 Blog's Page
Blog's Page

Security Researchers Have Identified A New malware Threat Known As The Wuxia Ransomware, Linking Its Underlying Code To The VoidCrypt Ransomware Family. Once Infected, Victims Of Wuxia Ransomware Find Themselves Unable To Access A Vast Array Of Files On Their Compromised Devices, As The Malware Employs A Robust Encryption Routine Targeting Numerous File Types. The Attackers' Objective Is To Extort Money From Affected Users By Promising To Restore The Encrypted Files Upon Payment.
Wuxia's Encryption Process Includes A Notable Alteration Of The Original File Names. The Malware Appends A Victim's ID, An Email Address ('hushange_delbar@outlook.com'), And A New File Extension ('.wuxia'). Additionally, It Delivers A Ransom Note To The Victims, Providing Instructions On The Decryption Process. Wuxia Ransom-demanding Message Is Presented In A Text File Named 'Decryption-Guide.txt' And Displayed In A Pop-up Window Through A File Named 'Decryption-Guide.hta.'
This Development Underscores The Evolving Threat Landscape, With Wuxia Demonstrating Sophisticated Encryption Techniques And A Connection To The VoidCrypt Ransomware Family.
As A Response, Users And Organizations Are Advised To Prioritize Robust Cybersecurity Measures, Including Regular Backups, Up-to-date Security Software, And Awareness Of Potential Phishing Attempts. Additionally, Refraining From Paying Ransoms And Seeking Assistance From Cybersecurity Experts Are Crucial Steps In Mitigating The Impact Of Such Ransomware Threats.
The Full Text Of The Note Is:
'Your Files Are Has Been Locked
Your Files Has Been Encrypted With Cryptography Algorithm
If You Need Your Files And They Are Important To You, Dont Be Shy Send Me An Email
Send Test File + The Key File On Your System (File Exist In C:/ProgramData Example : KEY-SE-24r6t523 Or RSAKEY.KEY) To Make Sure Your Files Can Be Restored
Make An Agreement On Price With Me And Pay
Get Decryption Tool + RSA Key AND Instruction For Decryption Process
Attention:
1- Do Not Rename Or Modify The Files (You May Loose That File)
2- Do Not Try To Use 3rd Party Apps Or Recovery Tools ( If You Want To Do That Make An Copy From Files And Try On Them And Waste Your Time )
3-Do Not Reinstall Operation System(Windows) You May Loose The Key File And Loose Your Files
4-Do Not Always Trust To Middle Mans And Negotiators (some Of Them Are Good But Some Of Them Agree On 4000usd For Example And Asked 10000usd From Client) This Was Happened
Your Case ID : -
Our Email:Hushange_delbar@outlook.com.'
The Pop-up Window And Accompanying Text File Display Identical Messages, Emphasizing The Impossibility Of Restoring Encrypted Files Without The Assistance Of The Attackers. Victims Are Directed To Establish Contact With The Hackers Via The Email Address 'Hushange_delbar@outlook.com,' Which Is Also Embedded In The File Names. The Message Instructs Affected Users To Provide Two Specific Files: One Encrypted File For The Hackers To Test Their Decryption Capabilities And Another Containing A Crucial Key.
The Note Specifies That The Key File Should Be Located In The C:/ProgramData Folder And Must Be Named Either 'KEY-SE-24r6t523' Or 'RSAKEY.KEY.' Upon Contacting The Hackers, Victims Will Receive Information About The Ransom Amount Required To Obtain The Decryption Tool And The RSA Decryption Key.
The Latter Part Of The Ransom Message Issues Multiple Warnings, Cautioning Victims Against Using Third-party Tools To Attempt File Unlocking. It Strongly Advises Against Engaging Firms Offering Negotiation Services, As Such Actions May Result In Additional Financial Costs For The Victim.
This Underscores The Hackers' Intent To Maintain Control Over The Decryption Process And Discourage Any Attempts To Bypass Their Specified Communication Channels Or Seek Alternative Solutions. As A Response, Affected Individuals And Organizations Should Prioritize Engaging With Cybersecurity Experts And Law Enforcement Agencies To Explore Lawful And Effective Strategies For Mitigating The Impact Of Such Ransomware Attacks.
This Black Friday VPN Deals 2023, Fortify Your Online Security With Exclusive VPN Deals! Unlock Discounts On Top-tier Services, Ensuring Private And Unrestricted Internet Access. Black Friday VPN Deals 2023, Browse Anonymously, Safeguard Sensitive Data, And Enjoy Seamless Streaming With Lightning-fast Speeds. Don't Miss Out On These Limited-time Offers—invest In Your Digital Privacy This Black Friday VPN Deals 2023 And Enjoy A Safer Online Experience. Read More...
