 Blog's Page
Blog's Page

Emerging In Late 2019, The PwndLocker ransomware Has Swiftly Made A Substantial Impact, Notably With Unprecedented Ransom Demands For Specific Targets. This Sophisticated Malware Has Strategically Targeted Business And Local Government Networks, Levying Ransom Demands Surpassing $650,000. The Scale And Audacity Of PwndLocker's Operations Underscore The Severity And Financial Implications It Poses To Its Victims Within A Relatively Short Timeframe.
PwndLocker Is A Type Of Ransomware That Came To Public Attention In Late 2019. Ransomware Is A Malicious Software That Encrypts A User's Files Or System, Rendering Them Inaccessible, And Demands A Ransom, Often In Cryptocurrency, For The Decryption Key.
PwndLocker, Like Many Ransomware Variants, Targets Businesses And Organizations, Encrypting Their Files And Demanding Significant Ransom Payments For Their Release. The Specific Details, Features, And Activities Of PwndLocker May Evolve Over Time As Cyber Threats Continually Adapt.
It's Crucial To Stay Informed About The Latest Cybersecurity Developments And Utilize Up-to-date Security Measures To Mitigate The Risks Associated With Ransomware And Similar Threats.
PwndLocker Exhibits A Multifaceted Approach To File Encryption, Disabling Critical Windows Services Such As Backup Exec And Microsoft SQL Server. It Goes Further By Attempting To Erase Shadow Volume Copies, Impede Antivirus Functionality, And Target Processes Associated With Microsoft Office And Firefox.
Following This Setup, PwndLocker Executes File Encryption As Per Its Programming And Generates A Ransom Note. The Note Instructs Victims On How To Pay The Ransom To Obtain The Decryption Tool For File Restoration.
The Ransom Demand Varies Based On The Network Or Company Size, With Victims Directed To Contact Cybercriminals Via A Specified Email Address For File Restoration. Failure To Pay Within Two Days Results In An Increased Ransom Amount, Doubling After Two Weeks. Notably, The Decryption Key Is Deleted After A Month, Rendering Files Permanently Unrecoverable.
Hackers, Asserting Access To Sensitive Information, Threaten Victims With Its Dissemination On Social Media If The Ransom Remains Unpaid. To Ascertain The Required Payment, Victims Must Use The Tor Browser To Access A Designated Website.
PwndLocker Ransom Note: Decrypting Your Files
Your Network Have Been Penetrated And Encrypted With A Strong Algorythm
Backups Were Either Removed Or Encrypted
No One Can Help You To Recover The Network Except Us
Do Not Share This Link Or Email. Otherwise, We Will Have To Delete The Decryption Keys.
To Get Your Files Back You Have To Pay The Decryption Fee In BTC.
The Price Depends On The Network Size, Number Of Employees, And Annual Revenue.
Download TOR-Browser: Https://www.torproject.org/download
Login Ax3spapdymip4jpy.onion Using Your ID XXXX
Or
Contact Our Support By Email Xxx@xxx.com
You’ll Receive Instructions Inside.
You Should Get In Touch With Us Within 2 Days After You Noticed The Encryption To Have A Good Discount.
The Decryption Key Will Be Stored For 1 Month.
The Price Will Be Increased By 100% In Two Weeks.
We Also Have Gathered Your Sensitive Data.
We Would Share It In Case You Refuse To Pay.
Do Not Rename Or Move Encrypted Files.
Decryption Using Third-party Software Is Impossible.
Attempts To Self-decrypting Files Will Result In Loss Of Your Data.
Security Experts Consistently Advise Against Paying Attackers As There's No Assurance Of File Restoration, And The Removal Of Ransomware Isn't Guaranteed. These Malicious Programs Are Designed To Persist On Computers, Leaving The Possibility Of A New Infection. Relying On Payment Doesn't Ensure A Comprehensive Resolution To The Ransomware Threat.
PwndLocker Lacks A Specific Infection Method, Spreading Through Malicious Downloads, Spam Emails, Illegal Downloads, Fake Updates, And Cracking Tools. Trojans Play A Role In Disseminating Various Viruses And Ransomware. "Spray And Pray" Spam Email Campaigns Aim To Lure Recipients Into Downloading Attachments Containing The Virus. Ransomware Further Proliferates Through Peer-to-peer Sharing, File Hosting Sites, Freeware Downloads, Unofficial Websites, And Third-party Downloaders. Despite Appearing Harmless, These Downloads Install Malware Upon Execution.
