 Blog's Page
Blog's Page

The Ppvw Ransomware Poses A Serious Threat To Software Systems, Employing A Malicious Encryption Process That Renders Data Inaccessible To Its Rightful Owner On Compromised Devices. This Insidious malware Targets A Variety Of File Types, Utilizing A Sophisticated Encryption Routine.
The Malevolent Actors Behind The Ppvw Ransomware Then Demand A Ransom Payment In Exchange For A Decryption Tool That Can Restore Access To The Encrypted Files. This Particular Ransomware Strain Is A New Addition To The Notorious STOP/DJVU Ransomware Family.
What Sets The Ppvw Ransomware Apart From Its Counterparts Within The Same Family Is Its Distinctive Use Of The '.ppvw' File Extension To Identify The Files It Encrypts. In Addition To This Unique Characteristic, The Cybercriminals Responsible For The Ppvw Ransomware Have Been Observed Employing Other Malicious Payloads. Notably, They Deploy The RedLine And Vidar Stealers Alongside Various Iterations Of The STOP/DJVU Ransomware, Enhancing The Overall Threat Level.
Upon Infecting A Device, The Ppvw Ransomware Leaves Its Mark By Appending The '.ppvw' Extension To The Encrypted Files. The Victims Of This Ransomware Attack Then Discover A Ransom Note In The Form Of A Text File Named '_readme.txt.'
The Contents Of This File Provide Instructions On How To Contact The Perpetrators And Proceed With The Ransom Payment Process. The Attackers Capitalize On The Urgency And Critical Nature Of The Situation, Creating A Sense Of Pressure For The Victims To Comply With Their Demands.
It Is Essential To Note That The Ppvw Ransomware Operates Within The Broader Context Of The STOP/DJVU Ransomware Family, Known For Its Destructive Capabilities And Extortion Tactics. The Use Of Distinct File Extensions, Such As '.ppvw,' Serves As A Fingerprint That Allows Security Experts To Identify And Categorize This Specific Variant.
However, The Evolving Nature Of Ransomware Threats Is Evident In The Observed Deployment Of Additional Harmful Payloads Like The RedLine And Vidar Stealers, Indicating A Growing Sophistication In The Attackers' Strategies.
As Organizations And Individuals Face The Increasing Threat Of Ransomware Attacks, It Is Crucial To Prioritize Cybersecurity Measures. This Includes Regular Backups Of Important Data, Implementing Robust Security Protocols, And Staying Informed About Emerging Threats.
Collaborative Efforts Between Cybersecurity Experts And Law Enforcement Agencies Are Essential To Track And Apprehend The Individuals Responsible For Developing And Distributing Such Malicious Software. In The Face Of The Ppvw Ransomware And Its Ilk, A Proactive And Multi-faceted Approach To Cybersecurity Is Paramount To Mitigate The Risks And Potential Damages Associated With These Insidious Attacks.
Victim Loses Their Significant File Due To Ppvw Ransomware
The Ransom Note Associated With The Ppvw Ransomware Contains Critical Information For Its Victims. It Prominently Displays Two Email Addresses, 'support@freshmail.top' And 'datarestorehelp@airmail.cc.'
Victims Are Directed To Contact These Addresses Within A 72-hour Timeframe To Avoid An Increase In The Ransom Amount. Initially Set At $490, The Demanded Payment Doubles To $980 If Victims Fail To Comply Within The Specified Window.
The Note Explicitly Underscores That Without Purchasing The Decryption Software And Obtaining A Unique Key From The Threat Actors, The Encrypted Files Are Irretrievable. While The Ransom Note Mentions A Free Decryption Offer For A Single File, It Cautions That The Selected File Should Not Contain Essential Information.
Exercising Extreme Caution Is Paramount When Dealing With Cybercriminals, As There Is No Assurance That Fulfilling The Payment Will Result In The Receipt Of The Promised Decryption Tools. Consequently, It Is Strongly Recommended To Resist Paying The Ransom, As This Action Does Not Guarantee The Recovery Of Files And May Further Embolden Criminal Activities.
Moreover, Swift Removal Of The Ppvw Ransomware From The Infected Computer Is Imperative To Prevent Additional Data Encryption. Taking Immediate Action To Eliminate The Ransomware Is Critical In Mitigating The Overall Damage Caused By The Attack.
Organizations And Individuals Affected By This Ransomware Should Prioritize Cybersecurity Measures, Seek Assistance From Experts, And Report Such Incidents To Law Enforcement Agencies To Contribute To The Collective Effort Against Cybercrime.
