 Blog's Page
Blog's Page

The 'PacMan' Ransomware Poses A Significant Threat, Designed To Extort Money From Its Victims. 'PacMan' Ransomware Particular Ransomware Variant Has Been Employed In Targeted Attacks Against Danish Chiropractors, Utilizing Highly Specific Phishing Tactics.
Upon Infection, The 'PacMan' Ransomware Actively Disrupts Legitimate Windows Services And Utilities On The Compromised Computer. Operating As A Form Of Crypto-malware, 'PacMan' Ransomware Encrypts The Files Of Its Victims, Rendering Them Inaccessible Until A Ransom Is Paid In Exchange For The Decryption Key.
The Moniker 'PacMan' Ransomware Is Derived From The Online Nickname Of The Threat's Creator, Underscoring The Personalized And Potentially Malicious Nature Of This Cyber Threat.
The 'PacMan' Ransomware Is Disseminated Through Sophisticated Phishing Email Campaigns Leveraging Advanced Social Engineering Techniques. These Deceptive Emails Include An Embedded Link Leading To A Dropbox File, Within Which The 'PacMan' Ransomware Is Concealed.
Clicking On The Link Triggers The Installation Of The 'PacMan' Ransomware On The Victim's Computer. Distinguishing Itself From Other Ransomware Threats, The 'PacMan' Variant Goes Beyond File Encryption.
It Possesses The Ability To Log Keystrokes On The Compromised Computer, Potentially Gathering Sensitive Data, And Disrupts The Settings Of The Affected System. 'PacMan' Ransomware Multifaceted Approach Enhances The Threat's Impact, Underscoring The Importance Of Vigilance Against Such Targeted Cyber Attacks.
Upon Activation On The Victim's Computer, The 'PacMan' Ransomware Initiates The Encryption Process Targeting Files Containing Crucial Information. Microsoft Office Documents, Image Files, Video Game Savers, Database Files, And Various Document Types May Fall Victim To This Encryption.
Once The Encryption Is Complete, The 'PacMan' Ransomware Prominently Displays A Ransom Message On The Victim's Desktop. Notably More Assertive In Its Ransom Demands Compared To Similar Threats, The 'PacMan' Ransomware Explicitly States That Unless The Ransom Is Paid Within 24 Hours, The Files Will Remain Encrypted.
Unfortunately, Decrypting The Affected Files Without The Encryption Key Is Unfeasible. The Primary Defense Against The 'PacMan' Ransomware Involves Proactive Measures Such As Regularly Backing Up Sensitive Files, Practicing Secure Browsing Habits, And Employing Robust Security Software And Protocols To Thwart Potential Threats.
The 'PacMan' Ransomware Has Undergone Analysis By Malware Experts, Revealing Its Development In The .NET Framework. Additionally, Security Analysts Have Identified A Noteworthy Feature: The 'PacMan' Ransomware Incorporates Keylogging Capabilities Alongside Its Encryption Functionality.
Beyond These Capabilities, The Ransomware Takes Preemptive Measures By Terminating Specific Windows Utilities, Including Task Manager, Registry Editor, Terminal, PowerShell, System Restore, Windows Backup, And Msconfig.
'PacMan' Ransomware Deliberate Disabling Of Tools Aims To Hinder Potential Efforts To Remove The 'PacMan' Ransomware From An Infected Computer Or Impede Its Detection And Intervention.
Malware Analysts Strongly Suspect That The Mastermind Behind The 'PacMan' Ransomware Is Likely Based In Denmark. The Messages Affiliated With The 'PacMan' Ransomware Are Impeccably Written In Danish, Employing A Social Engineering Strategy To Exploit Less-experienced Computer Users.
Notably, The 'PacMan' Ransomware Exhibits A Highly Targeted Approach, Meticulously Selecting Its Victims Rather Than Employing A Broad-scale Method. The Adept Execution Of The 'PacMan' Ransomware Attack Has Raised Concerns Among PC Security Researchers, Indicating A Potential High Risk For Additional Attacks.
