 Blog's Page
Blog's Page
Cybersecurity Threats Continue To Evolve As Hackers Develop More Advanced Ways To Infiltrate Systems And Steal Sensitive Data. One Such Threat That Has Gained Attention In The Cybersecurity World Is The Nivdort Trojan Virus. This Malicious Software Is Known For Its Ability To Hide Deep Within A System, Steal Personal Information, And Allow Cybercriminals To Control Infected Computers Remotely.
In This Guide, We Will Explore Everything You Need To Know About The Nivdort Trojan, Including How It Works, How It Infects Devices, Signs Of Infection, And The Best Ways To Remove And Prevent It.
The Nivdort Trojan Is A Type Of Trojan Horse Malware Designed To Secretly Infiltrate Computers And Create A Backdoor For Hackers. Once Installed, It Can Perform A Variety Of Malicious Activities, Including Stealing Financial Data, Logging Keystrokes, Downloading Additional Malware, And Giving Attackers Remote Control Of The Infected System.
Unlike Traditional Viruses That Spread Automatically, Trojans Rely On social Engineering Techniques To Trick Users Into Installing Them. Nivdort Often Disguises Itself As Legitimate Software, Email Attachments, Or Downloads From Compromised Websites.
Cybersecurity Researchers Have Categorized Nivdort As A banking Trojan, As It Frequently Targets Online Banking Credentials And Financial Information.
The Nivdort Trojan First Appeared In Cybersecurity Reports In The Early 2010s. It Was Detected By Several Security Companies After Infected Systems Began Sending Suspicious Traffic To Remote Command-and-control Servers.
Over Time, Different Variants Of The Trojan Have Emerged, Each With Enhanced Capabilities And Improved Stealth Techniques. Hackers Continuously Update The Malware To Evade Antivirus Detection And Exploit New Vulnerabilities.
Although Its Exact Creators Remain Unknown, Cybersecurity Analysts Believe It Was Developed By Organized Cybercriminal Groups Focused On Financial Fraud And Data Theft.
Once The Nivdort Trojan Infiltrates A Computer, It Performs Several Steps To Establish Control And Avoid Detection.
The Infection Usually Begins When A User Unknowingly Downloads Or Opens A Malicious File. This File Installs The Trojan Silently In The Background.
After Installation, The Malware Modifies System Files And Registry Settings To Ensure It Runs Every Time The Computer Starts.
Nivdort Connects To Remote command-and-control (C2) Servers Operated By Hackers. Through These Servers, Attackers Can Send Instructions To The Infected Machine.
The Trojan Collects Sensitive Information From The System, Including:
Login Credentials
Banking Information
Browser Cookies
Email Accounts
Keystrokes Typed By The User
Hackers Can Remotely Control The Infected Computer To:
Download Additional Malware
Send Spam Emails
Participate In Botnet Attacks
Monitor User Activity
Like Most Trojan Malware, Nivdort Relies Heavily On deception Techniques To Trick Users. Here Are The Most Common Infection Methods.
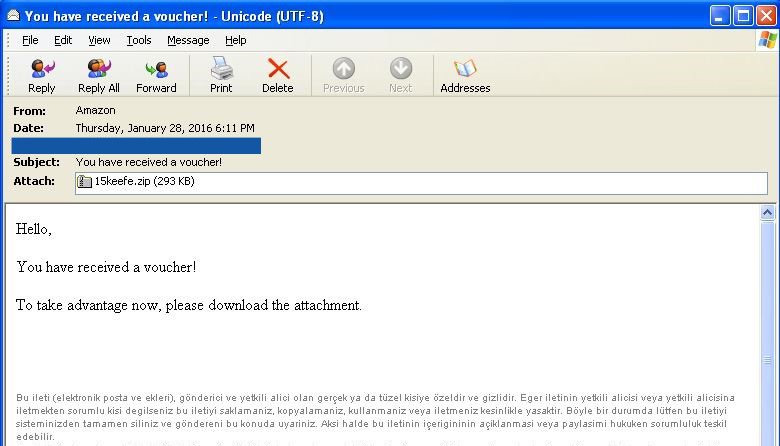
Cybercriminals Often Distribute The Trojan Through Phishing Emails. These Emails May Contain Attachments Disguised As Invoices, Documents, Or Shipping Notifications.
Once The Attachment Is Opened, The Trojan Installs Itself Silently.
Another Common Method Is Distributing Nivdort Through Fake Software Installers Or Cracked Software Downloads.
Users Looking For Free Software Versions May Unknowingly Install The Trojan.
Hackers Sometimes Inject Malicious Scripts Into Legitimate Websites. When Users Visit These Sites, The Malware May Download Automatically.
Some Websites Exploit Browser Vulnerabilities To Install Malware Without Requiring Any User Interaction.
Detecting Trojan Infections Can Be Difficult Because They Are Designed To Operate Stealthily. However, There Are Several Warning Signs That May Indicate A System Infection.
