 Blog's Page
Blog's Page
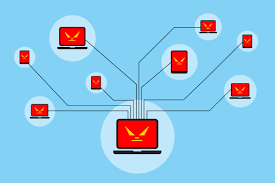
Avalanche Botnet Is A Malicious Program That Can Violate Cyber Law. Avalanche Botnet Has Been Designed By The Cybercriminal To Target The Terminal, Where Are The Security System Compromise Easily. There Are Number Of Things, Which Has Been Associated With Avalanche Botnet Potentially Unwanted Program. It Can Target The Computer System Specially Worked On Windows Platform. However, There Are Lots Of Issues Generated Inadvertently In The Computer System Via Avalanche Botnet Malware. The Phishing Attack Is A Also Used By Avalanche Botnet To Target The Users And Persuade Them To A Legitimate Website Or An Online Platform.
The Malware That Are Distributed Using This Covert Network Are Basically Information Stealing, Banking Trojans And Ransomware.
This Worldwide Network Was Capable Of Providing The Following Services:
Also, It Has Been Reported That This Fast Flux Network Was Advertised In The Underground Online Cybercriminal Forums.
This Universal Network Make Use Of DNS Techniques To Hide Cybercrimes Behind The Ever Changing Network Of Compromised Hosts Acting As Proxies. These Proxy Machines Are The Compromised Systems Or Machines That Are Already A Part Of One Or The Other Botnet. These Machines Then Can Help The Attacker In Hiding Its Identity Behind These Machines Over The Network Thereby Making It Nearly Impossible To Identify The Attacker’s Machine.
Malware Authors Use Avalanche Services To Compromise Various Machines, Which Are Then Capable Of Performing The Following Functions:
Stealing Of User Credentials And Other Sensitive Data, Such As Banking And Credit Card Information.Capable Of Encrypting User Files And Demand Ransom Amount Of Money Against The Decryption Key.Providing Cyber Criminals An Unauthorized Remote Access To The Infected Computer.Capable Of Serving Or Being A Part Of Conducting Distributed Denial-of-service (DDoS) Attacks.
The Various Malware Families That Are Using This Fast Flux Network Are Listed Below:
The Avalanche Botnet Was A Highly Sophisticated Cybercriminal Infrastructure That Operated From Around 2009 Until It Was Dismantled In 2016 Through A Large International Law Enforcement Effort. Unlike Typical Botnets That Rely On A Single Centralized Command-and-control (C2) Server, Avalanche Used A Resilient And Decentralized Architecture, Making It Much Harder To Detect And Shut Down.
Avalanche Functioned As A Platform For Multiple Types Of Malware Campaigns Rather Than A Single Malicious Program. Cybercriminals Used It To Distribute Banking Trojans, Ransomware, And Phishing Attacks On A Global Scale. Some Of The Most Notable Malware Families Associated With Avalanche Included Zeus, Citadel, And CryptoLocker. These Tools Allowed Attackers To Steal Financial Information, Capture Login Credentials, And Extort Victims By Encrypting Their Data.
A Key Feature Of Avalanche Was Its Fast-flux DNS Technique, Which Frequently Changed IP Addresses Associated With Its Domains. This Made It Extremely Difficult For Security Professionals To Block Its Infrastructure. Additionally, The Botnet Used Domain Generation Algorithms (DGAs) To Create A Large Number Of Domain Names, Further Complicating Efforts To Track And Disable It.
At Its Peak, Avalanche Controlled Hundreds Of Thousands Of Infected Computers Across More Than 180 Countries. It Was Responsible For Significant Financial Losses, Estimated In The Hundreds Of Millions Of Dollars.
The Takedown Of Avalanche In Late 2016 Was The Result Of A Coordinated Effort Involving Law Enforcement Agencies, Cybersecurity Firms, And Academic Researchers From Over 30 Countries. Authorities Seized Servers, Blocked Malicious Domains, And Arrested Key Suspects. This Operation Is Considered One Of The Most Successful Global Actions Against Cybercrime Infrastructure.
Overall, Avalanche Demonstrated How Organized And Scalable Cybercrime Had Become, Highlighting The Need For International Cooperation In Combating Digital Threats.
Step 1: Boot Into Safe Mode
Restart Your PC And Press F8 (or Shift + F8 For Some Systems) Before Windows Loads.
Choose Safe Mode With Networking.
Safe Mode Prevents Most Malware From Loading.
Press Win + R, Type appwiz.cpl, And Press Enter.
Sort By Install Date And Uninstall Unknown Or Recently Added Programs.
Use A Trusted Anti-malware Tool:
Malwarebytes – https://www.malwarebytes.com
Screenshot Of Malwarebytes - Visit Links
Microsoft Defender – Built Into Windows 10/11
HitmanPro, ESET Online Scanner, Or Kaspersky Virus Removal Tool
ZoneAlarm Pro Antivirus + Firewall NextGen
VIPRE Antivirus - US And Others Countries, | India
Run A Full Scan And Delete/quarantine Detected Threats.
