 Blog's Page
Blog's Page
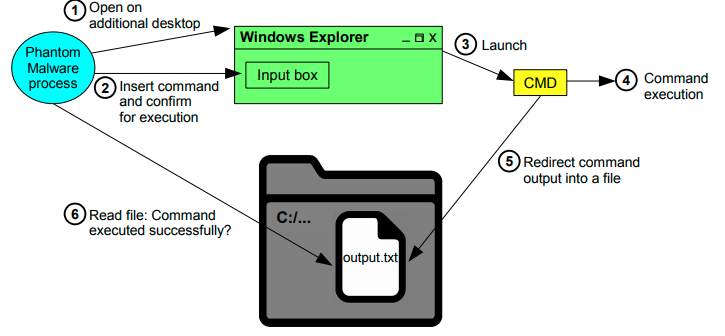
PhantomLayer Is A Newly Discovered, Highly Evasive Multi-layered Malware Strain That Uses Advanced Obfuscation And Virtualization Techniques To Bypass Modern Security Defenses. It Is Primarily Used In targeted Cyber-espionage And Data Exfiltration Campaigns, Often Against Enterprises, Government Bodies, And Financial Institutions.
Unlike Traditional Malware, PhantomLayer Deploys Itself In Multiple Concealed Layers—making Detection And Removal Extremely Challenging. It Is Often Delivered Via Phishing Emails, Weaponized PDFs, Or Drive-by Downloads From Compromised Websites.
Multi-Layer Payload Encryption:
Uses AES And XOR Encryption In Multiple Payload Stages To Hide Its Malicious Code.
Virtualized Execution Environment:
Operates Inside A Custom-built Virtual Machine, Making It Extremely Difficult For Static And Dynamic Analysis Tools To Trace Real Instructions.
Modular Architecture:
Can Download And Execute Additional Modules Based On The Victim's Environment And Data Access Levels.
Persistence Techniques:
Installs Deep Into The Windows Registry, Scheduled Tasks, And Uses DLL Sideloading To Survive System Reboots.
Anti-Debugging & Anti-VM Capabilities:
Shuts Down Or Goes Dormant If It Detects Sandboxes, Debuggers, Or Virtual Environments.
Initial Access:
Delivered Through Spear-phishing Emails With Malicious Attachments Or Links.
Decryption Phase:
The First-stage Loader Decrypts And Loads The Core Malware From Memory (fileless Operation).
Virtual Machine Launch:
The Malware Runs Its Payload Within A Custom VM, Which Emulates Its Own CPU Instructions, Evading Antivirus Tools.
Command & Control (C2) Communication:
Connects To Encrypted C2 Servers, Often Using TLS Over Non-standard Ports To Download Further Instructions Or Exfiltrate Data.
PhantomLayer Has Been Detected Targeting:
Government Defense Agencies
Financial Services And Fintech Platforms
Critical Infrastructure Systems
High-value Corporations In Europe And Asia
Once Active, PhantomLayer Can:
Steal Credentials, Cookies, And Session Tokens
Capture Screenshots And Keystrokes
Spread Laterally Across Networks
Drop Ransomware Or Wipers As A Final-stage Payload
Use EDR & XDR Solutions With Behavior-based Detection, Not Just Signature-based AVs.
Block Macro Execution From Office Documents By Default.
Enforce Strict Email Filtering And Disable External Content Loading.
Monitor For Anomalous Traffic To Unfamiliar IPs/domains.
Regularly patch OS And Third-party Software To Close Exploitation Paths.
Obfuscated PowerShell Or JavaScript In Temp Folders
Connections To Unusual Domains With Self-signed TLS Certs
Registry Entries In HKCU\Software\Microsoft\Windows\CurrentVersion\Run\
Hidden Scheduled Tasks Named With GUIDs
PhantomLayer Represents The Next Generation Of Stealth Malware—blending custom Virtual Execution, layered Encryption, And modular Payloads To Become Nearly Invisible To Traditional Tools. Organizations Must Adopt Proactive, behavioral Threat Hunting Strategies And Ensure employee Awareness To Stay Protected.
Step 1: Boot Into Safe Mode
Restart Your PC And Press F8 (or Shift + F8 For Some Systems) Before Windows Loads.
Choose Safe Mode With Networking.
Safe Mode Prevents Most Malware From Loading.
Press Win + R, Type appwiz.cpl, And Press Enter.
Sort By Install Date And Uninstall Unknown Or Recently Added Programs.
Use A Trusted Anti-malware Tool:
Malwarebytes – https://www.malwarebytes.com
Screenshot Of Malwarebytes - Visit Links
Microsoft Defender – Built Into Windows 10/11
HitmanPro, ESET Online Scanner, Or Kaspersky Virus Removal Tool
ZoneAlarm Pro Antivirus + Firewall NextGen
VIPRE Antivirus - US And Others Countries, | India
Run A Full Scan And Delete/quarantine Detected Threats.
Win + R, Type temp → Delete All Files.Press Win + R, Type %temp% → Delete All Files.
