 Blog's Page
Blog's Page
Discover How CrimsonRAT Ransomware Is Targeting Indian Institutions And Government Systems. Learn How It Works, Its Impact, And Tips To Stay Protected In 2025.
CrimsonRAT (Remote Access Trojan) Is A Highly Sophisticated Malware Used For Cyber Espionage. Originally Linked To The APT Group **Transparent Tribe**, CrimsonRAT Has Evolved Into A Powerful Surveillance And Data-stealing Tool. Unlike Traditional Ransomware, Which Encrypts Files For Ransom, CrimsonRAT Operates Silently In The Background, Collecting Sensitive Data, Keystrokes, Screenshots, And System Information.
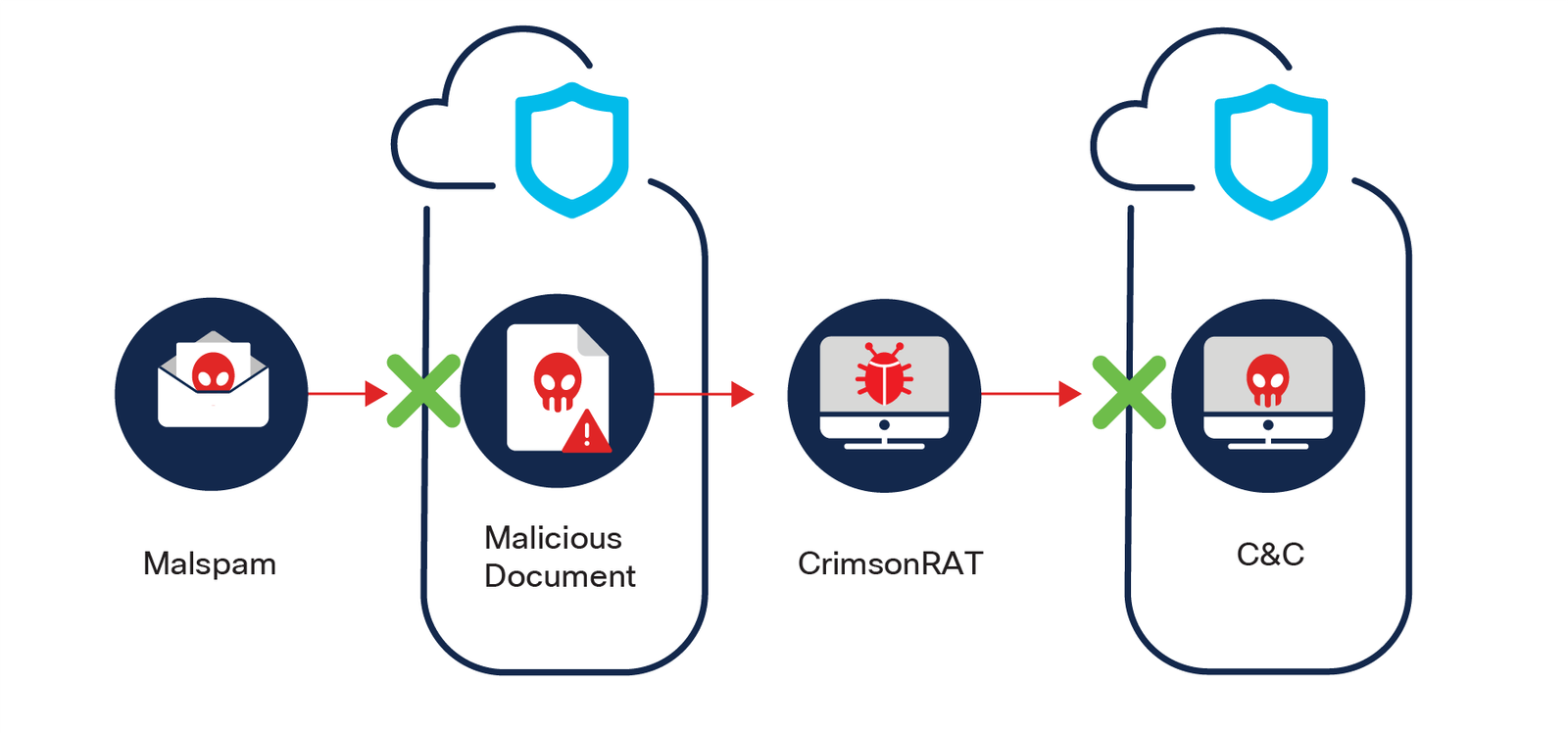
CrimsonRAT Usually Spreads Via Phishing Emails, Malicious Links, Or Fake Software Updates. Once A User Unknowingly Clicks On A Compromised Attachment Or Link, The Malware Silently Installs Itself In The System And Begins Its Surveillance Operations.
