 Blog's Page
Blog's Page
Android Smartphones Have Become An Essential Part Of Daily Life. From Banking And Shopping To Social Networking And Business Communication, People Rely Heavily On Mobile Devices. However, With The Growing Popularity Of Android Devices, Cybercriminals Are Continuously Developing Advanced Malware To Exploit Vulnerabilities. One Such Dangerous Malware Is Dvmap Android Malware.
Dvmap Is Considered One Of The Most Sophisticated Android Malware Families Discovered In Recent Years. It Is Known For Its Ability To Infiltrate Android Systems, Gain Root Access, And Hide Malicious Activities From Users And Security Applications. In This Blog, We Will Explore What Dvmap Android Malware Is, How It Works, Its Impact, Symptoms, And Ways To Protect Your Device From Infection.
Dvmap Is A Type Of Android Malware Designed To Compromise Android Devices By Modifying System Files And Bypassing Security Protections. Security Researchers Identified Dvmap As A Highly Dangerous Malware Because It Can Inject Malicious Code Into Core Android System Libraries.
Unlike Ordinary Malware That Simply Displays Ads Or Steals Data, Dvmap Attempts To Gain Root Privileges On The Infected Device. Root Access Allows The Malware To Control Almost Every Aspect Of The Android Operating System. Once Installed, It Can Silently Perform Harmful Actions Without The User's Knowledge.
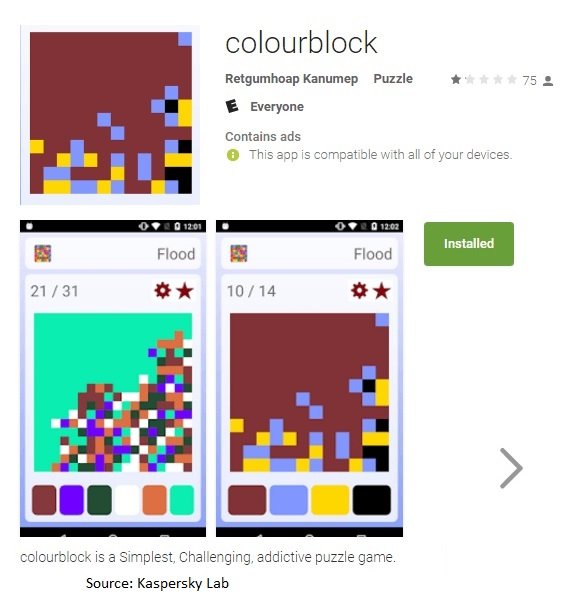
The Malware Was Mainly Distributed Through Fake Applications Uploaded To Unofficial Android App Stores And Sometimes Even Managed To Bypass Security Checks In Legitimate App Marketplaces.
Dvmap Uses Advanced Techniques To Infect Android Devices And Maintain Persistence. Here’s How The Malware Typically Operates:
Dvmap Often Hides Inside Apps That Appear Harmless. These Apps May Include Games, Utility Tools, Or Photo-editing Software. Users Unknowingly Download And Install The Infected Application.
After Installation, The Malware Attempts To Exploit Vulnerabilities In The Android Operating System To Gain Root Access. Root Access Gives Dvmap Complete Administrative Control Over The Device.
One Of The Most Dangerous Features Of Dvmap Is Its Ability To Inject Malicious Code Into System Libraries. This Process Allows It To Hide From Antivirus Software And Security Scans.
Once The Device Is Compromised, Dvmap Can Download Additional Malicious Payloads. These May Include Spyware, Ransomware, Adware, Or Banking Trojans.
Even After Restarting The Device, Dvmap Can Continue Running Because It Modifies Core System Components. Removing It Can Be Extremely Difficult Without Resetting The Device.
Dvmap Stands Out Among Android Malware Families Because Of Its Advanced Capabilities. Some Of Its Key Features Include:
Root Access Exploitation
System File Modification
Stealthy Malware Injection
Ability To Bypass Antivirus Detection
Downloading Secondary Malicious Payloads
Persistent Access To Infected Devices
These Features Make Dvmap One Of The Most Dangerous Threats In The Android Ecosystem.
Detecting Dvmap Malware Can Be Difficult Because It Hides Deep Within The Operating System. However, Users May Notice Certain Warning Signs:
Slow Device Performance
Frequent App Crashes
Device Overheating
Battery Draining Rapidly
Users May Start Seeing Unwanted Advertisements Or Redirects Even When No Browser Is Open.
Malware Often Communicates With Remote Servers. Sudden Spikes In Internet Data Usage May Indicate Malicious Background Activity.
Dvmap Can Install Additional Applications Without User Permission.
Some Infected Devices May Show Disabled Antivirus Or Security Applications.