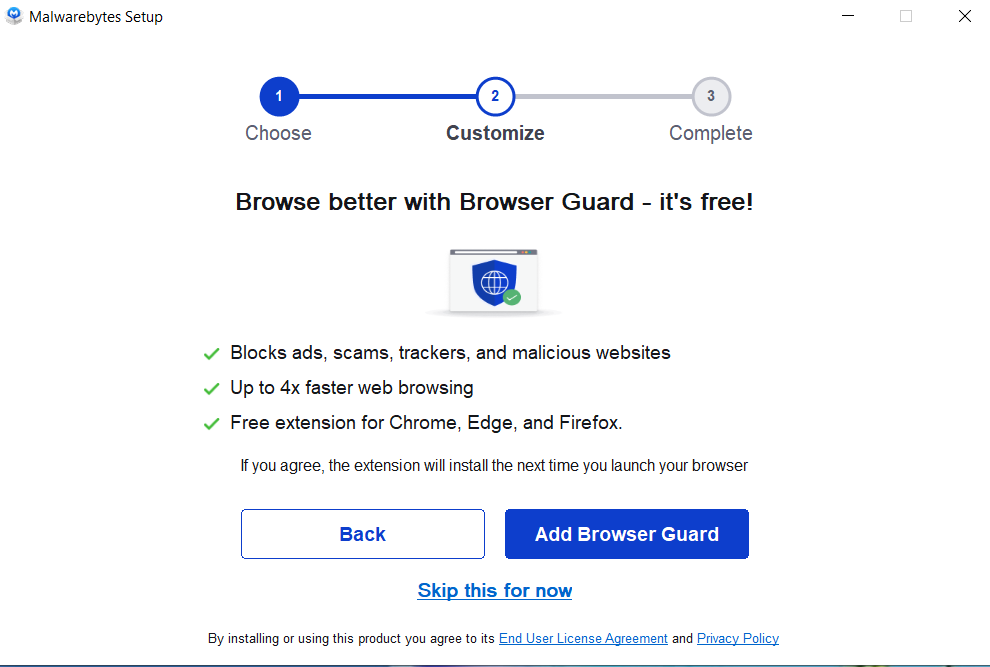
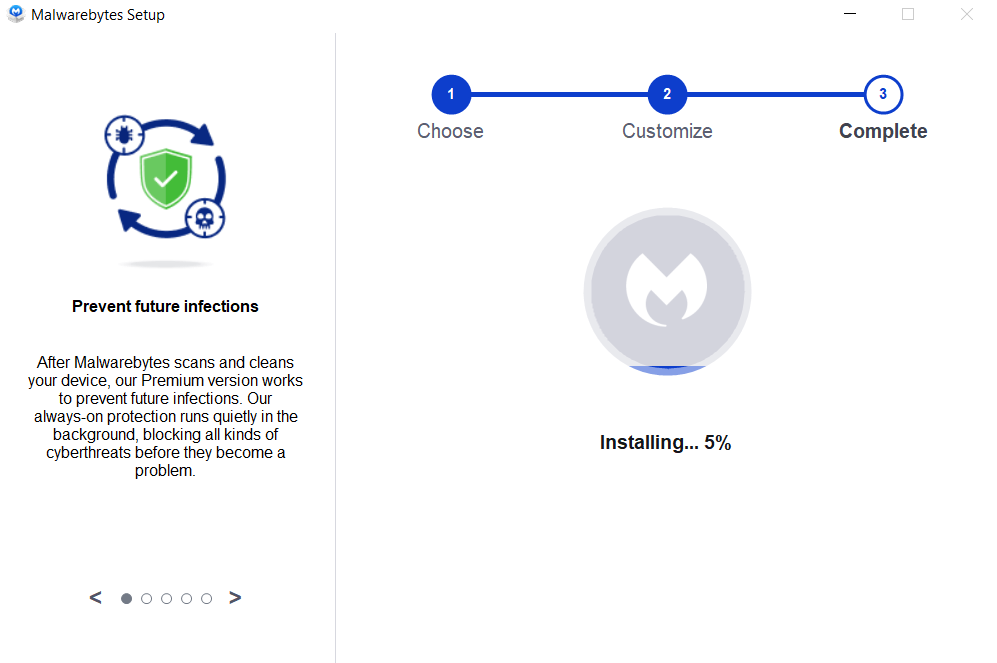
Removing Malware From A Windows Computer Involves A Combination Of Using Antivirus Or Anti-malware Tools, Performing System Scans, And Taking Manual Actions To Eliminate The Malicious Software. Here's A Step-by-step Guide:
Ctrl + Shift + Esc To Open Task Manager.Win + R To Open The Run Dialog, Type cleanmgr, And Press Enter.Remember To Maintain Good Security Practices, Such As Keeping Your Operating System And Software Up-to-date, Using A Reputable Antivirus Program, And Being Cautious When Clicking On Links Or Downloading Files From The Internet. Regularly Backing Up Your Important Data Is Also Crucial To Mitigate The Impact Of Potential Infections.
