 Blog's Page
Blog's Page
The Internet Has Become An Essential Part Of Daily Life, But Along With Its Benefits Comes An Increasing Number Of Cybersecurity Threats. One Such Threat That Gained Global Attention Is The Fireball Browser Hijacker And Adware. Originally Discovered By Cybersecurity Researchers, Fireball Infected Millions Of Computers Worldwide, Raising Concerns About Browser Security, Online Privacy, And Malware Distribution.
In This Article, We Will Explore What Fireball Browser Hijacker Is, How It Works, How It Spreads, The Risks It Poses, And The Best Ways To Remove And Prevent It.
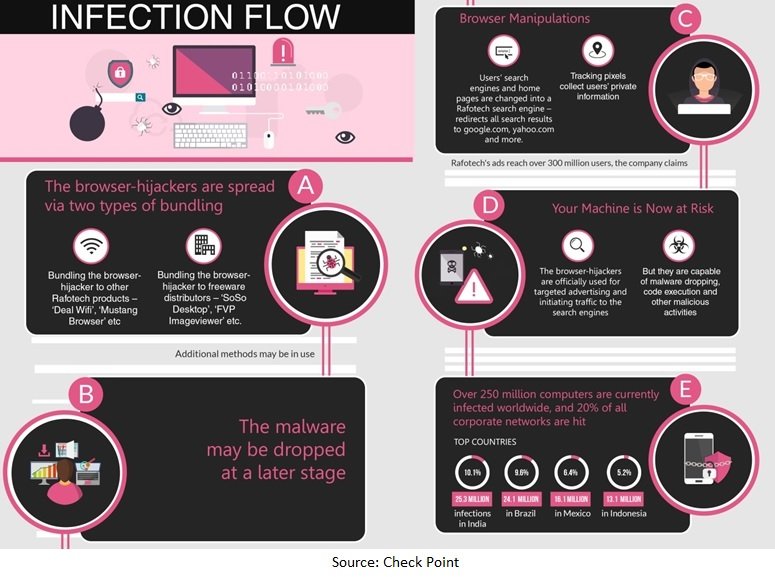
Fireball Is A Type Of Browser Hijacker And Adware Designed To Manipulate Web Browsers, Modify Browser Settings, And Redirect Users To Unwanted Search Engines Or Advertising Websites. It Was Initially Linked To A Digital Marketing Company That Used The Software To Generate Web Traffic And Advertising Revenue.
Unlike Traditional Viruses That Focus On Destroying Files Or Stealing Data Directly, Fireball Primarily Targets Browsers Such As Google Chrome, Mozilla Firefox, Microsoft Edge, And Internet Explorer. Once Installed, It Can Change The Browser Homepage, Alter The Default Search Engine, Inject Advertisements, And Track User Browsing Activities.
Cybersecurity Experts Classify Fireball As Potentially Unwanted Software (PUP) Because Users Often Install It Unknowingly Through Bundled Software Downloads Or Deceptive Installation Methods.
Aliases:
It Is Reported That The Malware “Fireball” Is Used By One Of The Largest Marketing Agency To Manipulate The Victims’ Browsers And Changes Their Default Search Engines And Home-pages Into Fake Search Engines. It Also Redirects The Queries To Either Yahoo.com Or Google.com. The Fake Search Engines Also Collects The Users’ Private Information.
Indicators Of Compromise (IoC)
Command & Control Addresses:
File Hashes:
Fireball Operates By Taking Control Of A User’s Browser Settings. After Installation, It May:
Replace The Default Homepage
Change The Browser Search Engine
Redirect Search Queries To Sponsored Websites
Display Intrusive Advertisements And Pop-ups
Install Browser Extensions Without Permission
Collect Browsing Data And User Behavior
Download Additional Malicious Software
The Primary Goal Of Fireball Is To Generate Advertising Revenue Through Redirected Traffic And Ad Impressions. However, Its Ability To Execute Code Remotely Also Makes It A Significant Security Concern.
One Of The Reasons Fireball Became Widespread Is Its Aggressive Distribution Methods. The Malware Commonly Spreads Through:
Free Software Downloads Often Include Additional Programs Hidden Within The Installation Process. Users Who Click “Next” Repeatedly Without Reviewing Installation Settings May Accidentally Install Fireball Alongside Legitimate Software.
Cybercriminals May Disguise Fireball As A Browser Update, Media Player Update, Or Security Patch. Unsuspecting Users Install The Fake Update, Unknowingly Infecting Their Systems.
Clicking Suspicious Ads Or Pop-ups Can Trigger Automatic Downloads Of Adware Or Browser Hijackers.
Downloading Cracked Software, Pirated Applications, Or Files From Unofficial Websites Increases The Risk Of Malware Infections, Including Fireball.