While The Ransomware Itself Follows A Relatively Standard Pattern, Its Underpinning Social Engineering Approach Suggests That It Might Be Part Of A Broader Campaign Targeting Other Vulnerable Entities In Denmark. The Successful Targeting Of Danish Chiropractors Underscores The Likelihood Of Similar Tactics Being Employed Against Other Businesses And Individuals In Denmark.
Consequently, Malware Analysts Caution Computer Users In Denmark To Remain Vigilant Against Phishing Attacks That Could Serve As A Vector For The Distribution Of The 'PacMan' Ransomware.
This Black Friday VPN Deals 2023, Fortify Your Online Security With Exclusive VPN Deals! Unlock Discounts On Top-tier Services, Ensuring Private And Unrestricted Internet Access. Black Friday VPN Deals 2023, Browse Anonymously, Safeguard Sensitive Data, And Enjoy Seamless Streaming With Lightning-fast Speeds. Don't Miss Out On These Limited-time Offers—invest In Your Digital Privacy This Black Friday VPN Deals 2023 And Enjoy A Safer Online Experience. Read More...
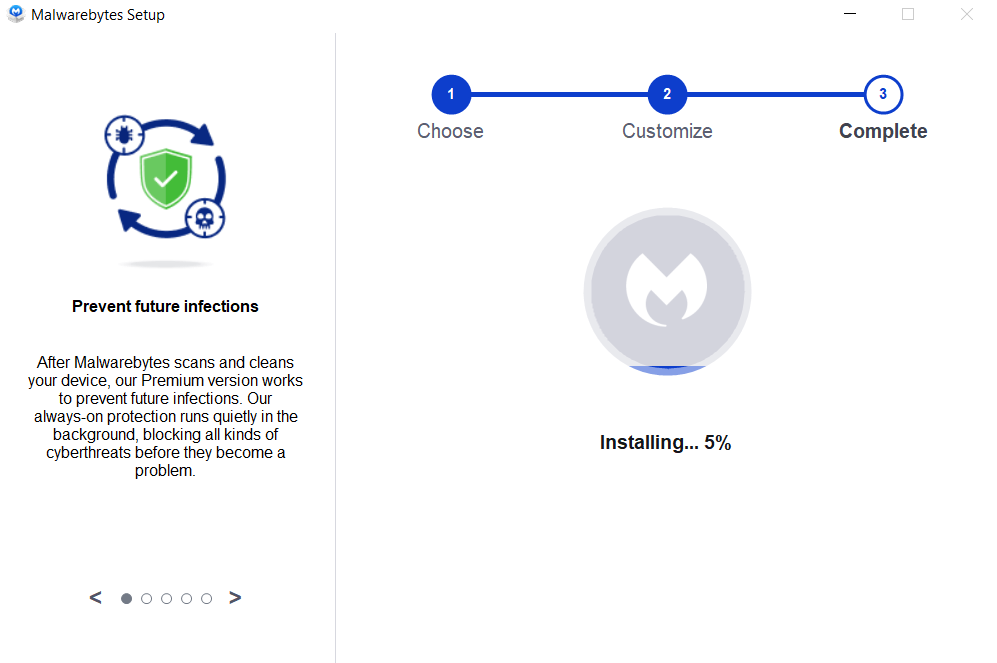
Removing Malware From A Windows Computer Involves A Combination Of Using Antivirus Or Anti-malware Tools, Performing System Scans, And Taking Manual Actions To Eliminate The Malicious Software. Here's A Step-by-step Guide:
Ctrl + Shift + Esc To Open Task Manager.Win + R To Open The Run Dialog, Type cleanmgr, And Press Enter.Remember To Maintain Good Security Practices, Such As Keeping Your Operating System And Software Up-to-date, Using A Reputable Antivirus Program, And Being Cautious When Clicking On Links Or Downloading Files From The Internet. Regularly Backing Up Your Important Data Is Also Crucial To Mitigate The Impact Of Potential Infections.