If You Have Malwarebytes Installed On Your Computer And It Has Detected Malware, Follow These Steps To Remove The Malware:
Open Malwarebytes:
Update Malwarebytes:
Run A Threat Scan:
Review Scan Results:
Quarantine Or Remove Threats:
Reboot Your Computer:
Check For Persistence:
Monitor For Issues:
Clear Browser Data:
Reset Browser Settings:
Review Installed Programs:
Change Passwords:
Update Operating System:




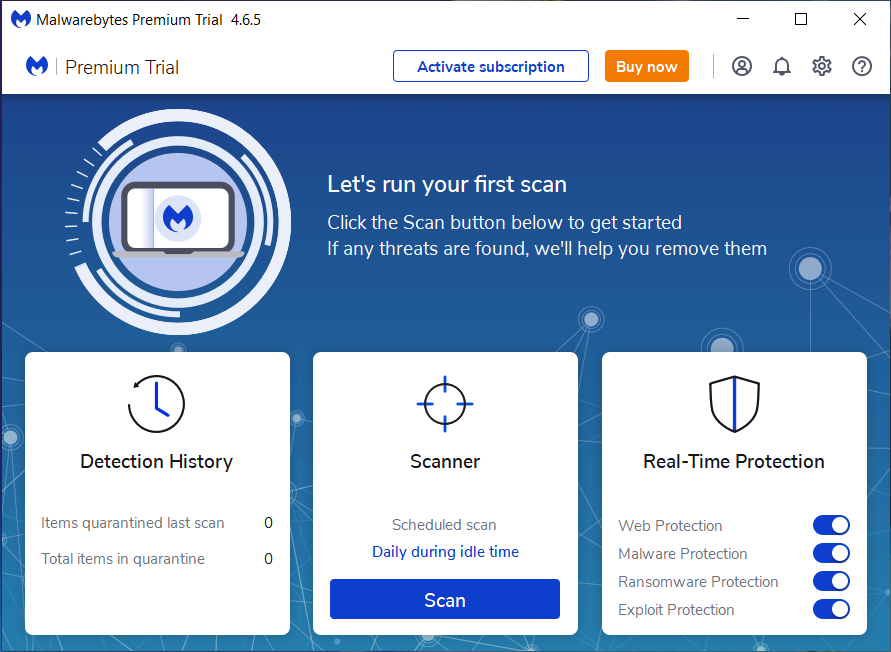
If The Malware Persists Or If You Encounter Difficulties During The Removal Process, You May Want To Seek Assistance From The Malwarebytes Support Community Or Consider Running Additional Scans Using Other Reputable Antivirus Or Anti-malware Tools. Remember To Keep Your Security Software Updated And Practice Safe Computing Habits To Minimize The Risk Of Future Infections.
Malwarebytes Is A Leading Cybersecurity Solution Dedicated To Protecting Users From The Ever-evolving Landscape Of Digital Threats. With A Proven Track Record In Malware Detection And Removal, Malwarebytes Offers Cutting-edge Technology To Safeguard Computers And Devices Against Viruses, Ransomware, And Other Malicious Software.
Boasting A User-friendly Interface, Malwarebytes Provides A Seamless Experience For Both Novice And Advanced Users. Its Real-time Protection Capabilities, Coupled With Powerful Scanning Algorithms, Ensure That Users Are Shielded From The Latest Cybersecurity Threats. Malwarebytes Continually Updates Its Extensive Malware Database, Enabling Users To Stay Ahead Of Emerging Risks And Vulnerabilities.
Beyond malware Detection, Malwarebytes Offers Additional Features Such As Web Protection And Anti-exploit Technology, Fortifying Defenses Against Malicious Websites And Zero-day Exploits. The Software's Lightweight Footprint Ensures Minimal Impact On System Performance, Delivering Robust Security Without Compromising Speed.
Whether Used As A Standalone Solution Or In Conjunction With Other Cybersecurity Tools, Malwarebytes Remains A Trusted Ally In The Battle Against Cyber Threats. As A Proactive And Responsive Cybersecurity Partner, Malwarebytes Empowers Users To Navigate The Digital World With Confidence, Knowing That Their Data And Devices Are Safeguarded Against The Latest And Most Sophisticated Threats.
Wuxia Ransomware, Remove Wuxia Ransomware, Uninstall Wuxia Ransomware, Delete Wuxia Ransomware, Wuxia Ransomware Removal