If You Notice Multiple Symptoms Together, Your Android Device May Be Infected.
Dvmap Is Considered Highly Dangerous Because It Targets The Core Of The Android Operating System. Unlike Regular Malware That Can Be Removed By Uninstalling An App, Dvmap Modifies System Libraries And Gains Deep-level Access.
Here Are Some Major Risks Associated With Dvmap Malware:
Cybercriminals Can Steal Personal Information, Login Credentials, Banking Details, And Sensitive Files.
Banking Trojans Downloaded By Dvmap Can Intercept Financial Transactions And Steal Money.
The Malware May Access Microphones, Cameras, Messages, And Call Logs.
Hackers Can Remotely Control Infected Devices For Malicious Activities.
Infected Devices May Become Part Of A Botnet Used For Spam Campaigns Or Cyberattacks.
Dvmap Malware Primarily Spreads Through Malicious Android Applications. Common Infection Sources Include:
Third-party App Stores
Pirated APK Downloads
Fake Utility Applications
Modified Gaming Apps
Malicious Advertisements
Cybercriminals Often Use Social Engineering Tactics To Trick Users Into Installing Infected Apps.
Preventing Malware Infection Is Always Better Than Dealing With The Consequences. Here Are Essential Cybersecurity Practices To Stay Protected:
Only Install Apps From Trusted Platforms Like The Official Google Play Store.
Never Download APK Files From Suspicious Websites Or Unofficial App Stores.
Install The Latest Android Security Patches And Updates To Fix Vulnerabilities.
Reliable Antivirus And Mobile Security Applications Can Help Detect Malware Threats Early.
Review App Permissions Carefully Before Installation. Avoid Apps Requesting Unnecessary Access.
Google Play Protect Scans Apps For Malicious Behavior And Adds An Extra Layer Of Security.
Rooted Devices Are More Vulnerable To Malware Attacks Because Security Restrictions Are Weakened.
Removing Dvmap Can Be Extremely Challenging Because It Embeds Itself Into System Files. However, The Following Steps May Help:
Safe Mode Disables Third-party Applications Temporarily.
Remove Recently Installed Or Unknown Applications.
Use Reputable Android Antivirus Software To Detect And Remove Threats.
If The Malware Persists, Performing A Factory Reset May Be Necessary.
In Severe Cases, Reinstalling The Official Android Firmware May Be The Only Solution.
Always Back Up Important Files Before Performing A Reset.
The Rise Of Malware Like Dvmap Highlights The Growing Importance Of Mobile Cybersecurity. Smartphones Now Contain Highly Sensitive Personal And Financial Information, Making Them Attractive Targets For Cybercriminals.
Users Should Remain Cautious While Installing Apps, Clicking Links, Or Downloading Files. Businesses Should Also Educate Employees About Mobile Security Risks And Implement Endpoint Protection Solutions.
Cybersecurity Awareness Plays A Critical Role In Preventing Malware Infections And Protecting Digital Privacy.
Dvmap Android Malware Is A Sophisticated Cyber Threat Capable Of Compromising Android Devices At The System Level. Its Ability To Gain Root Access, Inject Malicious Code, And Evade Detection Makes It Particularly Dangerous.
As Android Malware Continues To Evolve, Users Must Adopt Strong Cybersecurity Practices To Stay Safe. Downloading Apps Only From Trusted Sources, Keeping Devices Updated, And Using Reliable Mobile Security Tools Can Significantly Reduce The Risk Of Infection.
Staying Informed About Threats Like Dvmap Is The First Step Toward Protecting Your Android Device And Personal Data From Cybercriminals.
Step 1: Boot Into Safe Mode
Restart Your PC And Press F8 (or Shift + F8 For Some Systems) Before Windows Loads.
Choose Safe Mode With Networking.
Safe Mode Prevents Most Malware From Loading.
Press Win + R, Type appwiz.cpl, And Press Enter.
Sort By Install Date And Uninstall Unknown Or Recently Added Programs.
Use A Trusted Anti-malware Tool:
Malwarebytes – https://www.malwarebytes.com
Screenshot Of Malwarebytes - Visit Links
Microsoft Defender – Built Into Windows 10/11
HitmanPro, ESET Online Scanner, Or Kaspersky Virus Removal Tool
ZoneAlarm Pro Antivirus + Firewall NextGen
VIPRE Antivirus - US And Others Countries, | India
Run A Full Scan And Delete/quarantine Detected Threats.
Win + R, Type temp → Delete All Files.Press Win + R, Type %temp% → Delete All Files.
Use Disk Cleanup: cleanmgr In The Run Dialog.
Go To: C:\Windows\System32\drivers\etc
Open hosts File With Notepad.