Prevent Ransomware By Adhering To Online Best Practices: Avoid Suspicious Email Attachments And Dubious Sources, Keep Software Updated, And Maintain Regular Data Backups For Heightened Security.
Shortly After The Initiation Of The March Campaign Targeting Enterprise Networks With PwndLocker Ransomware And Demanding Ransom Payments Ranging From $175,000 To Over $650,000, Security Researchers Identified A Vulnerability In The Code. Fabian Wosar And Michael Gillespie Successfully Created A Decryptor Exploiting The Weakness, Enabling Victims To Recover Files Without Paying The Ransom.
Post Their Initial Setback, Threat Actors Rectified The Code Flaw, Rebranding The Ransomware As ProLock And Once Again Targeting Corporate Networks. ProLock Is Distributed Through A BMP Image File Named WinMgr.bmp, Stored In C:\ProgramData. This File, Appearing As A Black Screen With White Dots In The Upper Right Corner, Conceals The Ransomware Executable.
Although ProLock Has Been Observed Attacking A Limited Number Of Servers, The Access Method Remains Unknown. Suspected To Exploit Exposed Remote Desktop Services, The Decision To Hide The Ransomware In A BMP File Is Likely Aimed At Evading Detection, Deploying Throughout The Network Using Tools Like PSExec And PowerShell Empire.
Beyond The Bug Fix And Distribution Method, ProLock Mirrors The Methods Observed In PwndLocker Infections. It Eradicates Shadow Volume Copies, Initiates RSA-2048 Encryption On Files, And Appends The .proLock Extension. Notably, Certain File Types And System Files Remain Unencrypted, Displaying A Pattern Akin To PwndLocker.
The ProLock Ransomware Skips The Encryption Of Files In Common Application Folders And Operating System, As Well As The Following Extensions: .exe, .lnk, .dll, .msi, .ini, .ico, .sys, .chm, .lng, .hlf, .ttf, .inf, .bat, .cmd, .bac, .bak, .vhd, .bkf, .wbc, .dsk, .win, and .set.
Once All Other Valuable Files Are Encrypted, The ProLock Ransomware Will Create A Ransom Note In Each Folder That It Has Scanned, Named [HOW TO RECOVER FILES].TXT.
The Ransom Note Contains The Following Text:
Your Files Have Been Encrypted By ProLock Ransomware Using RSA-2048 Algorithm.
[.:Nothing Personal Just Business:.]
No One Can Help You To Restore Files Without Our Special Decryption Tool.
To Get Your Files Back You Have To Pay The Decryption Fee In BTC.
The Final Price Depends On How Fast You Write To Us.
***If You Have Any Problems Connecting Or Using TOR Network:
contact Our Support By Email Check1kyourf1les@protonmail.com
[You'll Receive Instructions And Price Inside]
The Decryption Keys Will Be Stored For 1 Month.
We Also Have Gathered Your Sensitive Data.
We Would Share It In Case You Refuse To Pay.
Decryption Using Third Party Software Is Impossible.
Attempts To Self-decrypting Files Will Result In The Loss Of Your Data.
Every ProLock Ransomware Executable Contains A Predetermined Ransom Amount Assigned To Each Victim. In A Tested Sample, The Demanded Ransom Payment Was Set At 80 Bitcoin, Equivalent To Over $500,000 At The Current Valuation.
Given That Threat Actors Have Addressed Their Encryption Flaw, Rendering Free Decryption Currently Unfeasible, It Is Strongly Recommended To Perform Regular Backups Of Your System Stored On Separate Devices. This Precautionary Measure Becomes Particularly Crucial In Light Of The Ransomware's Evolving Tactics And The Heightened Financial Stakes Involved.
This Black Friday VPN Deals 2023, Fortify Your Online Security With Exclusive VPN Deals! Unlock Discounts On Top-tier Services, Ensuring Private And Unrestricted Internet Access. Black Friday VPN Deals 2023, Browse Anonymously, Safeguard Sensitive Data, And Enjoy Seamless Streaming With Lightning-fast Speeds. Don't Miss Out On These Limited-time Offers—invest In Your Digital Privacy This Black Friday VPN Deals 2023 And Enjoy A Safer Online Experience. Read More...