Key Capabilities Of CrimsonRAT Include:
Unlike Traditional Ransomware, CrimsonRAT Doesn’t Show Any Visible Ransom Note. Instead, It Quietly Monitors The Infected System, Sending Collected Data To A Remote Command And Control (C2) Server Operated By The Attackers.
CrimsonRAT Has Been Attributed To APT36 (Transparent Tribe) — A Suspected Pakistani State-sponsored Hacking Group. This Group Has Been Active Since 2013 And Is Known For Targeting **Indian Military, Government Institutions, And Educational Entities.
In 2024 And 2025, Multiple Cybersecurity Firms Reported Increased Activity Linked To CrimsonRAT In India. Victims Included Defense Contractors, Academic Research Centers, And Government Officials.
CrimsonRAT Is Especially Dangerous Due To Its Focus On Espionage And Intelligence Gathering. The Malware Can Remain Undetected For Weeks Or Months, Silently Stealing Confidential Files, Login Credentials, And Government Communications.
Recent Attacks Have Led To:
These Cyber-attacks Have Raised Concerns About National Cybersecurity Policies And The Urgent Need For Endpoint Protection.
To Safeguard Against CrimsonRAT And Similar Remote Access Trojans, Follow These Cyber Hygiene Practices:
1. Do Not Open Unknown Email Attachments Or Links.
2. Install A Trusted Antivirus Or Anti-malware Software.
3. Keep Operating Systems And Applications Updated.
4. Use Multi-factor Authentication (MFA) Wherever Possible.
5. Educate Employees And Staff About Phishing Attacks.
6. Monitor Unusual Network Traffic And User Behavior.
Organizations Should Deploy EDR (Endpoint Detection And Response) Tools And Consider Conducting Regular Penetration Tests To Identify Vulnerabilities.
CrimsonRAT Is Not Just Another Malware — It’s A National Security Threat With A Focused Mission: Espionage. As India Continues To Digitize Defense And Governance, Threats Like CrimsonRAT Underline The Importance Of Proactive Cybersecurity.
Step 1: Boot Into Safe Mode
Restart Your PC And Press F8 (or Shift + F8 For Some Systems) Before Windows Loads.
Choose Safe Mode With Networking.
Safe Mode Prevents Most Malware From Loading.
Press Win + R, Type appwiz.cpl, And Press Enter.
Sort By Install Date And Uninstall Unknown Or Recently Added Programs.
Use A Trusted Anti-malware Tool:
Malwarebytes – https://www.malwarebytes.com
Screenshot Of Malwarebytes - Visit Links
Microsoft Defender – Built Into Windows 10/11
HitmanPro, ESET Online Scanner, Or Kaspersky Virus Removal Tool
ZoneAlarm Pro Antivirus + Firewall NextGen
VIPRE Antivirus - US And Others Countries, | India
Run A Full Scan And Delete/quarantine Detected Threats.
Win + R, Type temp → Delete All Files.Press Win + R, Type %temp% → Delete All Files.
Use Disk Cleanup: cleanmgr In The Run Dialog.
Go To: C:\Windows\System32\drivers\etc
Open hosts File With Notepad.
Replace With Default Content:
Press Ctrl + Shift + Esc → Open Task Manager
Go To Startup Tab
Disable Any Suspicious Entries.
Open Command Prompt As Administrator.