Replace With Default Content:
Press Ctrl + Shift + Esc → Open Task Manager
Go To Startup Tab
Disable Any Suspicious Entries.
Open Command Prompt As Administrator.
Run These Commands:
netsh Winsock Reset
netsh Int Ip Reset
ipconfig /flushdns
Unwanted Homepage Or Search Engine
Pop-ups Or Redirects
Unknown Extensions Installed
For Chrome:
Go To: chrome://extensions/
Remove Anything Unfamiliar
For Firefox:
Go To: about:addons → Extensions
Remove Suspicious Add-ons
For Edge:
Go To: edge://extensions/
Uninstall Unknown Add-ons
Chrome:
Go To chrome://settings/reset → "Restore Settings To Their Original Defaults"
Firefox:
Go To about:support → "Refresh Firefox"
Edge:
Go To edge://settings/resetProfileSettings → "Reset Settings"
All Browsers:
Use Ctrl + Shift + Del → Select All Time
Clear Cookies, Cached Files, And Site Data
Make Sure They Are Not Hijacked.
Chrome: chrome://settings/search
Firefox: about:preferences#search
Edge: edge://settings/search
Chrome: chrome://settings/cleanup
Use Malwarebytes Browser Guard For Real-time Browser Protection.
Always Download Software From Trusted Sources.
Keep Windows, Browsers, And Antivirus Updated.
Avoid Clicking Suspicious Links Or Ads.
Use ad Blockers And reputable Antivirus Software.
Backup Your Files Regularly.
To Remove Malware From Your Windows PC, Start By Booting Into Safe Mode, Uninstalling Suspicious Programs, And Scanning With Trusted Anti-malware Tools Like Malwarebytes. Clear Temporary Files, Reset Your Network Settings, And Check Startup Apps For Anything Unusual.
For web Browsers, Remove Unwanted Extensions, Reset Browser Settings, Clear Cache And Cookies, And Ensure Your Homepage And Search Engine Haven’t Been Hijacked. Use Cleanup Tools Like Chrome Cleanup Or Browser Guard For Added Protection.
?? Prevention Tips: Keep Software Updated, Avoid Suspicious Downloads, And Use Antivirus Protection Plus Browser Ad Blockers. Regular Backups Are Essential.
Why It Matters: Not All VPNs Offer Malware Protection.
What To Look For: Providers With built-in Malware/ad/tracker Blockers (e.g., NordVPN’s Threat Protection, ProtonVPN’s NetShield).
Purpose: Prevents Data Leaks If Your VPN Connection Drops.
Benefit: Ensures Your Real IP And Browsing Activity Aren’t Exposed To Malware-distributing Websites.
Why It Matters: DNS Leaks Can Expose Your Online Activity To Attackers.
Solution: Enable DNS Leak Protection In Your VPN Settings Or Use A Secure DNS Like Cloudflare (1.1.1.1).
Risk: Free VPNs Often Contain Malware, Sell User Data, Or Lack Security Features.
Better Option: Use Reputable Paid VPNs That Offer security Audits And Transparent Privacy Policies.
Some VPNs Block Known Phishing And Malicious Sites.
Example: Surfshark’s CleanWeb, CyberGhost’s Content Blocker.
Reason: Security Patches Fix Known Vulnerabilities.
Tip: Enable Auto-updates Or Check For Updates Weekly.
Scope: Malware Can Enter Through Phones, Tablets, Or IoT Devices.
Solution: Install VPN Apps On Every Internet-connected Device.
Fact: VPNs Do Not Remove Or Detect Malware On Your System.
Complement It With:
Antivirus Software
Firewall
Browser Extensions For Script Blocking
VPN Encrypts Traffic But Can’t Stop Malware From Executing If You Download Infected Files.
Split Tunneling Allows Certain Apps/sites To Bypass VPN.
Tip: Never Exclude Browsers, Email Clients, Or Download Managers From VPN Tunneling.
A VPN (Virtual Private Network) Enhances Your Online Privacy By Encrypting Your Internet Traffic And Masking Your IP Address. It Protects Your Data On Public Wi-Fi, Hides Browsing Activity From Hackers And ISPs, And Helps Bypass Geo-restrictions. VPNs Also Add A Layer Of Defense Against Malware By Blocking Malicious Websites And Trackers When Using Advanced Features. However, A VPN Does Not Remove Existing Malware Or Act As Antivirus Software. For Full Protection, Combine VPN Use With Antivirus Tools, Regular Software Updates, And Cautious Browsing Habits. Always Choose A Reputable VPN Provider With Strong Security And Privacy Policies.
Dvmap Android Trojan Virus, Dvmap Android Malware Removal Guide, Delete Dvmap Android Trojan Virus, How To Remove Dvmap Android Trojan Virus, Get Rid