If Your Computer Suddenly Becomes Extremely Slow Without Any Obvious Reason, Malware Could Be Consuming System Resources.
Nivdort Constantly Communicates With Remote Servers. Unusual Network Activity Or High Internet Usage May Indicate Infection.
If You Notice Unfamiliar Applications Or Processes In Your System, It Could Be A Sign Of Malware.
Some Trojan Variants Disable Antivirus Or Firewall Protections To Avoid Detection.
Users May Notice That Their Browser Redirects To Suspicious Websites Or Displays Unusual Pop-ups.
The Nivdort Trojan Is Particularly Dangerous Because It Can Compromise Both Personal And Financial Data. Some Of The Major Risks Include:
By Capturing Login Credentials And Personal Data, Attackers Can Impersonate Victims Online.
Banking Trojans Like Nivdort Are Designed To Steal Financial Information Such As Credit Card Numbers And Online Banking Passwords.
Infected Computers May Become Part Of A Botnet Used To Perform Large-scale Cyberattacks Such As distributed Denial-of-service (DDoS) Attacks.
Sensitive Files Stored On Infected Systems May Be Stolen Or Leaked.
If You Suspect Your Computer Is Infected, It Is Important To Act Quickly To Remove The Malware.
Disconnecting From The Internet Prevents The Trojan From Communicating With Remote Servers.
Restart Your Computer In Safe Mode To Prevent Malicious Programs From Launching Automatically.
Use A Reputable Antivirus Or Anti-malware Program To Scan The Entire System.
If The Antivirus Detects Nivdort Or Related Malware, Follow The Recommended Steps To Quarantine And Remove It.
After Removal, Update Your Operating System And All Software To Close Security Vulnerabilities.
Several Cybersecurity Tools Can Help Detect And Remove Trojans Like Nivdort.
Popular Malware Removal Tools Include:
Malwarebytes
Bitdefender
Kaspersky Security
Windows Defender
Norton Antivirus
These Tools Use Advanced Threat Detection Methods To Identify Hidden Malware.
Prevention Is Always Better Than Removal When It Comes To Malware Threats.
Never Open Attachments From Unknown Senders Or Click On Suspicious Email Links.
Only Download Software From Official Websites Or Trusted App Stores.
Regular Software Updates Help Fix Security Vulnerabilities That Malware Can Exploit.
A Reliable Antivirus Program Provides Real-time Protection Against Malware Threats.
Firewalls Help Block Unauthorized Connections Between Your Computer And External Networks.
Strong And Unique Passwords Can Reduce The Risk Of Unauthorized Access If Credentials Are Stolen.
Despite Advances In Cybersecurity Technology, Trojans Remain One Of The Most Common Types Of Malware. This Is Largely Because They Exploit human Behavior Rather Than Technical Vulnerabilities.
Cybercriminals Rely On Users Clicking Suspicious Links Or Downloading Infected Files. As Long As Social Engineering Remains Effective, Trojans Like Nivdort Will Continue To Pose A Significant Threat.
Organizations And Individuals Must Therefore Remain Vigilant And Practice Safe Browsing Habits.
Cybersecurity Experts Predict That Future Trojan Variants Will Become Even More Sophisticated. Some Expected Developments Include:
Use Of Artificial Intelligence To Evade Detection
Advanced Encryption Techniques
Targeted Attacks Against Specific Organizations
Increased Use Of Fileless Malware
As Cyber Threats Evolve, Security Solutions Must Also Adapt To Protect Users And Businesses.
The Nivdort Trojan Virus Is A Dangerous Form Of Malware Capable Of Stealing Sensitive Information And Giving Attackers Full Control Over Infected Systems. Its Ability To Disguise Itself As Legitimate Software Makes It Particularly Difficult To Detect.
However, By Understanding How The Trojan Works And Following Cybersecurity Best Practices, Users Can Significantly Reduce The Risk Of Infection.
Regular System Updates, Reliable Antivirus Protection, And Cautious Online Behavior Are Essential Defenses Against Threats Like The Nivdort Trojan.
Staying Informed About Emerging Cyber Threats Is One Of The Best Ways To Protect Your Digital Life In Today’s Increasingly Connected World.
Step 1: Boot Into Safe Mode
Restart Your PC And Press F8 (or Shift + F8 For Some Systems) Before Windows Loads.
Choose Safe Mode With Networking.
Safe Mode Prevents Most Malware From Loading.
Press Win + R, Type appwiz.cpl, And Press Enter.
Sort By Install Date And Uninstall Unknown Or Recently Added Programs.
Use A Trusted Anti-malware Tool:
Malwarebytes – https://www.malwarebytes.com
Screenshot Of Malwarebytes - Visit Links
Microsoft Defender – Built Into Windows 10/11
HitmanPro, ESET Online Scanner, Or Kaspersky Virus Removal Tool
ZoneAlarm Pro Antivirus + Firewall NextGen
VIPRE Antivirus - US And Others Countries, | India
Run A Full Scan And Delete/quarantine Detected Threats.