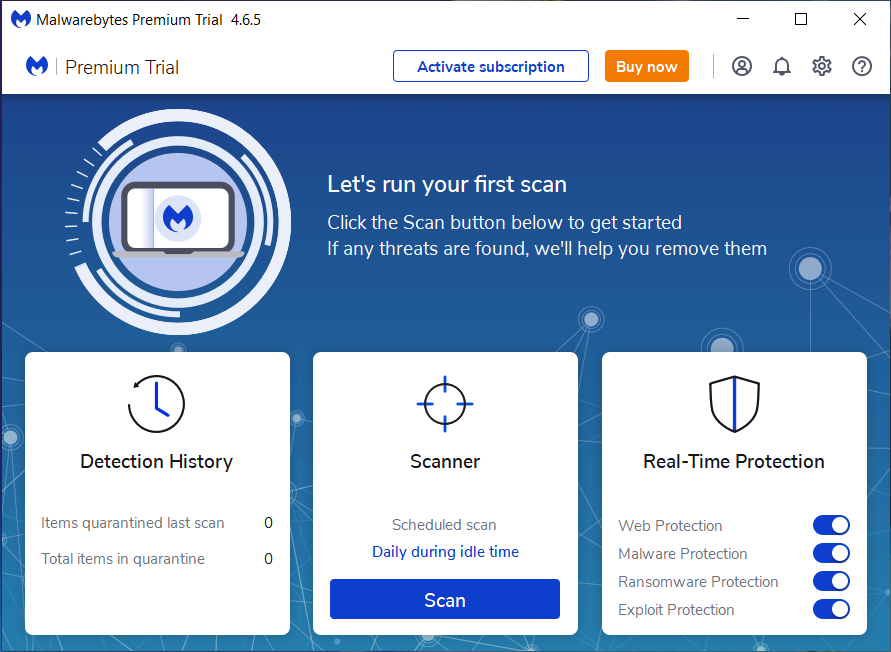
If You Have Malwarebytes Installed On Your Computer And It Has Detected Malware, Follow These Steps To Remove The Malware:
Open Malwarebytes:
Update Malwarebytes:
Run A Threat Scan:
Review Scan Results:
Quarantine Or Remove Threats:
Reboot Your Computer:
Check For Persistence:
Monitor For Issues:
Clear Browser Data:
Reset Browser Settings:
Review Installed Programs:
Change Passwords:
Update Operating System:




If The Malware Persists Or If You Encounter Difficulties During The Removal Process, You May Want To Seek Assistance From The Malwarebytes Support Community Or Consider Running Additional Scans Using Other Reputable Antivirus Or Anti-malware Tools. Remember To Keep Your Security Software Updated And Practice Safe Computing Habits To Minimize The Risk Of Future Infections.
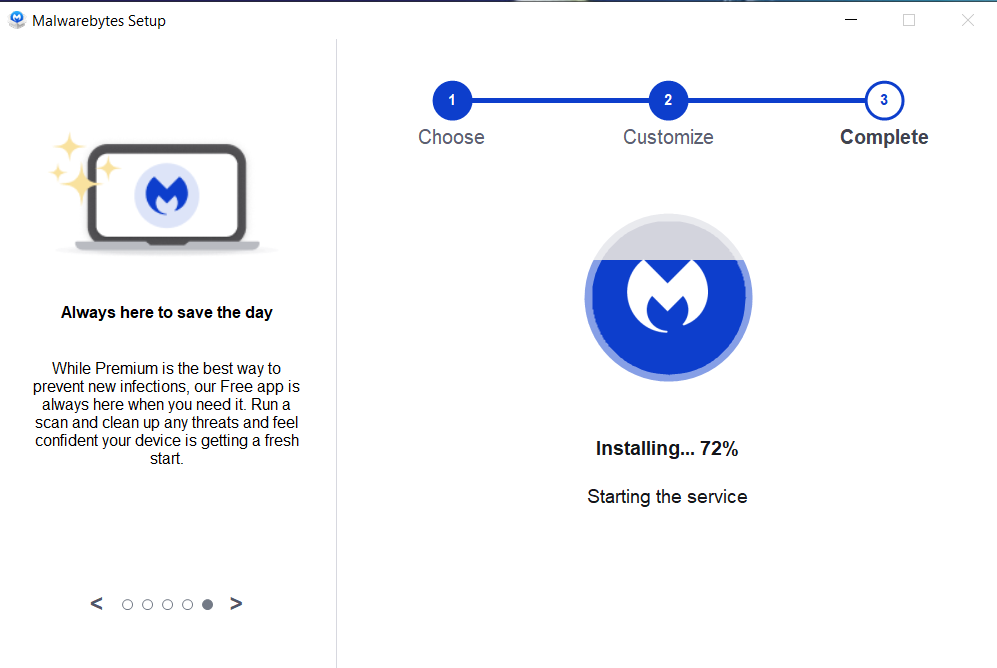
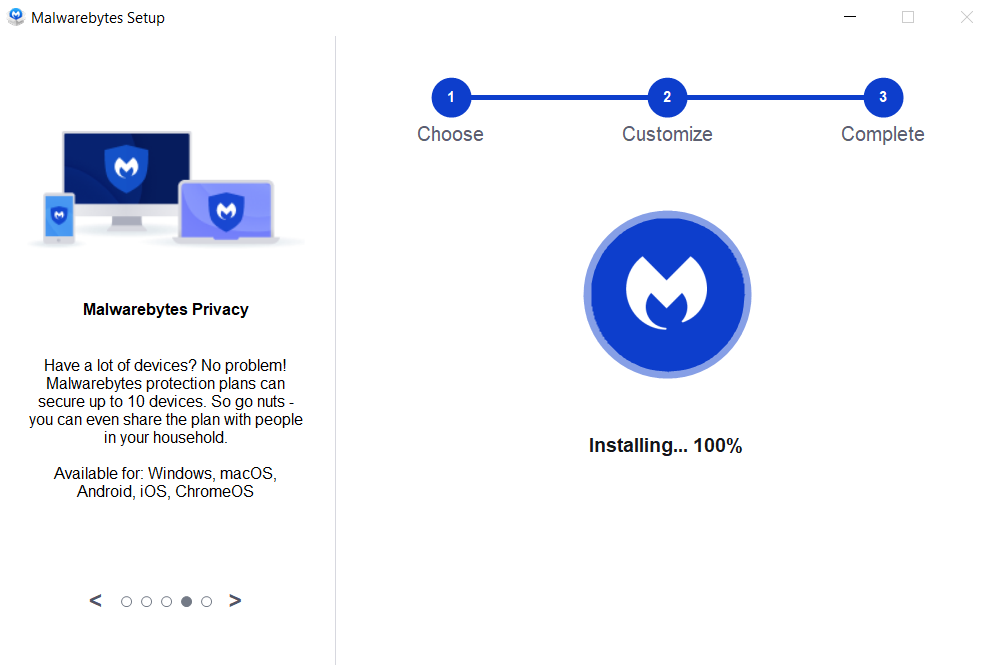
Malwarebytes Is A Leading Cybersecurity Solution Dedicated To Protecting Users From The Ever-evolving Landscape Of Digital Threats. With A Proven Track Record In Malware Detection And Removal, Malwarebytes Offers Cutting-edge Technology To Safeguard Computers And Devices Against Viruses, Ransomware, And Other Malicious Software.