Use Disk Cleanup: cleanmgr In The Run Dialog.
Go To: C:\Windows\System32\drivers\etc
Open hosts File With Notepad.
Replace With Default Content:
Press Ctrl + Shift + Esc → Open Task Manager
Go To Startup Tab
Disable Any Suspicious Entries.
Open Command Prompt As Administrator.
Run These Commands:
netsh Winsock Reset
netsh Int Ip Reset
ipconfig /flushdns
Unwanted Homepage Or Search Engine
Pop-ups Or Redirects
Unknown Extensions Installed
For Chrome:
Go To: chrome://extensions/
Remove Anything Unfamiliar
For Firefox:
Go To: about:addons → Extensions
Remove Suspicious Add-ons
For Edge:
Go To: edge://extensions/
Uninstall Unknown Add-ons
Chrome:
Go To chrome://settings/reset → "Restore Settings To Their Original Defaults"
Firefox:
Go To about:support → "Refresh Firefox"
Edge:
Go To edge://settings/resetProfileSettings → "Reset Settings"
All Browsers:
Use Ctrl + Shift + Del → Select All Time
Clear Cookies, Cached Files, And Site Data
Make Sure They Are Not Hijacked.
Chrome: chrome://settings/search
Firefox: about:preferences#search
Edge: edge://settings/search
Chrome: chrome://settings/cleanup
Use Malwarebytes Browser Guard For Real-time Browser Protection.
Always Download Software From Trusted Sources.
Keep Windows, Browsers, And Antivirus Updated.
Avoid Clicking Suspicious Links Or Ads.
Use ad Blockers And reputable Antivirus Software.
Backup Your Files Regularly.
To Remove Malware From Your Windows PC, Start By Booting Into Safe Mode, Uninstalling Suspicious Programs, And Scanning With Trusted Anti-malware Tools Like Malwarebytes. Clear Temporary Files, Reset Your Network Settings, And Check Startup Apps For Anything Unusual.
For web Browsers, Remove Unwanted Extensions, Reset Browser Settings, Clear Cache And Cookies, And Ensure Your Homepage And Search Engine Haven’t Been Hijacked. Use Cleanup Tools Like Chrome Cleanup Or Browser Guard For Added Protection.
?? Prevention Tips: Keep Software Updated, Avoid Suspicious Downloads, And Use Antivirus Protection Plus Browser Ad Blockers. Regular Backups Are Essential.
Why It Matters: Not All VPNs Offer Malware Protection.
What To Look For: Providers With built-in Malware/ad/tracker Blockers (e.g., NordVPN’s Threat Protection, ProtonVPN’s NetShield).
Purpose: Prevents Data Leaks If Your VPN Connection Drops.
Benefit: Ensures Your Real IP And Browsing Activity Aren’t Exposed To Malware-distributing Websites.
Why It Matters: DNS Leaks Can Expose Your Online Activity To Attackers.
Solution: Enable DNS Leak Protection In Your VPN Settings Or Use A Secure DNS Like Cloudflare (1.1.1.1).
Risk: Free VPNs Often Contain Malware, Sell User Data, Or Lack Security Features.
Better Option: Use Reputable Paid VPNs That Offer security Audits And Transparent Privacy Policies.
Some VPNs Block Known Phishing And Malicious Sites.
Example: Surfshark’s CleanWeb, CyberGhost’s Content Blocker.
Reason: Security Patches Fix Known Vulnerabilities.
Tip: Enable Auto-updates Or Check For Updates Weekly.
Scope: Malware Can Enter Through Phones, Tablets, Or IoT Devices.
Solution: Install VPN Apps On Every Internet-connected Device.
Fact: VPNs Do Not Remove Or Detect Malware On Your System.
Complement It With:
Antivirus Software
Firewall
Browser Extensions For Script Blocking
VPN Encrypts Traffic But Can’t Stop Malware From Executing If You Download Infected Files.
Split Tunneling Allows Certain Apps/sites To Bypass VPN.
Tip: Never Exclude Browsers, Email Clients, Or Download Managers From VPN Tunneling.
A VPN (Virtual Private Network) Enhances Your Online Privacy By Encrypting Your Internet Traffic And Masking Your IP Address. It Protects Your Data On Public Wi-Fi, Hides Browsing Activity From Hackers And ISPs, And Helps Bypass Geo-restrictions. VPNs Also Add A Layer Of Defense Against Malware By Blocking Malicious Websites And Trackers When Using Advanced Features. However, A VPN Does Not Remove Existing Malware Or Act As Antivirus Software. For Full Protection, Combine VPN Use With Antivirus Tools, Regular Software Updates, And Cautious Browsing Habits. Always Choose A Reputable VPN Provider With Strong Security And Privacy Policies.
PhantomLayer, Remove PhantomLayer, PhantomLayer Removal, Uninstall PhantomLayer, Delete PhantomLayer, Get Rid Of PhantomLayer, PhantomLayer Removal, D