Win + R, Type temp → Delete All Files.Press Win + R, Type %temp% → Delete All Files.
Use Disk Cleanup: cleanmgr In The Run Dialog.
Go To: C:\Windows\System32\drivers\etc
Open hosts File With Notepad.
Replace With Default Content:
Press Ctrl + Shift + Esc → Open Task Manager
Go To Startup Tab
Disable Any Suspicious Entries.
Open Command Prompt As Administrator.
Run These Commands:
netsh Winsock Reset
netsh Int Ip Reset
ipconfig /flushdns
Unwanted Homepage Or Search Engine
Pop-ups Or Redirects
Unknown Extensions Installed
For Chrome:
Go To: chrome://extensions/
Remove Anything Unfamiliar
For Firefox:
Go To: about:addons → Extensions
Remove Suspicious Add-ons
For Edge:
Go To: edge://extensions/
Uninstall Unknown Add-ons
Chrome:
Go To chrome://settings/reset → "Restore Settings To Their Original Defaults"
Firefox:
Go To about:support → "Refresh Firefox"
Edge:
Go To edge://settings/resetProfileSettings → "Reset Settings"
All Browsers:
Use Ctrl + Shift + Del → Select All Time
Clear Cookies, Cached Files, And Site Data
Make Sure They Are Not Hijacked.
Chrome: chrome://settings/search
Firefox: about:preferences#search
Edge: edge://settings/search
Chrome: chrome://settings/cleanup
Use Malwarebytes Browser Guard For Real-time Browser Protection.
Always Download Software From Trusted Sources.
Keep Windows, Browsers, And Antivirus Updated.
Avoid Clicking Suspicious Links Or Ads.
Use ad Blockers And reputable Antivirus Software.
Backup Your Files Regularly.
To Remove Malware From Your Windows PC, Start By Booting Into Safe Mode, Uninstalling Suspicious Programs, And Scanning With Trusted Anti-malware Tools Like Malwarebytes. Clear Temporary Files, Reset Your Network Settings, And Check Startup Apps For Anything Unusual.
For web Browsers, Remove Unwanted Extensions, Reset Browser Settings, Clear Cache And Cookies, And Ensure Your Homepage And Search Engine Haven’t Been Hijacked. Use Cleanup Tools Like Chrome Cleanup Or Browser Guard For Added Protection.
?? Prevention Tips: Keep Software Updated, Avoid Suspicious Downloads, And Use Antivirus Protection Plus Browser Ad Blockers. Regular Backups Are Essential.
Why It Matters: Not All VPNs Offer Malware Protection.
What To Look For: Providers With built-in Malware/ad/tracker Blockers (e.g., NordVPN’s Threat Protection, ProtonVPN’s NetShield).
Purpose: Prevents Data Leaks If Your VPN Connection Drops.
Benefit: Ensures Your Real IP And Browsing Activity Aren’t Exposed To Malware-distributing Websites.
Why It Matters: DNS Leaks Can Expose Your Online Activity To Attackers.
Solution: Enable DNS Leak Protection In Your VPN Settings Or Use A Secure DNS Like Cloudflare (1.1.1.1).
Risk: Free VPNs Often Contain Malware, Sell User Data, Or Lack Security Features.
Better Option: Use Reputable Paid VPNs That Offer security Audits And Transparent Privacy Policies.
Some VPNs Block Known Phishing And Malicious Sites.
Example: Surfshark’s CleanWeb, CyberGhost’s Content Blocker.
Reason: Security Patches Fix Known Vulnerabilities.
Tip: Enable Auto-updates Or Check For Updates Weekly.
Scope: Malware Can Enter Through Phones, Tablets, Or IoT Devices.
Solution: Install VPN Apps On Every Internet-connected Device.
Fact: VPNs Do Not Remove Or Detect Malware On Your System.
Complement It With:
Antivirus Software
Firewall
Browser Extensions For Script Blocking
VPN Encrypts Traffic But Can’t Stop Malware From Executing If You Download Infected Files.
Split Tunneling Allows Certain Apps/sites To Bypass VPN.
Tip: Never Exclude Browsers, Email Clients, Or Download Managers From VPN Tunneling.
A VPN (Virtual Private Network) Enhances Your Online Privacy By Encrypting Your Internet Traffic And Masking Your IP Address. It Protects Your Data On Public Wi-Fi, Hides Browsing Activity From Hackers And ISPs, And Helps Bypass Geo-restrictions. VPNs Also Add A Layer Of Defense Against Malware By Blocking Malicious Websites And Trackers When Using Advanced Features. However, A VPN Does Not Remove Existing Malware Or Act As Antivirus Software. For Full Protection, Combine VPN Use With Antivirus Tools, Regular Software Updates, And Cautious Browsing Habits. Always Choose A Reputable VPN Provider With Strong Security And Privacy Policies.
Nivdort Trojan Virus, Nivdort Trojan, Nivdort Malware, Nivdort Trojan Virus Removal, What Is Nivdort Trojan, How To Remove Nivdort Trojan