The Ransom Note Left To The Victims Of The Ppvw Ransomware Is:
'ATTENTION!
Don't Worry, You Can Return All Your Files!
All Your Files Like Pictures, Databases, Documents And Other Important Are Encrypted With Strongest Encryption And Unique Key.
The Only Method Of Recovering Files Is To Purchase Decrypt Tool And Unique Key For You.
This Software Will Decrypt All Your Encrypted Files.
What Guarantees You Have?
You Can Send One Of Your Encrypted File From Your PC And We Decrypt It For Free.
But We Can Decrypt Only 1 File For Free. File Must Not Contain Valuable Information.
You Can Get And Look Video Overview Decrypt Tool:
hxxps://we.tl/t-vKvLYNOV9o
Price Of Private Key And Decrypt Software Is $980.
Discount 50% Available If You Contact Us First 72 Hours, That's Price For You Is $490.
Please Note That You'll Never Restore Your Data Without Payment.
Check Your E-mail "Spam" Or "Junk" Folder If You Don't Get Answer More Than 6 Hours.
To Get This Software You Need Write On Our E-mail:
support@freshmail.top
Reserve E-mail Address To Contact Us:
datarestorehelp@airmail.cc
Your Personal ID:'
To Safeguard Your Data And Devices From The Persistent Threat Of Ransomware, It Is Crucial To Implement A Comprehensive Set Of Security Measures. This Approach Involves A Combination Of Proactive Steps, Ongoing Vigilance, And The Adoption Of Robust Security Practices.
Keep Software Updated: Regularly Update Operating Systems, Applications, And Security Software To Address Known Vulnerabilities That Cybercriminals May Exploit To Deliver Ransomware. Timely Application Of Patches And Updates Is Essential For Maintaining A Secure Environment.
Exercise Caution With Emails: Be Cautious When Dealing With Email Attachments, Links, Or Files From Unknown Or Suspicious Sources. Cybercriminals Often Use Phishing Emails To Spread Ransomware. Scrutinize Email Senders, Verify The Authenticity Of Attachments Or Links, And Approach Content From Unverified Sources With Skepticism.
Back Up Data Regularly: Regularly Back Up Important Data To Significantly Reduce The Impact Of A Ransomware Attack. Maintain Offline Or Cloud-based Backups Securely Stored Independently From The Primary System. Periodically Test The Data Restoration Process To Ensure The Integrity Of Backups.
Use Reliable Security Software: Install Reputable Anti-malware Solutions With Ransomware Detection And Prevention Capabilities. These Security Tools Can Identify And Block Known Ransomware Strains, Provide Real-time Protection, And Utilize Behavior-based Detection To Identify Suspicious Activities, Adding An Extra Layer Of Defense.
Limit Administrative Privileges: Minimize The Attack Surface By Restricting Administrative Privileges To Only Those Necessary For Daily Activities. This Helps Mitigate The Impact Of Ransomware Attacks, Preventing Malware From Gaining Extensive Control And Spreading Laterally.
Stay Informed: Educate Yourself About The Latest Ransomware Trends, Attack Techniques, And Prevention Strategies. Stay Informed Through Reputable Sources, Participate In Cybersecurity Awareness Programs, And Familiarize Yourself With Common Indicators Of Ransomware Attacks To Better Recognize And Respond To Potential Threats.
By Consistently Adopting These Comprehensive Security Measures, Users Can Significantly Reduce The Risk Of Falling Victim To Ransomware Attacks. This Proactive Approach Is Instrumental In Protecting Devices And Data From The Potentially Devastating Consequences Associated With Such Threats.
This Black Friday VPN Deals 2023, Fortify Your Online Security With Exclusive VPN Deals! Unlock Discounts On Top-tier Services, Ensuring Private And Unrestricted Internet Access. Black Friday VPN Deals 2023, Browse Anonymously, Safeguard Sensitive Data, And Enjoy Seamless Streaming With Lightning-fast Speeds. Don't Miss Out On These Limited-time Offers—invest In Your Digital Privacy This Black Friday VPN Deals 2023 And Enjoy A Safer Online Experience. Read More...
Removing Malware From A Windows Computer Involves A Combination Of Using Antivirus Or Anti-malware Tools, Performing System Scans, And Taking Manual Actions To Eliminate The Malicious Software. Here's A Step-by-step Guide:
Ctrl + Shift + Esc To Open Task Manager.Win + R To Open The Run Dialog, Type cleanmgr, And Press Enter.Remember To Maintain Good Security Practices, Such As Keeping Your Operating System And Software Up-to-date, Using A Reputable Antivirus Program, And Being Cautious When Clicking On Links Or Downloading Files From The Internet. Regularly Backing Up Your Important Data Is Also Crucial To Mitigate The Impact Of Potential Infections.
