping Your Operating System And Software Up-to-date, Using A Reputable Antivirus Program, And Being Cautious When Clicking On Links Or Downloading Files From The Internet. Regularly Backing Up Your Important Data Is Also Crucial To Mitigate The Impact Of Potential Infections.
If You Have Malwarebytes Installed On Your Computer And It Has Detected Malware, Follow These Steps To Remove The Malware:
Open Malwarebytes:
Update Malwarebytes:
Run A Threat Scan:
Review Scan Results:
Quarantine Or Remove Threats:
Reboot Your Computer:
Check For Persistence:
Monitor For Issues:
Clear Browser Data:
Reset Browser Settings:
Review Installed Programs:
Change Passwords:
Update Operating System:



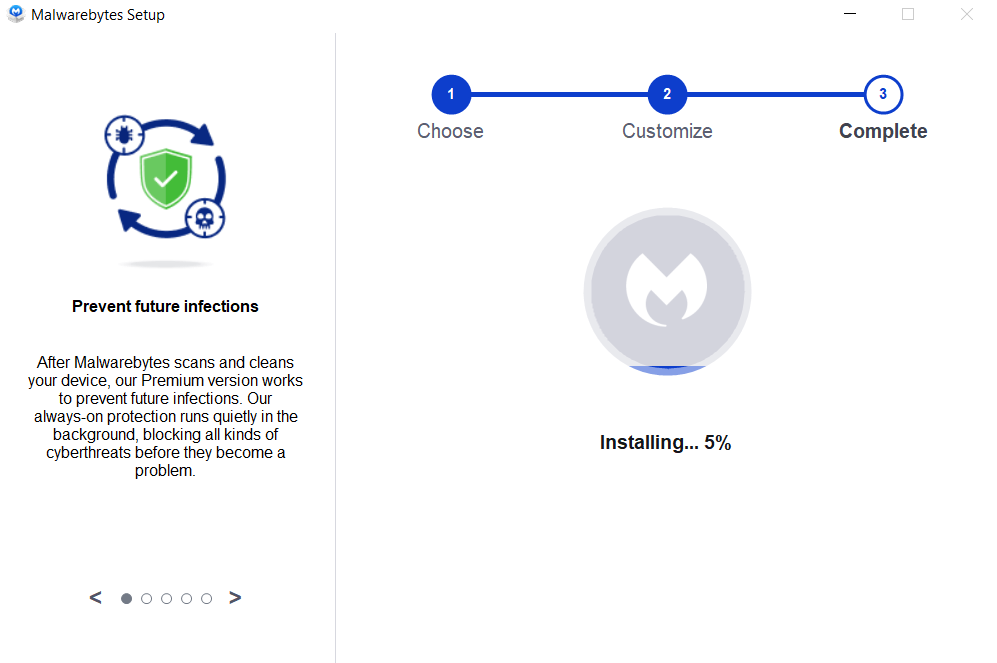

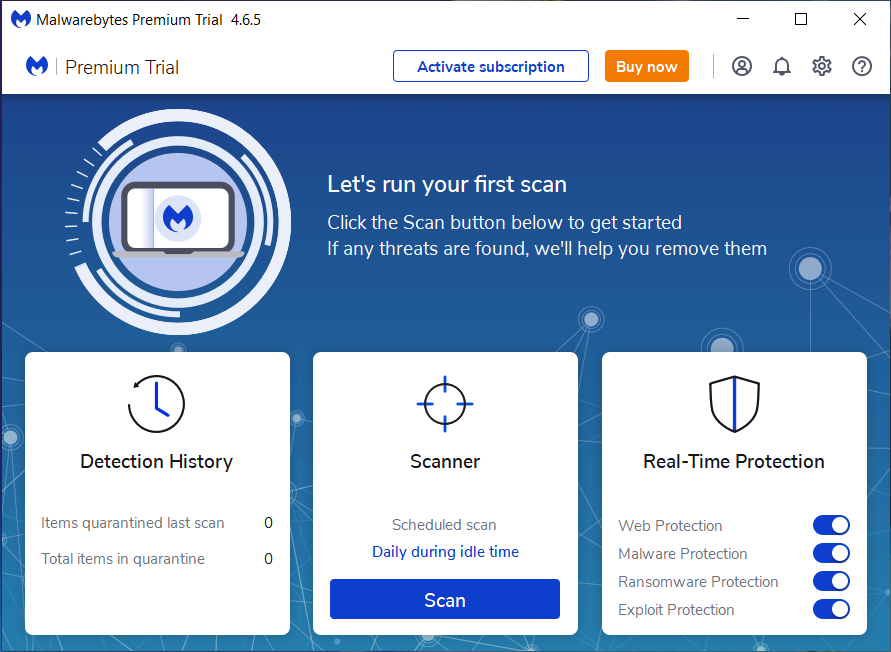
If The Malware Persists Or If You Encounter Difficulties During The Removal Process, You May Want To Seek Assistance From The Malwarebytes Support Community Or Consider Running Additional Scans Using Other Reputable Antivirus Or Anti-malware Tools. Remember To Keep Your Security Software Updated And Practice Safe Computing Habits To Minimize The Risk Of Future Infections.
Malwarebytes Is A Leading Cybersecurity Solution Dedicated To Protecting Users From The Ever-evolving Landscape Of Digital Threats. With A Proven Track Record In Malware Detection And Removal, Malwarebytes Offers Cutting-edge Technology To Safeguard Computers And Devices Against Viruses, Ransomware, And Other Malicious Software.
Boasting A User-friendly Interface, Malwarebytes Provides A Seamless Experience For Both Novice And Advanced Users. Its Real-time Protection Capabilities, Coupled With Powerful Scanning Algorithms, Ensure That Users Are Shielded From The Latest Cybersecurity Threats. Malwarebytes Continually Updates Its Extensive Malware Database, Enabling Users To Stay Ahead Of Emerging Risks And Vulnerabilities.
Beyond malware Detection, Malwarebytes Offers Additional Features Such As Web Protection And Anti-exploit Technology, Fortifying Defenses Against Malicious Websites And Zero-day Exploits. The Software's Lightweight Footprint Ensures Minimal Impact On System Performance, Delivering Robust Security Without Compromising Speed.
Whether Used As A Standalone Solution Or In Conjunction With Other Cybersecurity Tools, Malwarebytes Remains A Trusted Ally In The Battle Against Cyber Threats. As A Proactive And Responsive Cybersecurity Partner, Malwarebytes Empowers Users To Navigate The Digital World With Confidence, Knowing That Their Data And Devices Are Safeguarded Against The Latest And Most Sophisticated Threats.
AES-Matrix Ransomware, Remove AES-Matrix Ransomware, AES-Matrix Ransomware Removal, Uninstall AES-Matrix Ransomware, Delete AES-Matrix Ransomware| Links1 | Links2 | Links3 | Products | Social Links |
|---|---|---|---|---|
| Home | Blog | Sitemap | Email Checker Tool | |
| About | CSI Links | ISRO Project Code: AA0802 | Offers | |
| Disclaimer | Gallery | Contact Us | Antivirus | |
| Privacy Policy | Software Downloads |