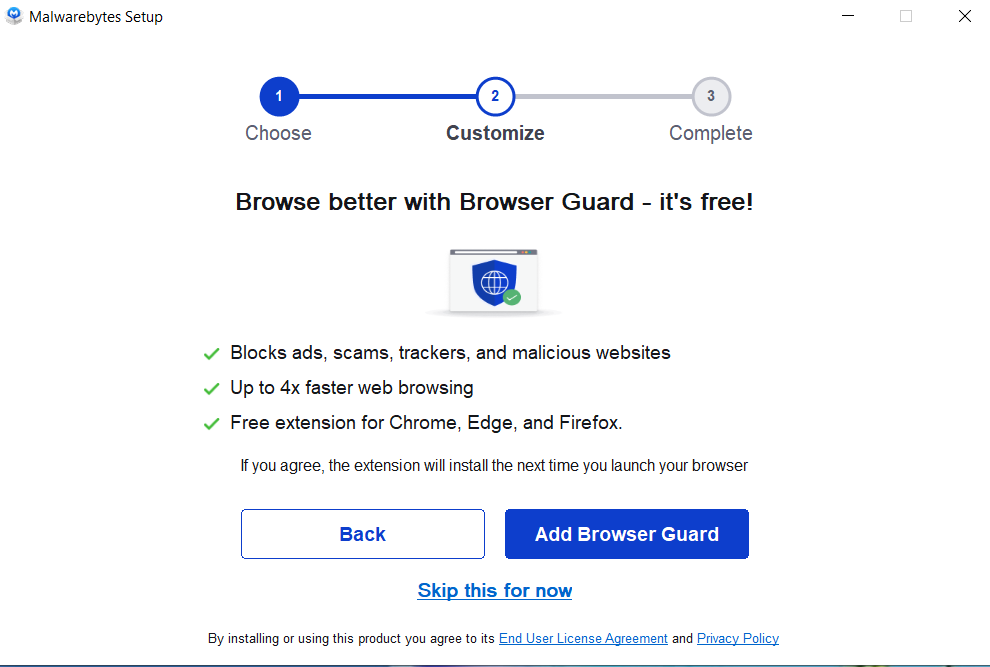
Removing Malware From A Windows Computer Involves A Combination Of Using Antivirus Or Anti-malware Tools, Performing System Scans, And Taking Manual Actions To Eliminate The Malicious Software. Here's A Step-by-step Guide:
Ctrl + Shift + Esc To Open Task Manager.Win + R To Open The Run Dialog, Type cleanmgr, And Press Enter.Remember To Maintain Good Security Practices, Such As Keeping Your Operating System And Software Up-to-date, Using A Reputable Antivirus Program, And Being Cautious When Clicking On Links Or Downloading Files From The Internet. Regularly Backing Up Your Important Data Is Also Crucial To Mitigate The Impact Of Potential Infections.
If You Have Malwarebytes Installed On Your Computer And It Has Detected Malware, Follow These Steps To Remove The Malware:
Open Malwarebytes:
Update Malwarebytes:
Run A Threat Scan:
Review Scan Results:
Quarantine Or Remove Threats:
Reboot Your Computer:
Check For Persistence:
Monitor For Issues:
Clear Browser Data:
Reset Browser Settings:
Review Installed Programs:
Change Passwords:
Update Operating System:



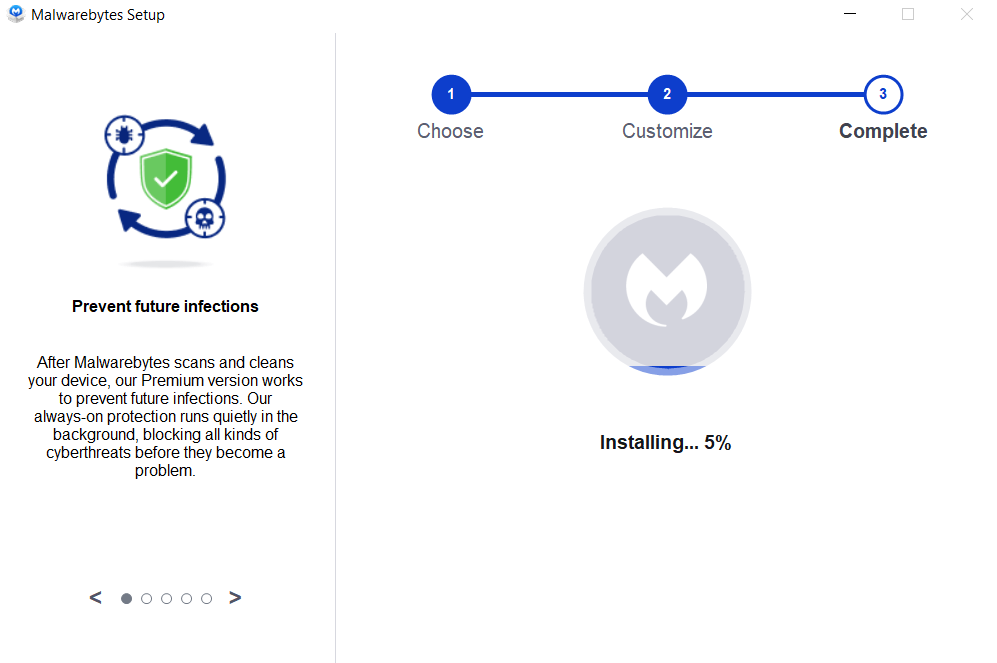
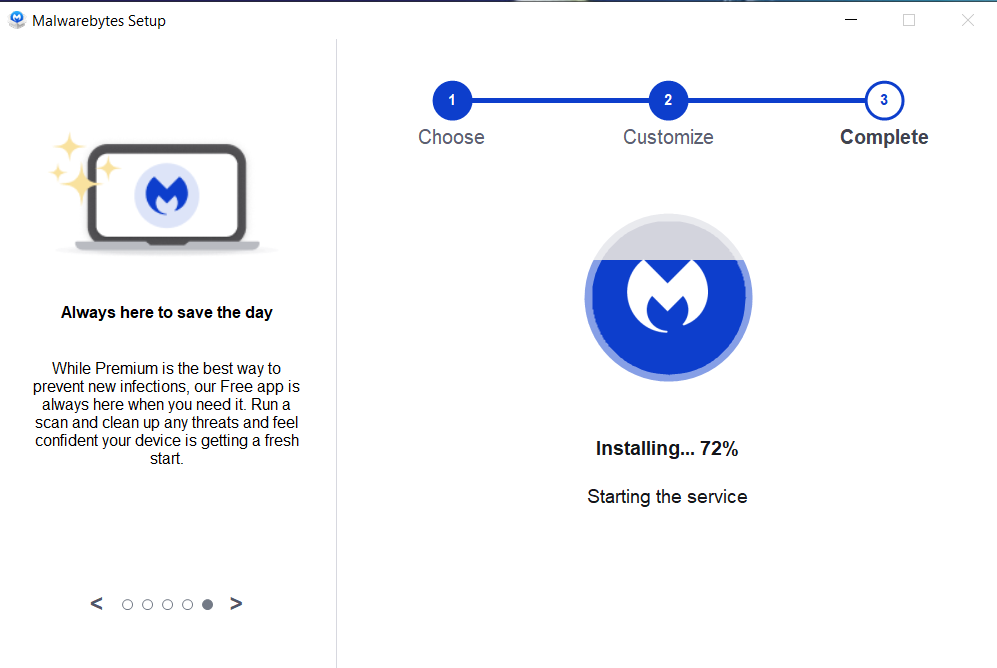

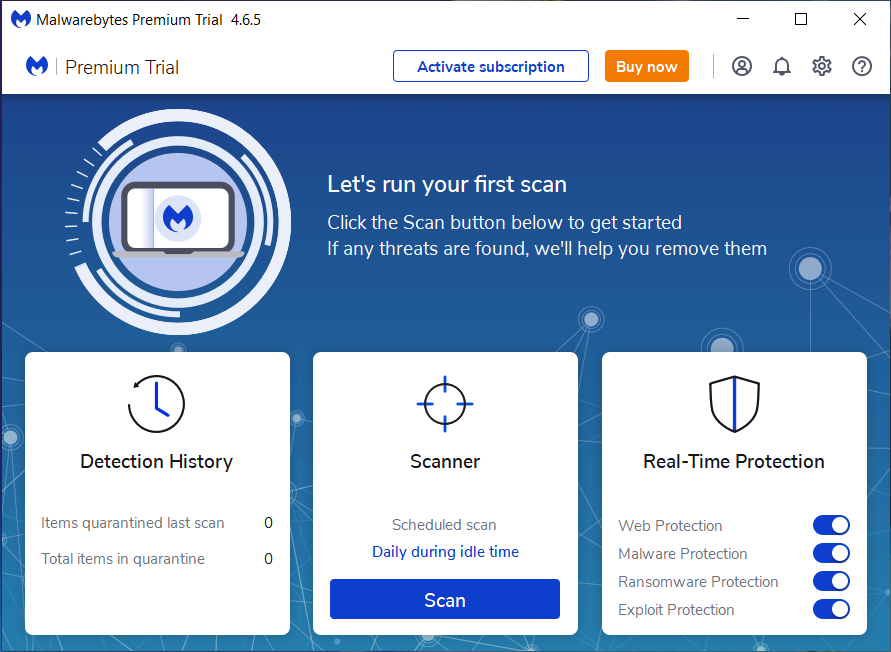
If The Malware Persists Or If You Encounter Difficulties During The Removal Process, You May Want To Seek Assistance From The Malwarebytes Support Community Or Consider Running Additional Scans Using Other Reputable Antivirus Or Anti-malware Tools. Remember To Keep Your Security Software Updated And Practice Safe Computing Habits To Minimize The Risk Of Future Infections.