If You Have Malwarebytes Installed On Your Computer And It Has Detected Malware, Follow These Steps To Remove The Malware:
Open Malwarebytes:
Update Malwarebytes:
Run A Threat Scan:
Review Scan Results:
Quarantine Or Remove Threats:
Reboot Your Computer:
Check For Persistence:
Monitor For Issues:
Clear Browser Data:
Reset Browser Settings:
Review Installed Programs:
Change Passwords:
Update Operating System:



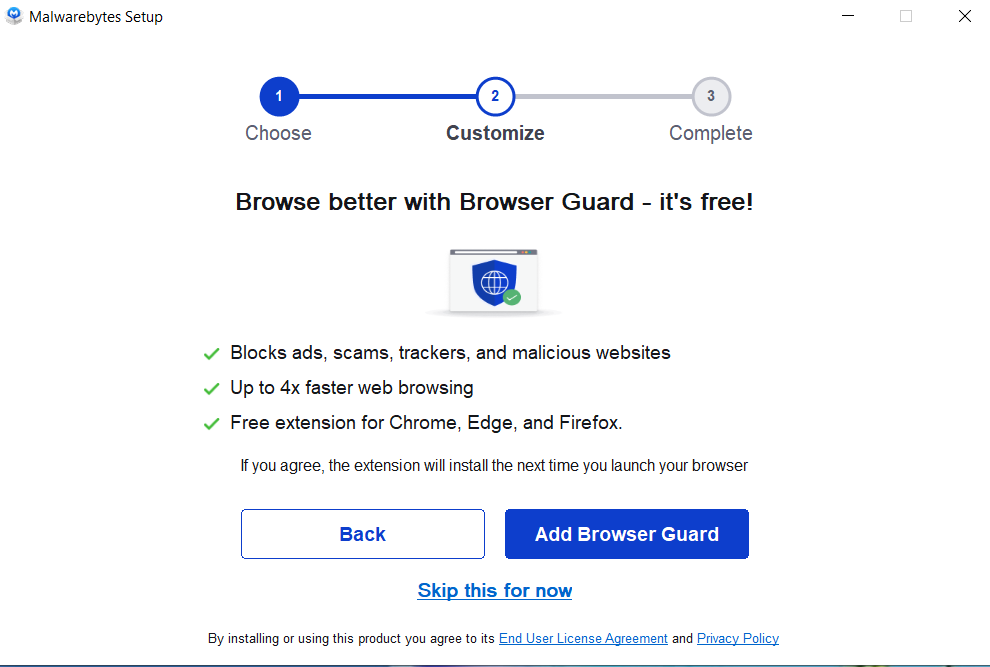
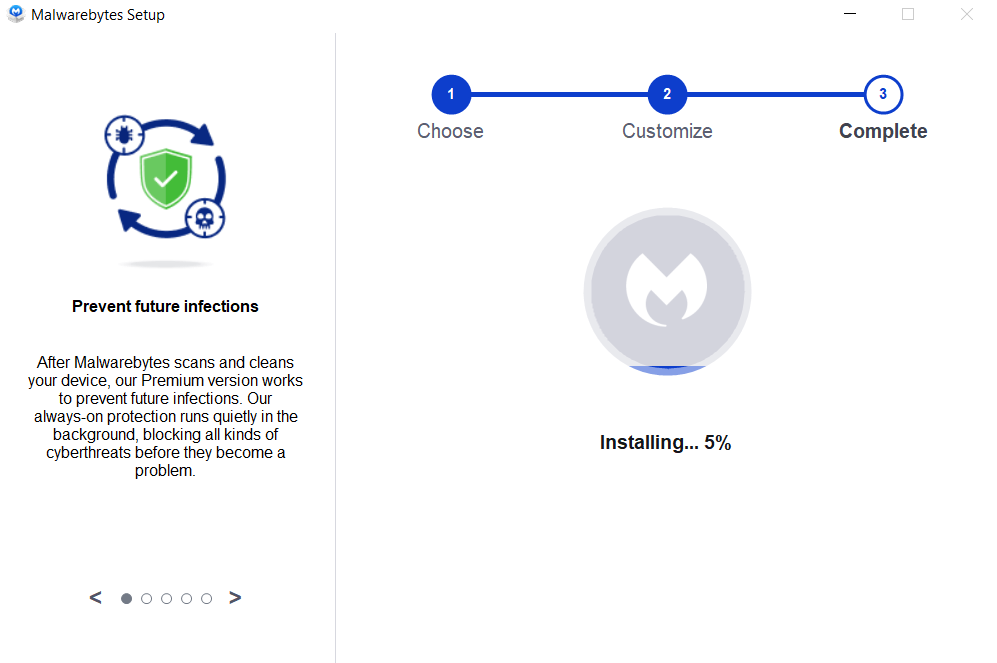
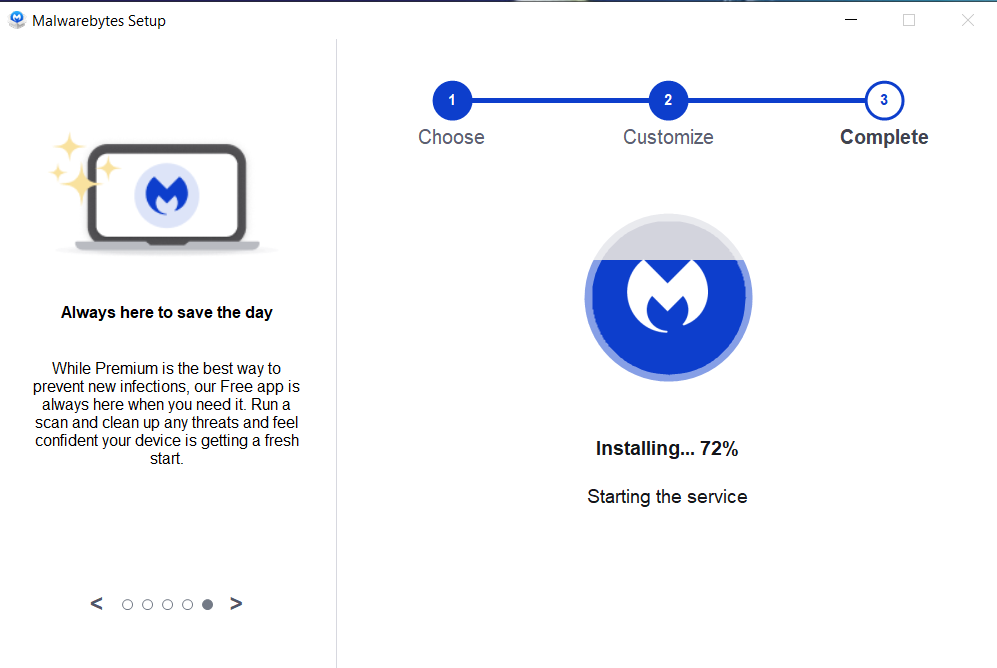
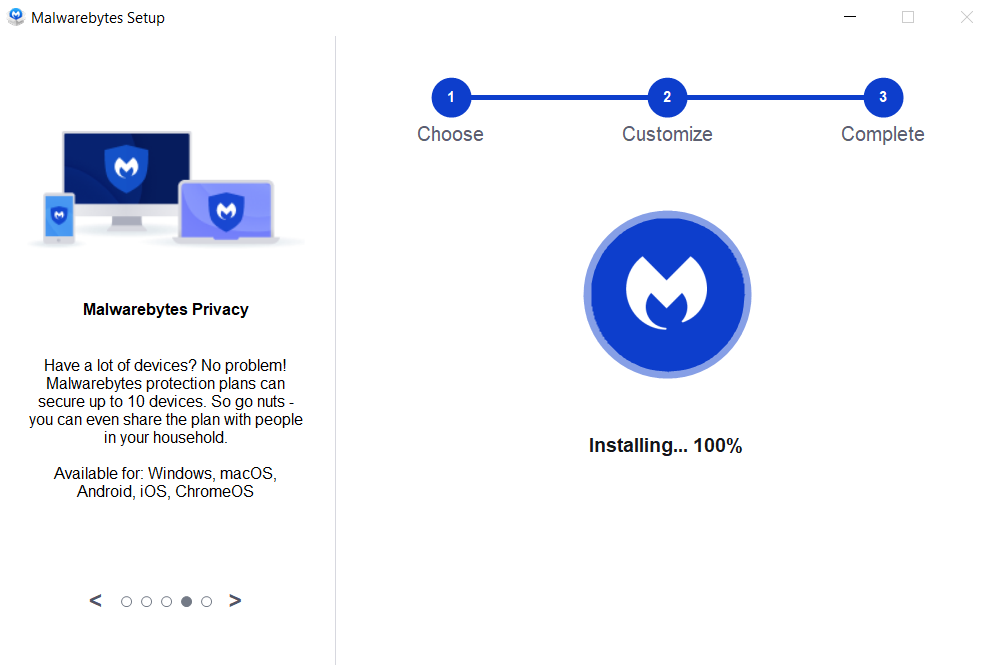

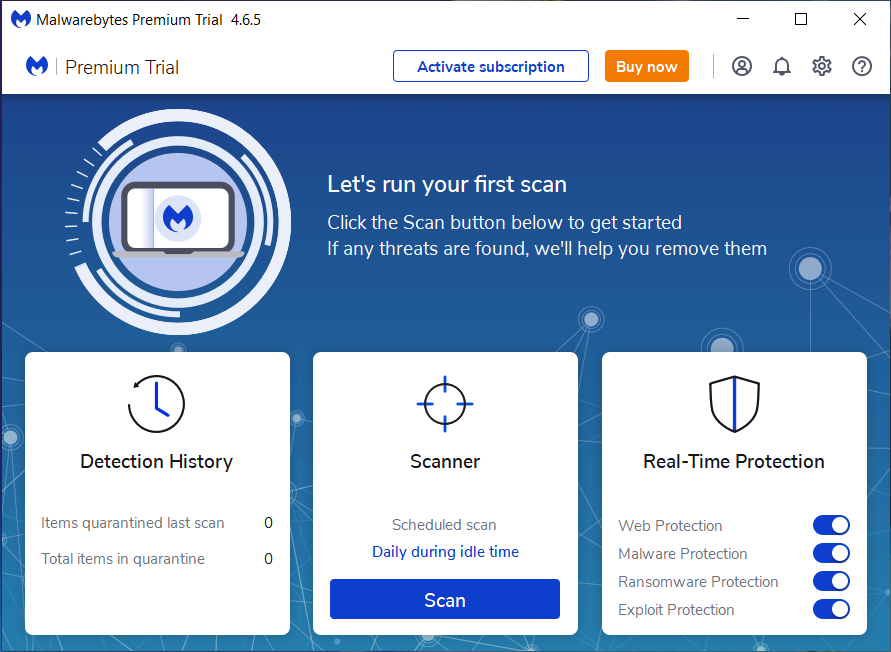
If The Malware Persists Or If You Encounter Difficulties During The Removal Process, You May Want To Seek Assistance From The Malwarebytes Support Community Or Consider Running Additional Scans Using Other Reputable Antivirus Or