Boasting A User-friendly Interface, Malwarebytes Provides A Seamless Experience For Both Novice And Advanced Users. Its Real-time Protection Capabilities, Coupled With Powerful Scanning Algorithms, Ensure That Users Are Shielded From The Latest Cybersecurity Threats. Malwarebytes Continually Updates Its Extensive Malware Database, Enabling Users To Stay Ahead Of Emerging Risks And Vulnerabilities.
Beyond malware Detection, Malwarebytes Offers Additional Features Such As Web Protection And Anti-exploit Technology, Fortifying Defenses Against Malicious Websites And Zero-day Exploits. The Software's Lightweight Footprint Ensures Minimal Impact On System Performance, Delivering Robust Security Without Compromising Speed.
Whether Used As A Standalone Solution Or In Conjunction With Other Cybersecurity Tools, Malwarebytes Remains A Trusted Ally In The Battle Against Cyber Threats. As A Proactive And Responsive Cybersecurity Partner, Malwarebytes Empowers Users To Navigate The Digital World With Confidence, Knowing That Their Data And Devices Are Safeguarded Against The Latest And Most Sophisticated Threats.
PacMan Ransomware, Remove PacMan Ransomware, Delete PacMan Ransomware, Uninstall PacMan Ransomware, Get Rid Of PacMan Ransomware, PacMan Ransomware Re