Users Infected With Fireball May Notice Several Unusual Behaviors In Their Browsers And Systems. Common Signs Include:
Homepage Changes Without Permission
Unknown Search Engines Appearing In The Browser
Excessive Pop-up Ads
Slow Browser Performance
Frequent Redirects To Unfamiliar Websites
New Browser Extensions You Did Not Install
Increased CPU Or Memory Usage
These Symptoms May Indicate The Presence Of Fireball Or Another Browser Hijacker.
Although Some People View Adware As Less Harmful Than Ransomware Or Trojans, Fireball Still Presents Serious Security And Privacy Risks.
Fireball Can Monitor Browsing Habits, Collect Search Queries, Track Visited Websites, And Gather Other Browsing-related Data. This Information May Be Used For Targeted Advertising Or Shared With Third Parties.
The Software’s Ability To Download And Execute Additional Files Means Infected Systems May Later Become Targets For More Dangerous Malware, Including Spyware, Ransomware, Or Banking Trojans.
Fireball Modifies Browser Settings Without Clear User Consent, Reducing User Control And Potentially Exposing Users To Unsafe Websites.
Adware Consumes System Resources, Causing Slower Browsing, Lagging Performance, And Frequent Crashes.
Removing Fireball Requires A Combination Of Manual Cleanup And Antivirus Scanning. Follow These Steps Carefully.
On Windows:
Open The Control Panel
Go To “Programs And Features”
Look For Suspicious Or Unknown Programs
Uninstall Any Unwanted Software
On Mac:
Open Applications
Move Suspicious Apps To Trash
Empty The Trash
Check All Installed Browser Extensions And Remove Anything Unfamiliar.
For Google Chrome:
Open Chrome Settings
Navigate To Extensions
Remove Suspicious Extensions
For Mozilla Firefox:
Open Add-ons And Themes
Disable Or Remove Unknown Add-ons
Resetting Your Browser Helps Restore Default Settings.
In Chrome:
Open Settings
Select “Reset And Clean Up”
Click “Restore Settings To Their Original Defaults”
Use Trusted Antivirus Or Anti-malware Software To Detect And Remove Remaining Threats. Security Tools Can Identify Hidden Files, Registry Changes, And Malicious Processes Associated With Fireball.
Install The Latest Operating System And Browser Updates To Patch Vulnerabilities And Improve Security.
Prevention Is Always Better Than Removal. Following Cybersecurity Best Practices Can Reduce The Risk Of Future Infections.
Only Download Applications From Official Websites Or Trusted App Stores.
Choose “Custom” Or “Advanced” Installation Options To Review Bundled Software Before Installation.
Do Not Click Pop-ups, Fake Alerts, Or Advertisements From Unknown Websites.
Install Reliable Antivirus Software And Ensure It Stays Updated.
Browser Updates Often Include Security Improvements That Help Protect Against Hijackers And Exploits.
Modern Browsers Include Built-in Protections Against Malicious Websites And Downloads. Keep These Features Enabled.
The Fireball Browser Hijacker Highlighted How Easily Adware Can Spread Across Millions Of Devices Through Deceptive Marketing Tactics And Bundled Installations. It Also Demonstrated The Importance Of Cybersecurity Awareness Among Internet Users.
Many Users Unknowingly Compromise Their Systems Simply By Rushing Through Software Installations Or Downloading Files From Unverified Sources. Educating Users About Online Threats Is One Of The Most Effective Ways To Reduce Malware Infections.
Organizations Should Also Train Employees On Safe Browsing Practices Because Browser Hijackers Can Compromise Workplace Systems, Expose Sensitive Information, And Create Security Vulnerabilities.
Fireball Browser Hijacker And Adware May Not Be As Destructive As Some Forms Of Malware, But It Remains A Serious Cybersecurity Threat. By Hijacking Browsers, Redirecting Traffic, Displaying Intrusive Advertisements, And Collecting User Data, Fireball Compromises Privacy And System Performance.
Fortunately, Users Can Protect Themselves Through Safe Browsing Habits, Careful Software Installation, Regular Updates, And Reliable Antivirus Protection. If You Suspect Your Device Is Infected, Prompt Removal And System Scanning Are Essential To Restore Browser Security And Prevent Further Issues.
Staying Informed About Threats Like Fireball Is A Critical Step Toward Maintaining Online Safety In Today’s Increasingly Connected Digital World.
Step 1: Boot Into Safe Mode
Restart Your PC And Press F8 (or Shift + F8 For Some Systems) Before Windows Loads.
Choose Safe Mode With Networking.
Safe Mode Prevents Most Malware From Loading.
Press Win + R, Type appwiz.cpl, And Press Enter.
Sort By Install Date And Uninstall Unknown Or Recently Added Programs.
Use A Trusted Anti-malware Tool:
Malwarebytes – https://www.malwarebytes.com
Screenshot Of Malwarebytes - Visit Links
Microsoft Defender – Built Into Windows 10/11
HitmanPro, ESET Online Scanner, Or Kaspersky Virus Removal Tool
ZoneAlarm Pro Antivirus + Firewall NextGen
VIPRE Antivirus - US And Others Countries, | India
Run A Full Scan And Delete/quarantine Detected Threats.