Anti-malware Tools. Remember To Keep Your Security Software Updated And Practice Safe Computing Habits To Minimize The Risk Of Future Infections.
Malwarebytes Is A Leading Cybersecurity Solution Dedicated To Protecting Users From The Ever-evolving Landscape Of Digital Threats. With A Proven Track Record In Malware Detection And Removal, Malwarebytes Offers Cutting-edge Technology To Safeguard Computers And Devices Against Viruses, Ransomware, And Other Malicious Software.
Boasting A User-friendly Interface, Malwarebytes Provides A Seamless Experience For Both Novice And Advanced Users. Its Real-time Protection Capabilities, Coupled With Powerful Scanning Algorithms, Ensure That Users Are Shielded From The Latest Cybersecurity Threats. Malwarebytes Continually Updates Its Extensive Malware Database, Enabling Users To Stay Ahead Of Emerging Risks And Vulnerabilities.
Beyond malware Detection, Malwarebytes Offers Additional Features Such As Web Protection And Anti-exploit Technology, Fortifying Defenses Against Malicious Websites And Zero-day Exploits. The Software's Lightweight Footprint Ensures Minimal Impact On System Performance, Delivering Robust Security Without Compromising Speed.
Whether Used As A Standalone Solution Or In Conjunction With Other Cybersecurity Tools, Malwarebytes Remains A Trusted Ally In The Battle Against Cyber Threats. As A Proactive And Responsive Cybersecurity Partner, Malwarebytes Empowers Users To Navigate The Digital World With Confidence, Knowing That Their Data And Devices Are Safeguarded Against The Latest And Most Sophisticated Threats.
Ppvw Ransomware, Ppvw Ransomware Removal, Remove Ppvw Ransomware, Uninstall Ppvw Ransomware, Delete Ppvw Ransomware