Run These Commands:
netsh Winsock Reset
netsh Int Ip Reset
ipconfig /flushdns
Unwanted Homepage Or Search Engine
Pop-ups Or Redirects
Unknown Extensions Installed
For Chrome:
Go To: chrome://extensions/
Remove Anything Unfamiliar
For Firefox:
Go To: about:addons → Extensions
Remove Suspicious Add-ons
For Edge:
Go To: edge://extensions/
Uninstall Unknown Add-ons
Chrome:
Go To chrome://settings/reset → "Restore Settings To Their Original Defaults"
Firefox:
Go To about:support → "Refresh Firefox"
Edge:
Go To edge://settings/resetProfileSettings → "Reset Settings"
All Browsers:
Use Ctrl + Shift + Del → Select All Time
Clear Cookies, Cached Files, And Site Data
Make Sure They Are Not Hijacked.
Chrome: chrome://settings/search
Firefox: about:preferences#search
Edge: edge://settings/search
Chrome: chrome://settings/cleanup
Use Malwarebytes Browser Guard For Real-time Browser Protection.
Always Download Software From Trusted Sources.
Keep Windows, Browsers, And Antivirus Updated.
Avoid Clicking Suspicious Links Or Ads.
Use ad Blockers And reputable Antivirus Software.
Backup Your Files Regularly.
To Remove Malware From Your Windows PC, Start By Booting Into Safe Mode, Uninstalling Suspicious Programs, And Scanning With Trusted Anti-malware Tools Like Malwarebytes. Clear Temporary Files, Reset Your Network Settings, And Check Startup Apps For Anything Unusual.
For web Browsers, Remove Unwanted Extensions, Reset Browser Settings, Clear Cache And Cookies, And Ensure Your Homepage And Search Engine Haven’t Been Hijacked. Use Cleanup Tools Like Chrome Cleanup Or Browser Guard For Added Protection.
?? Prevention Tips: Keep Software Updated, Avoid Suspicious Downloads, And Use Antivirus Protection Plus Browser Ad Blockers. Regular Backups Are Essential.
Why It Matters: Not All VPNs Offer Malware Protection.
What To Look For: Providers With built-in Malware/ad/tracker Blockers (e.g., NordVPN’s Threat Protection, ProtonVPN’s NetShield).
Purpose: Prevents Data Leaks If Your VPN Connection Drops.
Benefit: Ensures Your Real IP And Browsing Activity Aren’t Exposed To Malware-distributing Websites.
Why It Matters: DNS Leaks Can Expose Your Online Activity To Attackers.
Solution: Enable DNS Leak Protection In Your VPN Settings Or Use A Secure DNS Like Cloudflare (1.1.1.1).
Risk: Free VPNs Often Contain Malware, Sell User Data, Or Lack Security Features.
Better Option: Use Reputable Paid VPNs That Offer security Audits And Transparent Privacy Policies.
Some VPNs Block Known Phishing And Malicious Sites.
Example: Surfshark’s CleanWeb, CyberGhost’s Content Blocker.
Reason: Security Patches Fix Known Vulnerabilities.
Tip: Enable Auto-updates Or Check For Updates Weekly.
Scope: Malware Can Enter Through Phones, Tablets, Or IoT Devices.
Solution: Install VPN Apps On Every Internet-connected Device.
Fact: VPNs Do Not Remove Or Detect Malware On Your System.
Complement It With:
Antivirus Software
Firewall
Browser Extensions For Script Blocking
VPN Encrypts Traffic But Can’t Stop Malware From Executing If You Download Infected Files.
Split Tunneling Allows Certain Apps/sites To Bypass VPN.
Tip: Never Exclude Browsers, Email Clients, Or Download Managers From VPN Tunneling.
A VPN (Virtual Private Network) Enhances Your Online Privacy By Encrypting Your Internet Traffic And Masking Your IP Address. It Protects Your Data On Public Wi-Fi, Hides Browsing Activity From Hackers And ISPs, And Helps Bypass Geo-restrictions. VPNs Also Add A Layer Of Defense Against Malware By Blocking Malicious Websites And Trackers When Using Advanced Features. However, A VPN Does Not Remove Existing Malware Or Act As Antivirus Software. For Full Protection, Combine VPN Use With Antivirus Tools, Regular Software Updates, And Cautious Browsing Habits. Always Choose A Reputable VPN Provider With Strong Security And Privacy Policies.
CrimsonRAT, CrimsonRAT Ransomware, CrimsonRAT India 2025, APT36 Transparent Tribe, Remote Access Trojan, Indian Cybersecurity Threats, Malware In Indi