Win + R, Type temp → Delete All Files.Press Win + R, Type %temp% → Delete All Files.
Use Disk Cleanup: cleanmgr In The Run Dialog.
Go To: C:\Windows\System32\drivers\etc
Open hosts File With Notepad.
Replace With Default Content:
Press Ctrl + Shift + Esc → Open Task Manager
Go To Startup Tab
Disable Any Suspicious Entries.
Open Command Prompt As Administrator.
Run These Commands:
netsh Winsock Reset
netsh Int Ip Reset
ipconfig /flushdns
Unwanted Homepage Or Search Engine
Pop-ups Or Redirects
Unknown Extensions Installed
For Chrome:
Go To: chrome://extensions/
Remove Anything Unfamiliar
For Firefox:
Go To: about:addons → Extensions
Remove Suspicious Add-ons
For Edge:
Go To: edge://extensions/
Uninstall Unknown Add-ons
Chrome:
Go To chrome://settings/reset → "Restore Settings To Their Original Defaults"
Firefox:
Go To about:support → "Refresh Firefox"
Edge:
Go To edge://settings/resetProfileSettings → "Reset Settings"
All Browsers:
Use Ctrl + Shift + Del → Select All Time
Clear Cookies, Cached Files, And Site Data
Make Sure They Are Not Hijacked.
Chrome: chrome://settings/search
Firefox: about:preferences#search
Edge: edge://settings/search
Chrome: chrome://settings/cleanup
Use Malwarebytes Browser Guard For Real-time Browser Protection.
Always Download Software From Trusted Sources.
Keep Windows, Browsers, And Antivirus Updated.
Avoid Clicking Suspicious Links Or Ads.
Use ad Blockers And reputable Antivirus Software.
Backup Your Files Regularly.
To Remove Malware From Your Windows PC, Start By Booting Into Safe Mode, Uninstalling Suspicious Programs, And Scanning With Trusted Anti-malware Tools Like Malwarebytes. Clear Temporary Files, Reset Your Network Settings, And Check Startup Apps For Anything Unusual.
For web Browsers, Remove Unwanted Extensions, Reset Browser Settings, Clear Cache And Cookies, And Ensure Your Homepage And Search Engine Haven’t Been Hijacked. Use Cleanup Tools Like Chrome Cleanup Or Browser Guard For Added Protection.
?? Prevention Tips: Keep Software Updated, Avoid Suspicious Downloads, And Use Antivirus Protection Plus Browser Ad Blockers. Regular Backups Are Essential.
Why It Matters: Not All VPNs Offer Malware Protection.
What To Look For: Providers With built-in Malware/ad/tracker Blockers (e.g., NordVPN’s Threat Protection, ProtonVPN’s NetShield).
Purpose: Prevents Data Leaks If Your VPN Connection Drops.
Benefit: Ensures Your Real IP And Browsing Activity Aren’t Exposed To Malware-distributing Websites.
Why It Matters: DNS Leaks Can Expose Your Online Activity To Attackers.
Solution: Enable DNS Leak Protection In Your VPN Settings Or Use A Secure DNS Like Cloudflare (1.1.1.1).
Risk: Free VPNs Often Contain Malware, Sell User Data, Or Lack Security Features.
Better Option: Use Reputable Paid VPNs That Offer security Audits And Transparent Privacy Policies.
Some VPNs Block Known Phishing And Malicious Sites.
Example: Surfshark’s CleanWeb, CyberGhost’s Content Blocker.
Reason: Security Patches Fix Known Vulnerabilities.
Tip: Enable Auto-updates Or Check For Updates Weekly.
Scope: Malware Can Enter Through Phones, Tablets, Or IoT Devices.
Solution: Install VPN Apps On Every Internet-connected Device.
Fact: VPNs Do Not Remove Or Detect Malware On Your System.
Complement It With:
Antivirus Software
Firewall
Browser Extensions For Script Blocking
VPN Encrypts Traffic But Can’t Stop Malware From Executing If You Download Infected Files.
Split Tunneling Allows Certain Apps/sites To Bypass VPN.
Tip: Never Exclude Browsers, Email Clients, Or Download Managers From VPN Tunneling.
A VPN (Virtual Private Network) Enhances Your Online Privacy By Encrypting Your Internet Traffic And Masking Your IP Address. It Protects Your Data On Public Wi-Fi, Hides Browsing Activity From Hackers And ISPs, And Helps Bypass Geo-restrictions. VPNs Also Add A Layer Of Defense Against Malware By Blocking Malicious Websites And Trackers When Using Advanced Features. However, A VPN Does Not Remove Existing Malware Or Act As Antivirus Software. For Full Protection, Combine VPN Use With Antivirus Tools, Regular Software Updates, And Cautious Browsing Habits. Always Choose A Reputable VPN Provider With Strong Security And Privacy Policies.
Fireball Browser Hijacker/Adware: What It Is, How It Spreads, And How To Remove It