Win + R, Type temp → Delete All Files.Press Win + R, Type %temp% → Delete All Files.
Use Disk Cleanup: cleanmgr In The Run Dialog.
Go To: C:\Windows\System32\drivers\etc
Open hosts File With Notepad.
Replace With Default Content:
Press Ctrl + Shift + Esc → Open Task Manager
Go To Startup Tab
Disable Any Suspicious Entries.
Open Command Prompt As Administrator.
Run These Commands:
netsh Winsock Reset
netsh Int Ip Reset
ipconfig /flushdns
Unwanted Homepage Or Search Engine
Pop-ups Or Redirects
Unknown Extensions Installed
For Chrome:
Go To: chrome://extensions/
Remove Anything Unfamiliar
For Firefox:
Go To: about:addons → Extensions
Remove Suspicious Add-ons
For Edge:
Go To: edge://extensions/
Uninstall Unknown Add-ons
Chrome:
Go To chrome://settings/reset → "Restore Settings To Their Original Defaults"
Firefox:
Go To about:support → "Refresh Firefox"
Edge:
Go To edge://settings/resetProfileSettings → "Reset Settings"
All Browsers:
Use Ctrl + Shift + Del → Select All Time
Clear Cookies, Cached Files, And Site Data
Make Sure They Are Not Hijacked.
Chrome: chrome://settings/search
Firefox: about:preferences#search
Edge: edge://settings/search
Chrome: chrome://settings/cleanup
Use Malwarebytes Browser Guard For Real-time Browser Protection.
Always Download Software From Trusted Sources.
Keep Windows, Browsers, And Antivirus Updated.
Avoid Clicking Suspicious Links Or Ads.
Use ad Blockers And reputable Antivirus Software.
Backup Your Files Regularly.
To Remove Malware From Your Windows PC, Start By Booting Into Safe Mode, Uninstalling Suspicious Programs, And Scanning With Trusted Anti-malware Tools Like Malwarebytes. Clear Temporary Files, Reset Your Network Settings, And Check Startup Apps For Anything Unusual.
For web Browsers, Remove Unwanted Extensions, Reset Browser Settings, Clear Cache And Cookies, And Ensure Your Homepage And Search Engine Haven’t Been Hijacked. Use Cleanup Tools Like Chrome Cleanup Or Browser Guard For Added Protection.
?? Prevention Tips: Keep Software Updated, Avoid Suspicious Downloads, And Use Antivirus Protection Plus Browser Ad Blockers. Regular Backups Are Essential.
Why It Matters: Not All VPNs Offer Malware Protection.
What To Look For: Providers With built-in Malware/ad/tracker Blockers (e.g., NordVPN’s Threat Protection, ProtonVPN’s NetShield).
Purpose: Prevents Data Leaks If Your VPN Connection Drops.
Benefit: Ensures Your Real IP And Browsing Activity Aren’t Exposed To Malware-distributing Websites.
Why It Matters: DNS Leaks Can Expose Your Online Activity To Attackers.
Solution: Enable DNS Leak Protection In Your VPN Settings Or Use A Secure DNS Like Cloudflare (1.1.1.1).
Risk: Free VPNs Often Contain Malware, Sell User Data, Or Lack Security Features.
Better Option: Use Reputable Paid VPNs That Offer security Audits And Transparent Privacy Policies.
Some VPNs Block Known Phishing And Malicious Sites.
Example: Surfshark’s CleanWeb, CyberGhost’s Content Blocker.
Reason: Security Patches Fix Known Vulnerabilities.
Tip: Enable Auto-updates Or Check For Updates Weekly.
Scope: Malware Can Enter Through Phones, Tablets, Or IoT Devices.
Solution: Install VPN Apps On Every Internet-connected Device.
Fact: VPNs Do Not Remove Or Detect Malware On Your System.
Complement It With:
Antivirus Software
Firewall
Browser Extensions For Script Blocking
VPN Encrypts Traffic But Can’t Stop Malware From Executing If You Download Infected Files.
Split Tunneling Allows Certain Apps/sites To Bypass VPN.
Tip: Never Exclude Browsers, Email Clients, Or Download Managers From VPN Tunneling.
A VPN (Virtual Private Network) Enhances Your Online Privacy By Encrypting Your Internet Traffic And Masking Your IP Address. It Protects Your Data On Public Wi-Fi, Hides Browsing Activity From Hackers And ISPs, And Helps Bypass Geo-restrictions. VPNs Also Add A Layer Of Defense Against Malware By Blocking Malicious Websites And Trackers When Using Advanced Features. However, A VPN Does Not Remove Existing Malware Or Act As Antivirus Software. For Full Protection, Combine VPN Use With Antivirus Tools, Regular Software Updates, And Cautious Browsing Habits. Always Choose A Reputable VPN Provider With Strong Security And Privacy Policies.
Avalanche Botnet, Remove Avalanche Botnet, Uninstall Avalanche Botnet, Get Rid Of Avalanche Botnet, Avalanche Botnet Removal