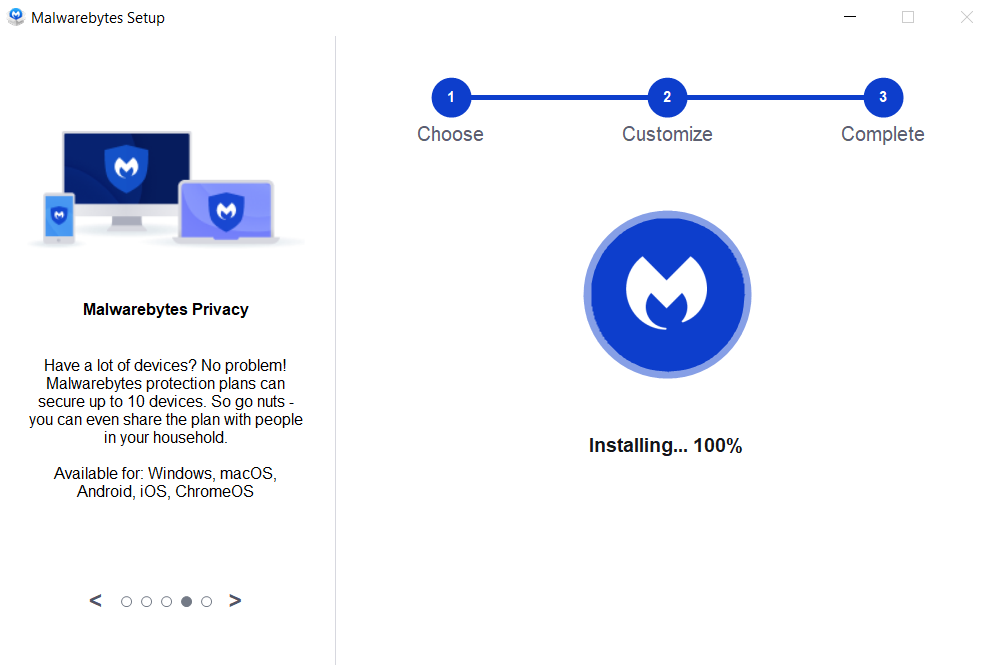
Malwarebytes Is A Leading Cybersecurity Solution Dedicated To Protecting Users From The Ever-evolving Landscape Of Digital Threats. With A Proven Track Record In Malware Detection And Removal, Malwarebytes Offers Cutting-edge Technology To Safeguard Computers And Devices Against Viruses, Ransomware, And Other Malicious Software.
Boasting A User-friendly Interface, Malwarebytes Provides A Seamless Experience For Both Novice And Advanced Users. Its Real-time Protection Capabilities, Coupled With Powerful Scanning Algorithms, Ensure That Users Are Shielded From The Latest Cybersecurity Threats. Malwarebytes Continually Updates Its Extensive Malware Database, Enabling Users To Stay Ahead Of Emerging Risks And Vulnerabilities.
Beyond malware Detection, Malwarebytes Offers Additional Features Such As Web Protection And Anti-exploit Technology, Fortifying Defenses Against Malicious Websites And Zero-day Exploits. The Software's Lightweight Footprint Ensures Minimal Impact On System Performance, Delivering Robust Security Without Compromising Speed.
Whether Used As A Standalone Solution Or In Conjunction With Other Cybersecurity Tools, Malwarebytes Remains A Trusted Ally In The Battle Against Cyber Threats. As A Proactive And Responsive Cybersecurity Partner, Malwarebytes Empowers Users To Navigate The Digital World With Confidence, Knowing That Their Data And Devices Are Safeguarded Against The Latest And Most Sophisticated Threats.
PwndLocker Ransomware, Remove PwndLocker Ransomware, Delete PwndLocker Ransomware, Uninstall PwndLocker Ransomware, Get Rid Of PwndLocker Ransomware| Links1 | Links2 | Links3 | Products | Social Links |
|---|---|---|---|---|
| Home | Blog | Sitemap | Email Checker Tool | |
| About | CSI Links | ISRO Project Code: AA0802 | Offers | |
| Disclaimer | Gallery | Contact Us | Antivirus | |
| Privacy Policy | Software Downloads |